In today's rapidly evolving digital landscape, securely connect remote IoT VPC has become a critical aspect of network infrastructure management. As more devices become interconnected, the need for robust security measures to protect sensitive data and maintain network integrity is paramount. Organizations must adopt advanced strategies to ensure secure communication between remote IoT devices and Virtual Private Clouds (VPCs).
The rise of the Internet of Things (IoT) has revolutionized how businesses operate, enabling smarter and more efficient processes. However, this increased connectivity also introduces vulnerabilities that malicious actors can exploit. By securely connecting remote IoT devices to a VPC, companies can safeguard their operations and data from potential threats.
This article delves into the intricacies of securely connecting remote IoT VPCs, offering practical insights and actionable strategies to enhance your network's security. Whether you're a network administrator, IT professional, or cybersecurity enthusiast, this guide will provide valuable information to help you fortify your IoT infrastructure.
Read also:Is Kamala Harris An Alcoholic Unveiling The Facts And Debunking Myths
Table of Contents
- Introduction
- Understanding IoT and VPC
- Challenges in Securing IoT VPC
- Strategies for Secure Connection
- Tools and Technologies
- Best Practices for Secure IoT VPC
- Case Studies
- Future Trends in IoT Security
- Conclusion
- References
Introduction
In recent years, the proliferation of IoT devices has transformed industries, offering unprecedented levels of automation and data-driven insights. However, the integration of these devices into existing network infrastructures poses significant security challenges. One of the most effective ways to mitigate these risks is by securely connecting remote IoT devices to a Virtual Private Cloud (VPC).
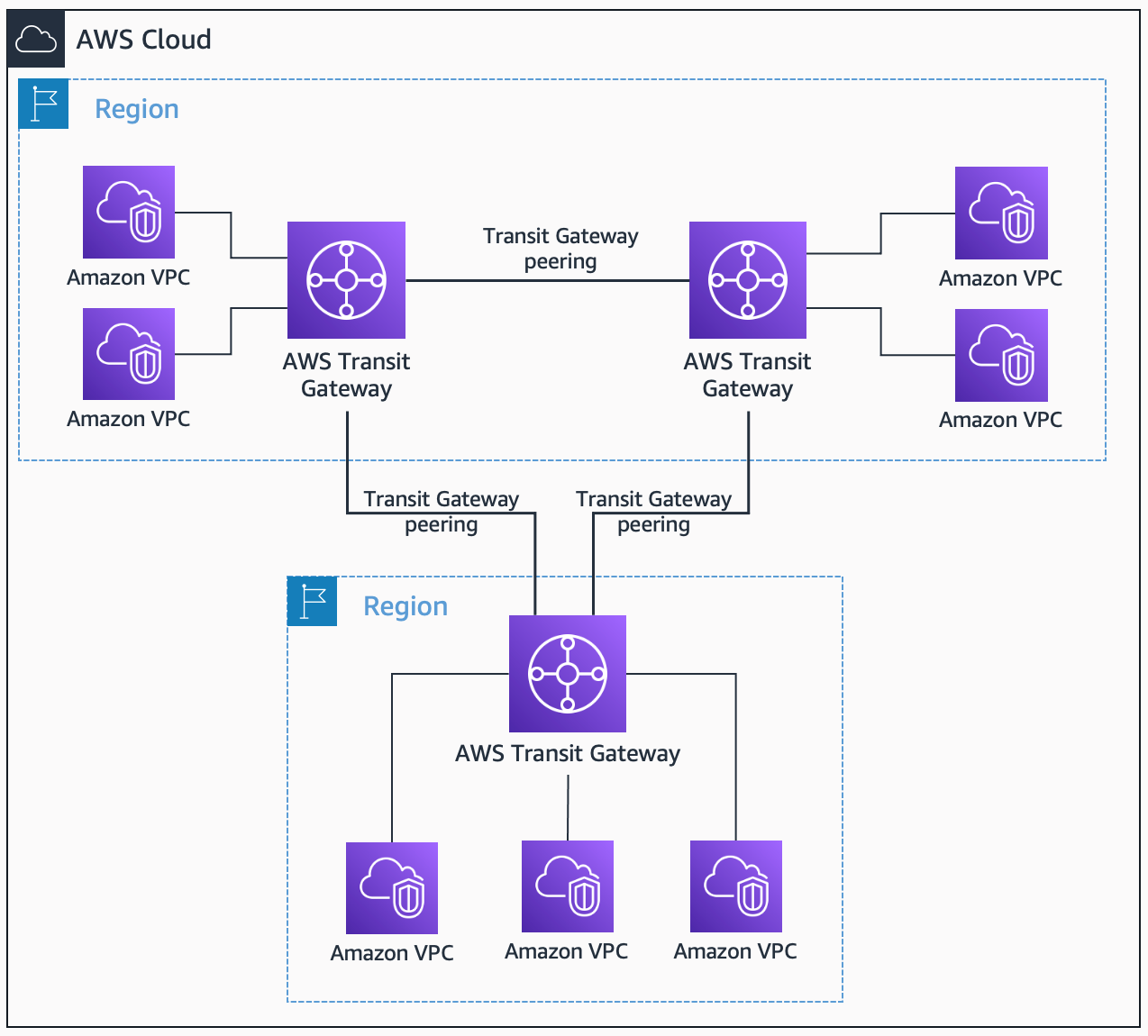
A VPC serves as a secure and isolated environment within the cloud, providing a dedicated space for storing and processing sensitive data. By leveraging VPCs, organizations can establish a secure connection between remote IoT devices and their core network, ensuring that data transmission remains protected from unauthorized access.
