In today's interconnected world, secure communication between devices has become more important than ever, especially in IoT (Internet of Things) networks. Understanding what Secure Shell (SSH) is and how it functions within IoT networks on Windows can be a game-changer for anyone managing or securing these systems. As cyber threats continue to evolve, leveraging SSH can provide robust protection for data integrity and device communication.
Secure Shell (SSH) is a cryptographic network protocol designed to secure data communication, remote shell services, and other secure network services between computers. In the context of IoT networks on Windows, SSH plays a pivotal role in safeguarding sensitive information and ensuring secure access to devices. Its importance cannot be overstated, as it serves as a foundational element in modern cybersecurity practices.
This article delves into the intricacies of SSH within IoT networks on Windows, exploring its functionalities, benefits, and best practices. By the end, you will have a comprehensive understanding of how SSH works and why it is indispensable in securing IoT ecosystems.
Read also:Ron Jeremy In Jail The Untold Story Behind The Arrests And Legal Battles
Table of Contents
- Introduction to Secure Shell (SSH)
- Secure Shell in IoT Networks
- SSH on Windows
- Benefits of Using SSH in IoT Networks
- How SSH Works
- Security Features of SSH
- Best Practices for Implementing SSH
- Common Issues and Troubleshooting
- The Future of SSH in IoT Networks
- Conclusion
Introduction to Secure Shell (SSH)
Secure Shell (SSH) was developed in the 1990s to address the security vulnerabilities of earlier protocols like Telnet and rlogin. It provides a secure channel over an unsecured network by encrypting data transmission and authenticating users. SSH operates on the application layer of the OSI model and uses port 22 by default.
Key Features of SSH
- Data Encryption: SSH ensures that all data transmitted between devices is encrypted, preventing unauthorized access.
- Authentication: It offers strong authentication mechanisms, including password-based and public-key authentication.
- Command Execution: SSH allows users to execute commands on remote machines securely.
SSH has become a standard protocol for secure communication across various platforms, including IoT devices running on Windows.
Secure Shell in IoT Networks
In IoT networks, where devices are interconnected and often operate in unsecured environments, SSH provides a reliable solution for securing communication. It ensures that data exchanged between IoT devices remains confidential and tamper-proof.
Why SSH is Crucial for IoT
- Secures Data Transmission: Protects sensitive information from interception.
- Authenticates Devices: Ensures only authorized devices can communicate within the network.
- Facilitates Remote Management: Allows administrators to manage IoT devices remotely with enhanced security.
Implementing SSH in IoT networks on Windows can significantly reduce the risk of cyberattacks and data breaches.
SSH on Windows
Windows has fully embraced SSH, providing built-in support for both SSH client and server functionalities since Windows 10 version 1809. This integration simplifies the process of setting up secure connections for IoT devices running on Windows.
Enabling SSH on Windows
- Install the OpenSSH Client and Server via Windows Features.
- Configure SSH settings through the Windows Registry or PowerShell.
- Use SSH keys for secure authentication instead of passwords.
By enabling SSH on Windows, users can securely manage IoT devices and ensure data integrity within their networks.
Read also:Is Bill Oreilly Married Today A Comprehensive Look At His Personal Life And Career
Benefits of Using SSH in IoT Networks
The adoption of SSH in IoT networks offers numerous advantages that contribute to enhanced security and operational efficiency.
Enhanced Security
SSH encrypts all data transmissions, making it extremely difficult for attackers to intercept or manipulate information. This is particularly important in IoT networks where devices often communicate over public networks.
Improved Efficiency
With SSH, administrators can remotely manage IoT devices without compromising security, saving time and resources. The protocol's reliability and performance make it ideal for large-scale IoT deployments.
