SSH access to IoT devices is a critical aspect of modern remote management, especially when leveraging AWS services. As IoT devices become more integrated into our daily lives, ensuring secure communication and management is essential. This guide will walk you through the process of setting up secure SSH connections to IoT devices anywhere using AWS, providing you with the tools and knowledge to manage your devices effectively.
With the increasing adoption of IoT devices across industries, the need for secure remote access has never been more important. Traditional methods of accessing devices remotely often lack the security and scalability required for enterprise-level deployments. AWS offers a robust solution that addresses these challenges, ensuring that your IoT devices remain secure and manageable from anywhere in the world.
This article will delve into the technical aspects of setting up SSH access for IoT devices using AWS, covering everything from basic configurations to advanced security measures. By the end of this guide, you'll have a comprehensive understanding of how to implement secure remote access for your IoT devices.
Read also:Denzel Washingtons Political Party A Comprehensive Analysis
Table of Contents
- Introduction to SSH and IoT on AWS
- Understanding SSH Basics
- Overview of IoT Devices
- AWS Services for IoT SSH
- Step-by-Step Setup Process
- Enhancing Security Measures
- Common Issues and Troubleshooting
- Scaling Your IoT SSH Infrastructure
- Best Practices for Managing IoT SSH
- Future Trends in IoT and SSH
Introduction to SSH and IoT on AWS
SSH (Secure Shell) is a cryptographic network protocol that allows users to securely access and manage remote devices over an unsecured network. In the context of IoT, SSH plays a crucial role in enabling secure communication between devices and their management systems. AWS provides a range of services that facilitate this process, ensuring that your IoT devices remain secure and accessible from anywhere.
By leveraging AWS services such as AWS IoT Core, AWS Systems Manager, and AWS CloudFormation, you can create a robust infrastructure for managing IoT devices remotely. This section will provide an overview of how these services work together to deliver secure SSH access to IoT devices.
