SSH remote IoT commands are essential tools for managing and securing Internet of Things (IoT) devices from a distance. As the IoT landscape continues to expand, understanding how to leverage SSH (Secure Shell) for remote device management has become increasingly critical for developers, IT professionals, and system administrators. In this article, we will explore everything you need to know about SSH remote IoT commands, including their applications, best practices, and how to implement them effectively.
Whether you're a beginner or an experienced professional, SSH remote IoT commands provide a secure and reliable way to interact with IoT devices. From configuring sensors to troubleshooting network issues, these commands enable seamless communication between remote systems, ensuring efficient device management and enhanced security.
This article will delve into the core concepts, provide practical examples, and offer actionable tips to help you master SSH remote IoT commands. By the end of this guide, you'll have a comprehensive understanding of how to use SSH for remote IoT device management and optimization.
Read also:William Macy The Journey Of An Esteemed Actor And Director
Table of Contents
- Introduction to SSH Remote IoT Commands
- What is SSH?
- Benefits of Using SSH for IoT
Basic SSH Commands for IoT
Advanced SSH Commands for IoT
- Security Best Practices for SSH Remote IoT Commands
Troubleshooting SSH IoT Connections
- Real-World Applications of SSH in IoT
- Tools and Software for SSH IoT Management
- The Future of SSH in IoT
- Conclusion
Introduction to SSH Remote IoT Commands
SSH remote IoT commands play a pivotal role in modern IoT ecosystems. With the increasing number of connected devices, managing them remotely has become a necessity. SSH provides a secure communication channel, allowing users to execute commands on remote IoT devices without compromising data integrity or security.
Understanding SSH remote IoT commands is vital for anyone involved in IoT development or management. These commands enable administrators to perform tasks such as file transfers, system updates, and device monitoring from any location, provided they have the necessary credentials and network access.
As we dive deeper into this topic, we'll explore the fundamental aspects of SSH, its advantages in IoT environments, and the essential commands required for effective remote device management.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol designed for secure communication over unsecured networks. It provides a robust framework for remote login, command execution, and data transfer between devices. SSH encrypts all data exchanged between the client and server, ensuring confidentiality, integrity, and authentication.
In the context of IoT, SSH serves as a critical tool for managing devices that may be dispersed across various locations. By leveraging SSH remote IoT commands, administrators can securely interact with devices, perform maintenance tasks, and monitor system performance without being physically present.
Some key features of SSH include:
Read also:Anselmo Feleppa Wife Unveiling The Life And Journey Of A Beloved Figure
- End-to-end encryption
- Authentication mechanisms (passwords, keys)
- Support for file transfer protocols (SFTP)
- Command execution capabilities
Benefits of Using SSH for IoT
Using SSH for IoT applications offers numerous advantages that enhance device management and security. Below are some of the primary benefits:
- Enhanced Security: SSH encrypts all communications, protecting sensitive data from unauthorized access.
- Remote Accessibility: Administrators can manage IoT devices from anywhere, streamlining maintenance and troubleshooting processes.
- Automation Capabilities: SSH supports script-based automation, enabling repetitive tasks to be executed efficiently.
- Scalability: SSH can handle large-scale IoT deployments, ensuring consistent performance across numerous devices.
These benefits make SSH an indispensable tool for IoT professionals seeking to optimize device management and security.
Basic SSH Commands for IoT
Mastering basic SSH commands is the first step toward effective IoT device management. These commands provide essential functionality for interacting with remote devices. Below are some commonly used SSH commands:
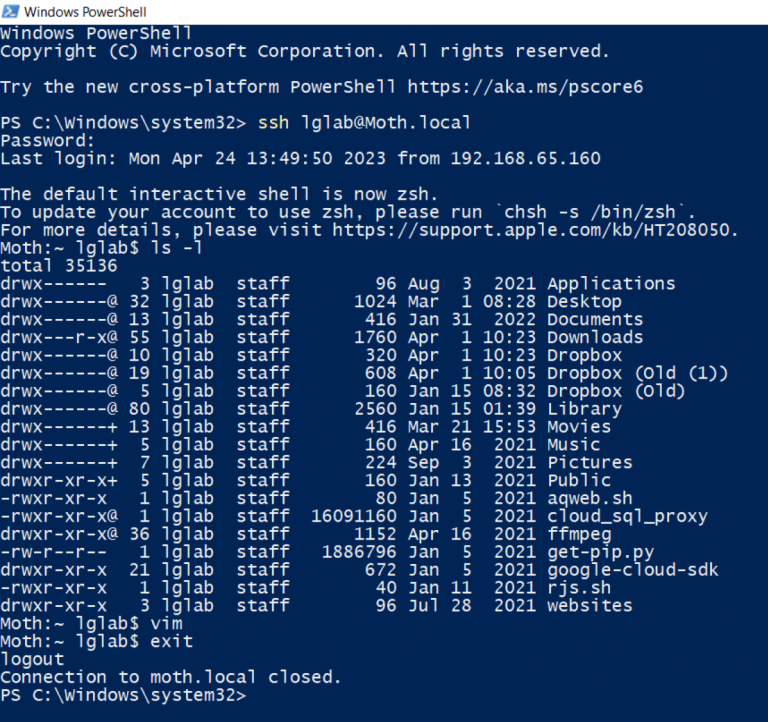
ssh username@hostname: Establishes a connection to a remote IoT device.scp file username@hostname:/path/to/destination: Transfers files securely to a remote device.ls: Lists files and directories on the remote system.cd: Changes the current directory on the remote system.sudo: Executes commands with administrative privileges.
