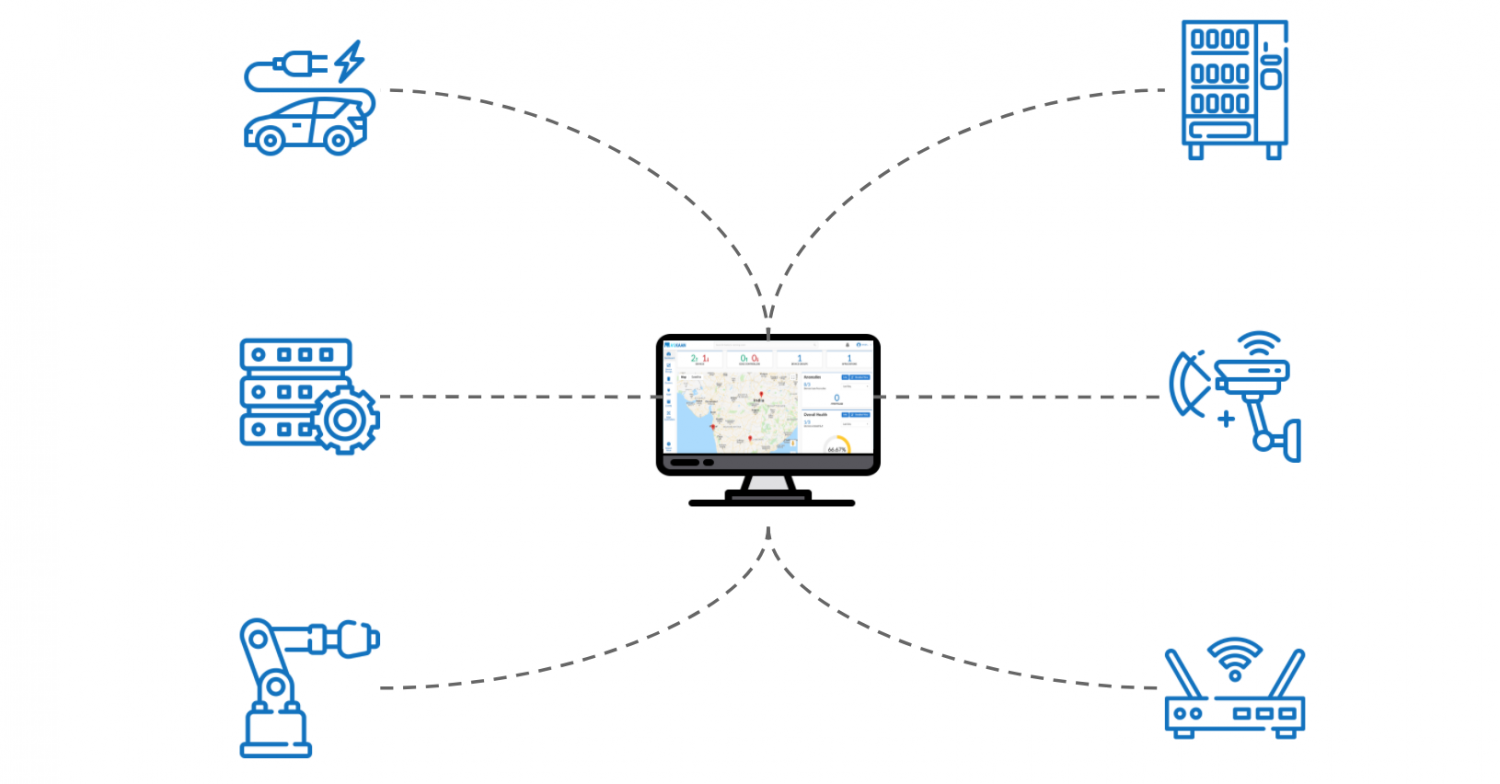
Accessing IoT devices remotely on a Mac without relying on free solutions has become an essential skill for tech enthusiasts and professionals alike. As the Internet of Things (IoT) continues to grow, the ability to manage and control smart devices from a distance is increasingly important. Whether you're managing home automation systems or monitoring industrial equipment, understanding how to securely access IoT devices remotely is crucial.
In today's interconnected world, IoT devices are everywhere, from smart thermostats and security cameras to industrial sensors and medical devices. The convenience of remote access allows users to control these devices from anywhere in the world. However, ensuring secure and reliable connections is paramount, especially when proprietary or paid solutions are required.
This comprehensive guide will walk you through the steps, tools, and best practices for accessing IoT devices remotely on a Mac without using free solutions. By the end of this article, you'll have the knowledge and confidence to set up a secure and efficient remote access system for your IoT devices.
Read also:Jayne Mansfield The Tragic Story Of Her Death And Legacy
Table of Contents
- Introduction to Remote Access for IoT Devices
- Why Security Matters in IoT Remote Access
- Essential Tools for Remote Access
- Step-by-Step Guide to Setup
- Understanding Network Requirements
- Common Issues and Troubleshooting
- Cost Considerations for Paid Solutions
- Best Practices for Secure IoT Remote Access
- Future Trends in IoT Remote Access
- Conclusion and Next Steps
Introduction to Remote Access for IoT Devices
Remote access to IoT devices on a Mac is a powerful capability that enhances productivity and convenience. It allows users to monitor and control devices from anywhere, as long as they have an internet connection. However, achieving this without relying on free solutions requires a deeper understanding of the tools and techniques involved.