Understanding SSH Basics
Before diving into the specifics of IoT and AWS, it's essential to understand the fundamentals of SSH. SSH uses encryption to secure data transmissions between a client and a server, ensuring that sensitive information remains protected. Key concepts include:
- Public-key cryptography for authentication.
- Secure tunneling for data transmission.
- Support for various authentication methods, including password-based and key-based authentication.
Understanding these basics will help you configure SSH access for your IoT devices more effectively.
Why SSH is Important for IoT
IoT devices often operate in unsecured environments, making them vulnerable to attacks. SSH provides a secure channel for managing these devices, reducing the risk of unauthorized access and data breaches. This section will explore the importance of SSH in IoT deployments and how it contributes to overall system security.
Overview of IoT Devices
IoT devices encompass a wide range of technologies, from simple sensors to complex industrial equipment. These devices are typically connected to the internet, allowing them to communicate with other systems and devices. Managing these devices remotely is essential for maintaining their functionality and security.
Read also:Is Lester Holt Ill Unveiling The Truth Behind The Rumors
This section will provide an overview of common IoT devices and their use cases, highlighting the need for secure remote access solutions.
Types of IoT Devices
- Smart home devices.
- Industrial sensors and actuators.
- Medical devices.
- Automotive systems.
Each type of device presents unique challenges and requirements for secure SSH access, which will be addressed in subsequent sections.
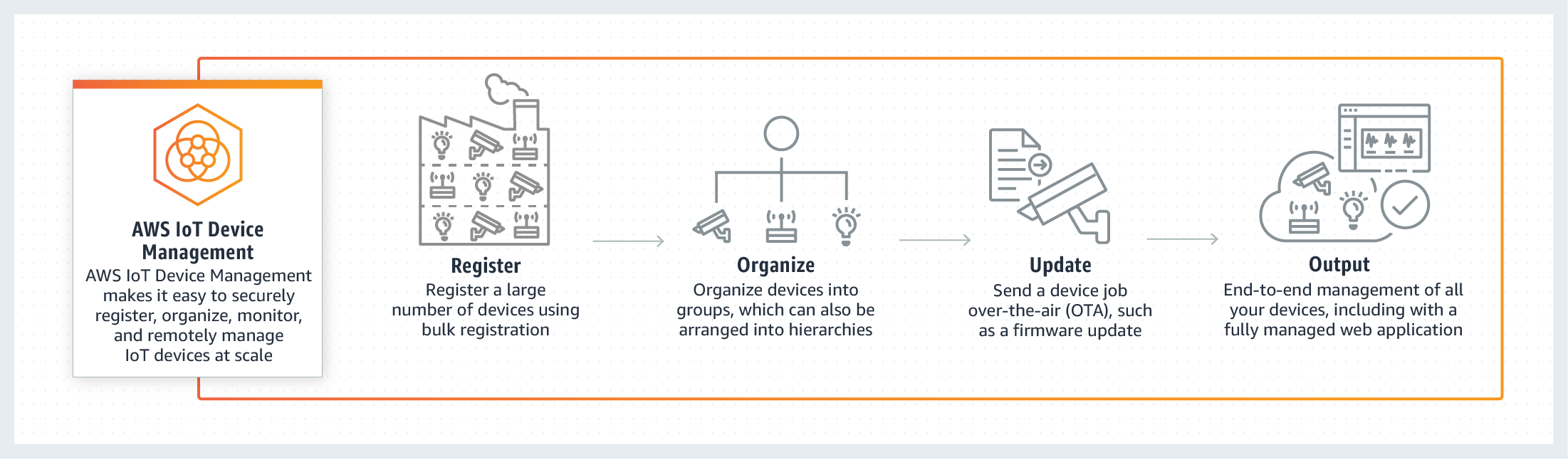
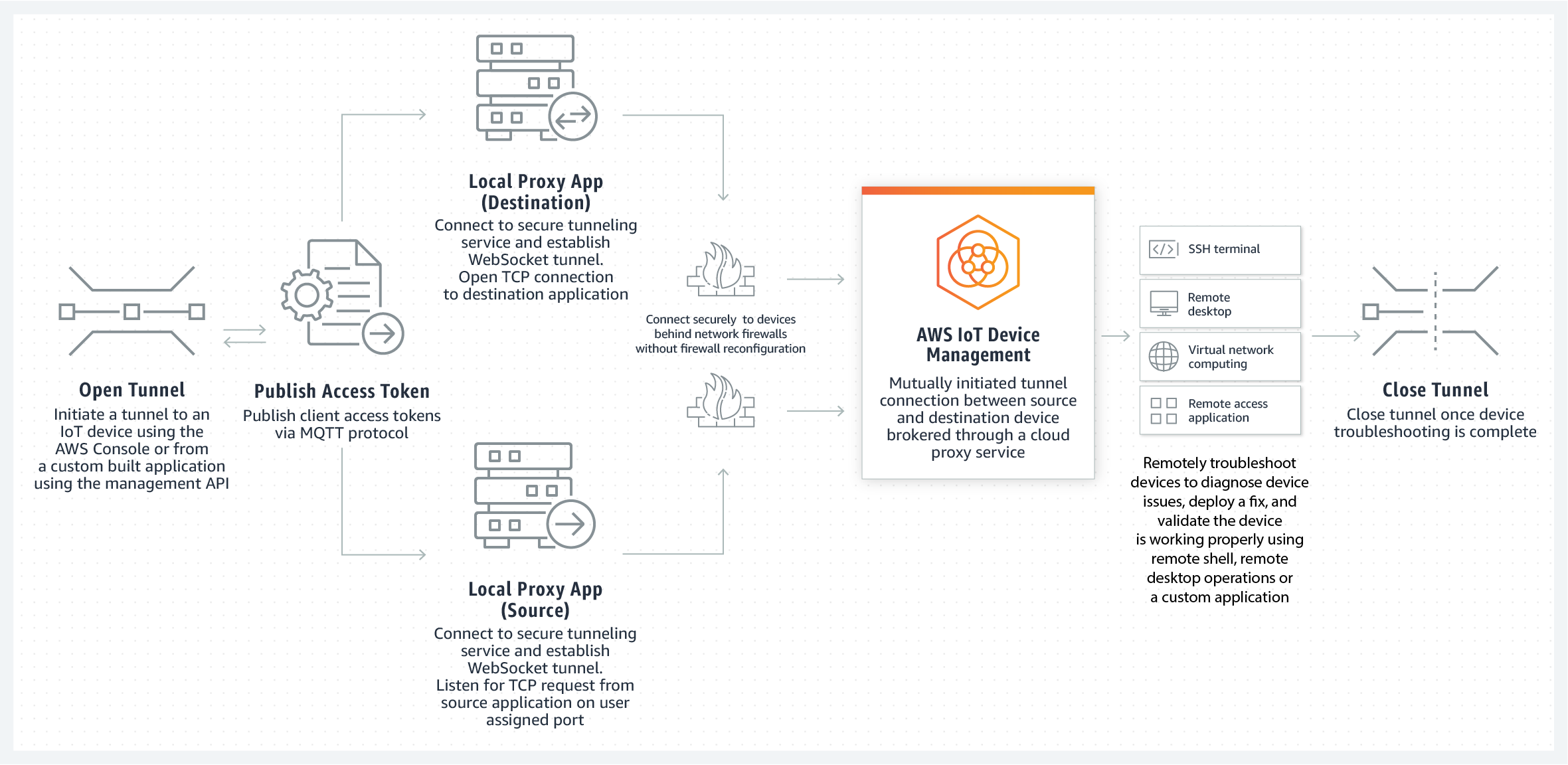
AWS Services for IoT SSH
AWS offers a suite of services designed to support IoT deployments, including secure SSH access. Key services include:
- AWS IoT Core: A managed cloud platform for connecting and managing IoT devices.