These commands form the foundation of SSH remote IoT management, enabling users to perform basic tasks efficiently.
Advanced SSH Commands for IoT
For more complex IoT management tasks, advanced SSH commands are essential. These commands provide enhanced functionality, allowing administrators to optimize device performance and troubleshoot issues. Below are some advanced SSH commands:
ssh-keygen: Generates public and private keys for secure authentication.ssh-copy-id username@hostname: Copies the public key to the remote device for key-based authentication.top: Displays real-time system resource usage on the remote device.ps aux: Lists all running processes on the remote system.netstat -tuln: Displays active network connections and listening ports.
These commands empower administrators to gain deeper insights into remote IoT devices and address complex issues effectively.
Security Best Practices for SSH Remote IoT Commands
Securing SSH remote IoT connections is paramount to protecting sensitive data and preventing unauthorized access. Below are some best practices for enhancing SSH security:
- Disable password authentication and use key-based authentication instead.
- Change the default SSH port to a non-standard port to reduce brute-force attack risks.
- Implement firewall rules to restrict access to trusted IP addresses.
- Regularly update SSH software to patch known vulnerabilities.
- Monitor SSH logs for suspicious activity and potential security breaches.
By adhering to these best practices, administrators can significantly enhance the security of their SSH remote IoT connections.
Troubleshooting SSH IoT Connections
Occasionally, SSH remote IoT connections may encounter issues that hinder device management. Below are some common troubleshooting tips:
- Verify network connectivity between the client and server.
- Check SSH service status on the remote device to ensure it's running.
- Review SSH configuration files for potential errors.
- Test SSH connections using different ports or authentication methods.
- Consult SSH logs for detailed error information.
These troubleshooting steps can help identify and resolve issues quickly, ensuring uninterrupted SSH remote IoT management.
Real-World Applications of SSH in IoT
SSH remote IoT commands are widely used in various industries to manage and secure connected devices. Below are some real-world applications:
- Smart Home Automation: SSH enables remote control and monitoring of smart home devices, ensuring optimal performance and security.
- Industrial IoT: SSH facilitates secure communication between industrial sensors, controllers, and monitoring systems.
- Healthcare IoT: SSH ensures the secure transmission of medical data from IoT devices to centralized systems.
- Environmental Monitoring: SSH supports remote data collection and analysis for environmental sensors deployed in remote locations.
These applications demonstrate the versatility and importance of SSH in modern IoT ecosystems.
Tools and Software for SSH IoT Management
Several tools and software solutions are available to enhance SSH remote IoT management. Below are some popular options:
- PuTTY: A widely used SSH client for Windows users, offering a user-friendly interface for remote connections.
- OpenSSH: An open-source SSH implementation providing robust functionality for Linux and Unix-based systems.
- SecureCRT: A feature-rich SSH client offering advanced session management and scripting capabilities.
- WinSCP: A secure file transfer tool that integrates with SSH for seamless file management on remote IoT devices.
These tools simplify SSH remote IoT management, enabling administrators to perform tasks more efficiently.
The Future of SSH in IoT
As IoT continues to evolve, the role of SSH in remote device management is expected to grow. Emerging technologies such as 5G and edge computing will further enhance the capabilities of SSH, enabling faster and more reliable communication between devices. Additionally, advancements in encryption and authentication protocols will strengthen SSH security, addressing the growing challenges of IoT device management.
The future of SSH in IoT looks promising, with ongoing innovations aimed at improving efficiency, scalability, and security for remote device management.
Conclusion
In conclusion, SSH remote IoT commands are indispensable tools for managing and securing IoT devices. From basic commands to advanced functionalities, SSH provides a comprehensive solution for remote device interaction, ensuring efficient and secure communication. By following security best practices and leveraging the right tools, administrators can optimize SSH remote IoT management and address potential challenges effectively.
We invite you to share your thoughts and experiences with SSH remote IoT commands in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, let's continue to advance the field of IoT management and security.