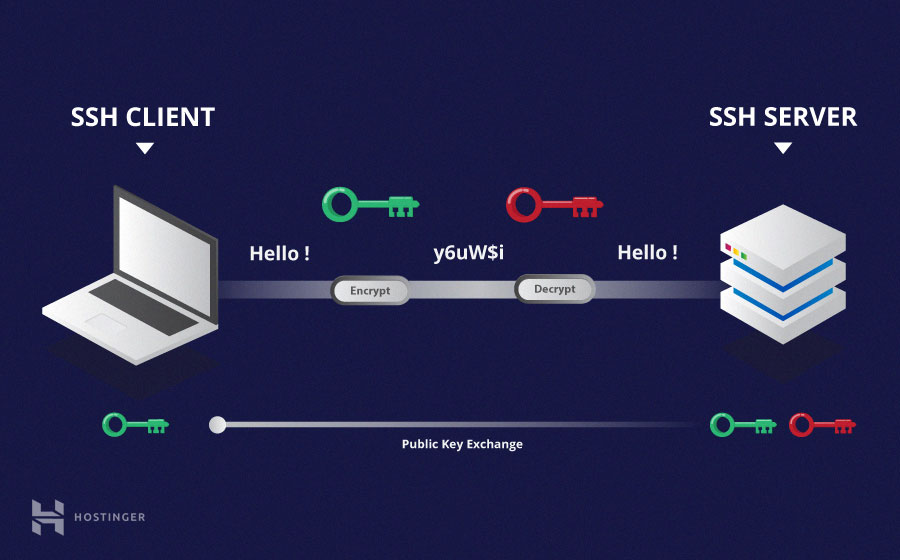
How SSH Works
SSH operates through a client-server architecture, where the client initiates a connection to the server. The process involves several steps:
- Connection Establishment: The client connects to the server using the specified port (usually 22).
- Key Exchange: The client and server exchange cryptographic keys to establish a secure session.
- User Authentication: The client authenticates itself to the server using passwords or public-key authentication.
- Data Transmission: Once authenticated, encrypted data can be transmitted between the client and server.
This structured approach ensures that all communications are secure and authenticated.
Security Features of SSH
SSH incorporates several advanced security features that make it a preferred choice for securing IoT networks:
Encryption Protocols
SSH supports various encryption algorithms, such as AES, Blowfish, and DES, ensuring that data remains encrypted during transmission.
Public Key Infrastructure (PKI)
SSH leverages PKI for secure authentication, allowing users to authenticate using digital certificates instead of passwords.
Best Practices for Implementing SSH
To maximize the security benefits of SSH in IoT networks, it is essential to follow best practices:
- Use strong, unique passwords or implement public-key authentication.
- Regularly update SSH software to patch vulnerabilities.
- Limit SSH access to trusted IP addresses using firewall rules.
By adhering to these practices, organizations can enhance the security of their IoT networks.
Common Issues and Troubleshooting
While SSH is a robust protocol, users may encounter issues during implementation. Common problems include:
Connection Errors
Ensure that the SSH service is running on the server and that there are no firewall restrictions blocking port 22.
Authentication Failures
Verify that the correct credentials or SSH keys are being used for authentication.
Addressing these issues promptly can prevent disruptions in IoT network operations.
The Future of SSH in IoT Networks
As IoT continues to expand, the role of SSH in securing these networks will become increasingly critical. Advances in encryption technologies and the integration of SSH with emerging standards will further enhance its capabilities.
Integration with Emerging Technologies
SSH is likely to be integrated with blockchain and quantum-resistant cryptography, providing even stronger security measures for IoT networks.
Staying informed about these developments will help organizations stay ahead in the ever-evolving cybersecurity landscape.
Conclusion
Secure Shell (SSH) is an indispensable tool for securing IoT networks on Windows. Its ability to encrypt data, authenticate users, and facilitate remote management makes it a cornerstone of modern cybersecurity practices. By understanding how SSH works and implementing best practices, organizations can protect their IoT ecosystems from potential threats.
We encourage readers to share their thoughts and experiences with SSH in the comments section below. Additionally, explore other articles on our site to deepen your knowledge of cybersecurity and IoT technologies.