Understanding IoT and VPC
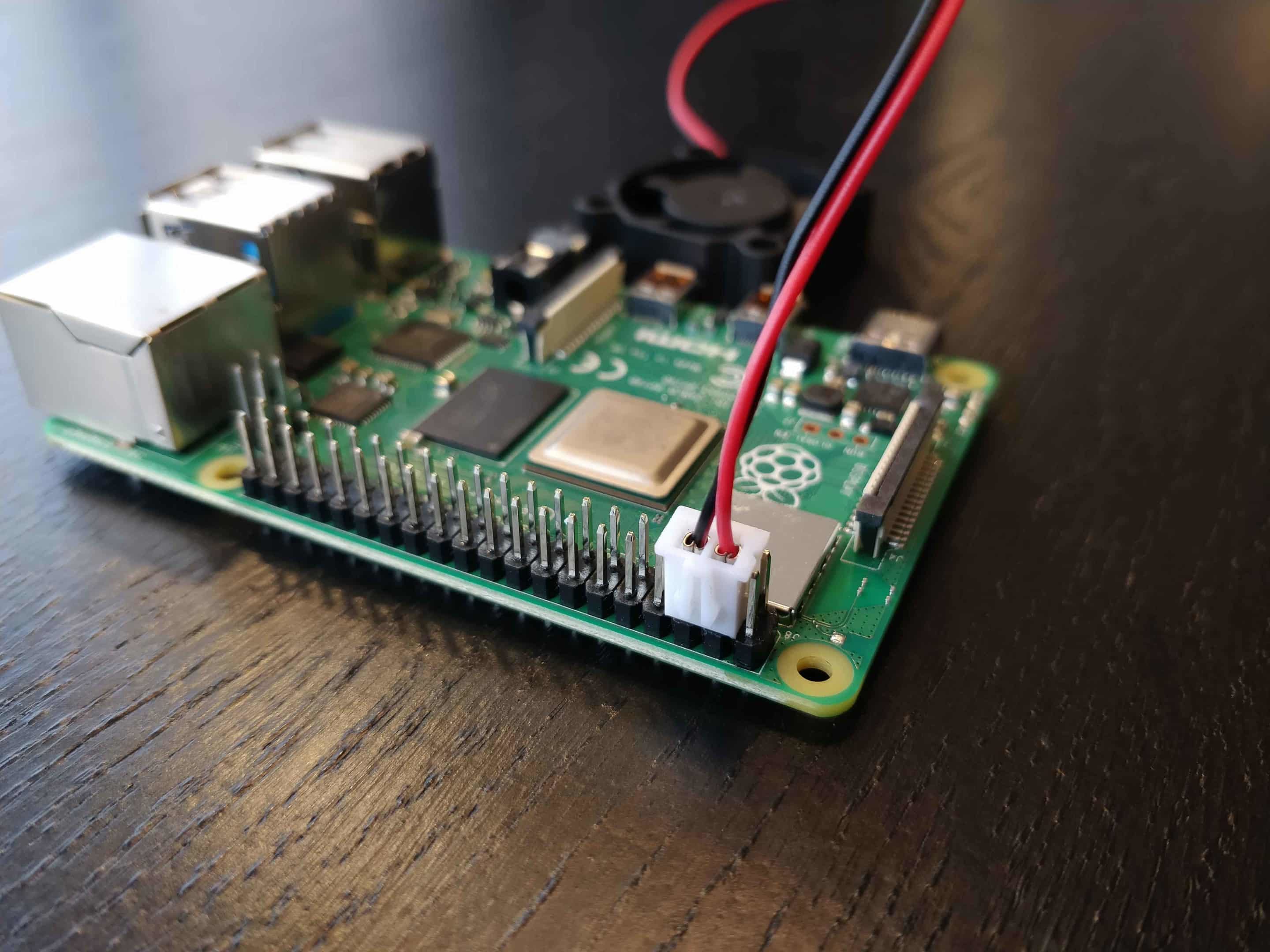
The Internet of Things refers to a network of interconnected devices capable of collecting and exchanging data. These devices range from simple sensors to complex industrial machinery, all designed to enhance operational efficiency and decision-making. On the other hand, a Virtual Private Cloud (VPC) is a private cloud environment hosted within a larger public cloud infrastructure.