- AWS Systems Manager: A tool for managing and securing devices across your infrastructure.
- AWS CloudFormation: A service for automating the deployment of infrastructure resources.
This section will explore how these services can be used together to create a secure SSH access solution for IoT devices.
How AWS IoT Core Works
AWS IoT Core acts as a central hub for managing IoT devices, providing secure communication channels and device management capabilities. By integrating SSH access into this platform, you can ensure that your devices remain secure and accessible from anywhere.
Step-by-Step Setup Process
Setting up secure SSH access to IoT devices using AWS involves several steps. This section will guide you through the process, covering everything from initial configuration to advanced security measures.
- Create an AWS account and set up the necessary services.
- Provision your IoT devices and configure SSH access.
- Set up AWS IoT Core and integrate SSH into your device management workflow.
- Test and verify your configuration to ensure secure access.
By following these steps, you can establish a secure SSH connection to your IoT devices using AWS services.
Configuring SSH Keys
SSH keys are a critical component of secure access, providing a more secure alternative to password-based authentication. This section will walk you through the process of generating and configuring SSH keys for your IoT devices.
Enhancing Security Measures
While SSH provides a secure communication channel, additional security measures are necessary to protect your IoT devices from attacks. This section will explore various strategies for enhancing security, including:
- Implementing firewalls and network segmentation.
- Using strong authentication methods, such as multi-factor authentication.
- Regularly updating firmware and software to address vulnerabilities.
By implementing these measures, you can ensure that your IoT devices remain secure and protected from unauthorized access.
Best Practices for Secure IoT Deployments
Adopting best practices for IoT security is essential for maintaining the integrity of your devices and infrastructure. This section will provide guidance on implementing these practices in your SSH-enabled IoT deployments.
Common Issues and Troubleshooting
As with any technology, issues may arise when setting up SSH access for IoT devices. This section will address common problems and provide solutions for resolving them. Topics covered include:
- Connection issues and troubleshooting steps.
- Authentication failures and how to address them.
- Performance issues and optimization techniques.
By understanding these issues and their solutions, you can ensure smooth operation of your IoT SSH infrastructure.
Debugging SSH Connections
Debugging SSH connections can be challenging, especially when dealing with IoT devices. This section will provide tips and tools for diagnosing and resolving connection issues, ensuring that your devices remain accessible and secure.
Scaling Your IoT SSH Infrastructure
As your IoT deployment grows, scaling your SSH infrastructure becomes increasingly important. This section will explore strategies for scaling your infrastructure, including:
- Using AWS auto-scaling to manage device growth.
- Implementing load balancing for improved performance.
- Optimizing resource usage to reduce costs.
By implementing these strategies, you can ensure that your SSH-enabled IoT infrastructure remains scalable and efficient.
Optimizing Resource Usage
Optimizing resource usage is key to maintaining a cost-effective IoT SSH infrastructure. This section will provide guidance on identifying and addressing resource bottlenecks, ensuring that your infrastructure operates efficiently.
Best Practices for Managing IoT SSH
Managing IoT devices with SSH access requires adherence to best practices to ensure security and efficiency. This section will outline key practices for managing your IoT SSH infrastructure, including:
- Regularly monitoring device activity and logs.
- Implementing access controls and permissions.
- Conducting regular security audits and updates.
By following these practices, you can maintain a secure and efficient IoT SSH infrastructure.
Monitoring Device Activity
Monitoring device activity is essential for detecting and addressing security threats. This section will provide guidance on setting up monitoring systems and analyzing logs to identify potential issues.
Future Trends in IoT and SSH
The future of IoT and SSH is promising, with advancements in technology driving new possibilities for secure remote access. This section will explore emerging trends and technologies, including:
- Quantum-resistant cryptography for enhanced security.
- Edge computing for improved performance and efficiency.
- Artificial intelligence for intelligent device management.
By staying informed about these trends, you can ensure that your IoT SSH infrastructure remains cutting-edge and effective.
Quantum Computing and Its Impact
Quantum computing has the potential to revolutionize the field of cryptography, impacting the security of SSH and IoT devices. This section will examine the implications of quantum computing and how it may affect future SSH implementations.
Conclusion
In conclusion, setting up secure SSH access to IoT devices using AWS is a powerful solution for managing remote devices. By leveraging AWS services and adhering to best practices, you can ensure that your IoT devices remain secure and accessible from anywhere in the world. This guide has covered the essential steps and considerations for implementing SSH access, providing you with the knowledge and tools to manage your IoT infrastructure effectively.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and AWS technologies. Together, we can build a more secure and connected future for IoT devices.