Free solutions often come with limitations, such as restricted features, lack of support, and potential security risks. Paid solutions, on the other hand, offer robust features, enhanced security, and reliable customer support. This article focuses on how to access IoT devices remotely on a Mac using paid tools and secure methods.
Whether you're a homeowner managing smart home devices or a professional overseeing industrial equipment, the ability to access IoT devices remotely is a valuable asset. By following the guidelines in this article, you can ensure a seamless and secure remote access experience.
Why Security Matters in IoT Remote Access
Security is a critical consideration when accessing IoT devices remotely. The increasing number of cyber threats targeting IoT devices highlights the importance of implementing robust security measures. Unauthorized access to IoT devices can lead to data breaches, privacy violations, and even physical damage to equipment.
Paid solutions often provide advanced security features, such as encryption, two-factor authentication, and firewalls. These features help protect your devices and data from malicious actors. Additionally, paid solutions typically offer regular updates and patches to address emerging security vulnerabilities.
Here are some key security considerations for IoT remote access:
Read also:Crazyjamjam Fanfic Exploring The World Of Creative Fiction
- Use strong and unique passwords for all devices.
- Enable two-factor authentication whenever possible.
- Regularly update firmware and software to patch vulnerabilities.
- Monitor device activity for any suspicious behavior.
Essential Tools for Remote Access
To access IoT devices remotely on a Mac, you'll need the right tools. While free solutions may seem appealing, they often fall short in terms of security and functionality. Paid tools, on the other hand, offer a wide range of features and support options. Here are some essential tools for remote access:
1. Secure Shell (SSH) Clients
SSH clients enable secure communication between your Mac and IoT devices. They provide encrypted connections, ensuring that your data remains private and secure. Popular SSH clients for Mac include:
- Terminal (built-in Mac application)
- SecureCRT
- PuTTY (via Wine or other compatibility layers)
2. Virtual Private Networks (VPNs)
VPNs create a secure tunnel between your Mac and IoT devices, protecting your connection from eavesdropping and interception. Paid VPN services offer reliable performance and advanced security features. Some popular options include:
- ExpressVPN
- NordVPN
- Private Internet Access (PIA)
Step-by-Step Guide to Setup
Setting up remote access for IoT devices on a Mac involves several steps. Below is a detailed guide to help you through the process:
Step 1: Prepare Your Mac
Before accessing IoT devices remotely, ensure your Mac is properly configured. This includes:
- Installing necessary software and tools.
- Configuring network settings.
- Securing your Mac with strong passwords and encryption.
Step 2: Configure Your IoT Device
Your IoT device must be properly set up for remote access. This involves:
- Connecting the device to a stable internet connection.
- Updating firmware and software to the latest version.
- Configuring security settings, such as enabling encryption and disabling unnecessary services.
Step 3: Set Up a Secure Connection
Establishing a secure connection between your Mac and IoT device is crucial. Use tools like SSH or a VPN to ensure data privacy and integrity. Follow these steps:
- Create an SSH key pair for authentication.
- Configure your router to forward necessary ports.
- Test the connection to ensure it works as expected.
Understanding Network Requirements
Network configuration plays a vital role in remote access. Your Mac and IoT devices must be connected to a stable and secure network. Consider the following network requirements:
- Ensure your internet connection has sufficient bandwidth for remote access.
- Use a static IP address or dynamic DNS service to simplify device access.
- Configure your router's firewall to allow only necessary traffic.
By optimizing your network settings, you can improve the performance and security of your remote access setup.
Common Issues and Troubleshooting
Even with careful planning, issues can arise during remote access. Here are some common problems and their solutions:
- Connection Issues: Check your network settings and ensure all devices are properly connected.
- Security Alerts: Review your security configurations and update them if necessary.
- Performance Problems: Optimize your network and device settings for better performance.
Regularly monitoring and maintaining your remote access setup can help prevent these issues from occurring.
Cost Considerations for Paid Solutions
Paid solutions for remote access come with varying costs, depending on the features and support offered. When evaluating options, consider the following factors:
- Subscription fees and pricing plans.
- Feature set and scalability.
- Customer support and service level agreements (SLAs).
Investing in a reliable paid solution can save you time and money in the long run by providing a secure and efficient remote access experience.
Best Practices for Secure IoT Remote Access
To ensure a secure and reliable remote access setup, follow these best practices:
- Regularly update all devices and software.
- Use strong authentication methods, such as two-factor authentication.
- Monitor device activity and log files for any suspicious behavior.
- Limit access to authorized users only.
By adhering to these practices, you can minimize the risk of security breaches and ensure a smooth remote access experience.
Future Trends in IoT Remote Access
The future of IoT remote access is promising, with advancements in technology and increasing adoption of smart devices. Emerging trends include:
- Improved security protocols and encryption standards.
- Integration with artificial intelligence (AI) and machine learning (ML) for enhanced functionality.
- Increased focus on user-friendly interfaces and seamless connectivity.
As technology continues to evolve, staying informed about the latest trends and innovations will help you make the most of your IoT remote access capabilities.
Conclusion and Next Steps
Accessing IoT devices remotely on a Mac without free solutions requires careful planning and the right tools. By following the guidelines in this article, you can set up a secure and efficient remote access system for your IoT devices. Remember to prioritize security, regularly update your devices, and stay informed about the latest trends in IoT technology.
We encourage you to take action by:
- Leaving a comment with your thoughts or questions.
- Sharing this article with others who may find it useful.
- Exploring other articles on our site for more tips and insights.
Thank you for reading, and happy remote accessing!