When combined, IoT and VPC create a powerful framework for secure data management. By securely connecting remote IoT devices to a VPC, organizations can ensure that data transmission occurs in a controlled and protected environment, reducing the risk of data breaches and cyberattacks.
Challenges in Securing IoT VPC
While the integration of IoT devices with VPCs offers numerous benefits, it also presents several challenges. Some of the most significant challenges include:
- Device Authentication: Ensuring that only authorized devices can access the VPC.
- Data Encryption: Protecting data during transmission to prevent interception by malicious actors.
- Network Segmentation: Isolating IoT devices from the rest of the network to minimize potential damage in case of a breach.
- Scalability: Managing the increasing number of IoT devices without compromising security.
Strategies for Secure Connection
Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments to enhance security. By separating IoT devices from other network components, organizations can limit the potential impact of a breach. This strategy ensures that even if one segment is compromised, the rest of the network remains unaffected.
Read also:Judy Dench A Legendary Journey Through Seven Decades Of Acting
Data Encryption
Data encryption is a fundamental aspect of securing IoT VPC connections. By encrypting data both in transit and at rest, organizations can protect sensitive information from unauthorized access. Modern encryption protocols, such as AES-256 and TLS, provide robust security measures to safeguard data integrity.
Access Control
Implementing strict access control policies is essential for maintaining the security of IoT VPC connections. By defining who can access specific resources and under what conditions, organizations can reduce the risk of unauthorized access. Multi-factor authentication (MFA) and role-based access control (RBAC) are effective tools for enhancing access security.
Tools and Technologies
Several tools and technologies are available to facilitate the secure connection of remote IoT devices to VPCs. Some of the most popular options include:
- AWS IoT Core: A managed cloud service that enables secure communication between IoT devices and AWS services.
- Azure IoT Hub: A cloud-based solution for connecting, monitoring, and managing IoT devices securely.
- Google Cloud IoT Core: A platform for securely connecting and managing IoT devices at scale.
Best Practices for Secure IoT VPC
To ensure the secure connection of remote IoT devices to VPCs, organizations should adhere to the following best practices:
- Regularly update firmware and software to address security vulnerabilities.
- Implement comprehensive logging and monitoring to detect and respond to suspicious activities.
- Conduct regular security audits to identify and mitigate potential risks.
- Train employees on cybersecurity best practices to minimize human error.
Case Studies
Several organizations have successfully implemented secure IoT VPC solutions, achieving significant improvements in network security. For example, a manufacturing company used AWS IoT Core to securely connect its factory floor devices to a VPC, reducing downtime and improving operational efficiency. Similarly, a healthcare provider leveraged Azure IoT Hub to enhance the security of its medical devices, ensuring patient data remained protected.
Future Trends in IoT Security
As the IoT landscape continues to evolve, several trends are expected to shape the future of secure IoT VPC connections. These include:
- Edge Computing: Processing data closer to the source to reduce latency and enhance security.
- Artificial Intelligence: Utilizing AI-driven analytics to detect and respond to security threats in real-time.
- Quantum Cryptography: Exploring advanced encryption techniques to protect data against future quantum computing threats.
Conclusion
Securing the connection between remote IoT devices and VPCs is crucial for maintaining network integrity and protecting sensitive data. By implementing robust strategies such as network segmentation, data encryption, and access control, organizations can significantly enhance their IoT infrastructure's security. Additionally, leveraging cutting-edge tools and technologies, along with adhering to best practices, ensures that your network remains resilient against emerging threats.
We encourage readers to share their thoughts and experiences in the comments section below. Your feedback helps us improve and provide more valuable content. Don't forget to explore our other articles for more insights into cybersecurity and IoT solutions.
References
1. AWS IoT Core Documentation: https://docs.aws.amazon.com/iot-core/latest/userguide/
2. Azure IoT Hub Documentation: https://docs.microsoft.com/en-us/azure/iot-hub/
3. Google Cloud IoT Core Documentation: https://cloud.google.com/iot-core/docs