IoT remote access via SSH on AWS has become a critical solution for businesses aiming to manage their devices securely and efficiently. As the Internet of Things (IoT) continues to expand, the need for secure and reliable remote access becomes increasingly important. This guide dives deep into the world of IoT remote access using SSH on AWS, providing you with everything you need to know to set up and manage your IoT ecosystem effectively.
In today's interconnected world, IoT devices are no longer confined to local networks. They are deployed globally, requiring remote access solutions that ensure security, scalability, and performance. AWS, with its robust infrastructure and services, offers a perfect platform to implement such solutions. By leveraging SSH (Secure Shell), you can establish encrypted connections to your IoT devices, ensuring data integrity and confidentiality.
This article is designed for professionals, developers, and enthusiasts who want to understand the nuances of IoT remote access using SSH on AWS. We'll explore the technical aspects, best practices, and real-world applications, ensuring that you're equipped with the knowledge to implement secure and scalable IoT solutions.
Read also:Lillian Phillips Bio A Comprehensive Look At Her Life Career And Achievements
Table of Contents
- Introduction to IoT Remote Access via SSH on AWS
- Understanding SSH and Its Role in IoT
- AWS IoT Platform: An Overview
Setup Process for IoT Remote Access via SSH on AWS
- Security Best Practices for IoT Remote Access
- Scaling Solutions for IoT Deployments
Real-World Use Cases of IoT Remote Access via SSH on AWS
- Troubleshooting Common Issues
- Optimizing Performance for IoT Remote Access
- Future Trends in IoT Remote Access
Introduction to IoT Remote Access via SSH on AWS
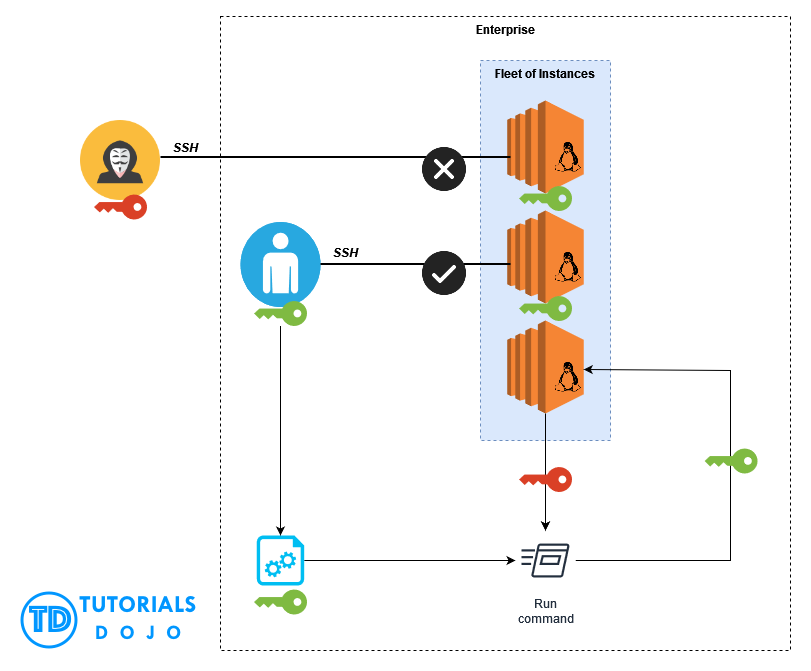
IoT remote access via SSH on AWS is a powerful solution for managing and monitoring IoT devices remotely. AWS provides a scalable and secure infrastructure that enables businesses to deploy IoT devices globally while maintaining control over them. SSH, as a protocol, ensures that all communication between devices and servers is encrypted, protecting sensitive data from unauthorized access.
The integration of SSH with AWS services allows for seamless management of IoT devices. Whether you're configuring devices, troubleshooting issues, or performing routine maintenance, SSH provides a secure channel for remote operations. This section will explore the fundamentals of IoT remote access, its benefits, and why AWS is the preferred platform for implementing such solutions.
Understanding SSH and Its Role in IoT
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure channel for remote access to devices, making it an ideal choice for IoT applications. In the context of IoT, SSH ensures that all data transmitted between devices and servers remains confidential and tamper-proof.
Key features of SSH include:
- Encryption of data during transmission
- Authentication mechanisms to verify device identity
- Support for secure file transfers
By leveraging SSH, IoT devices can be managed securely, reducing the risk of data breaches and unauthorized access. This section will delve deeper into the technical aspects of SSH and its role in IoT ecosystems.
AWS IoT Platform: An Overview
AWS IoT Platform is a comprehensive suite of services designed to simplify the development, deployment, and management of IoT solutions. It offers a range of features that cater to the unique needs of IoT applications, including device management, data processing, and analytics. The platform supports various communication protocols, including SSH, making it easy to integrate with existing systems.
Read also:Ron Jeremy In Jail The Untold Story Behind The Arrests And Legal Battles
Key components of AWS IoT Platform include:
- AWS IoT Core for device connectivity
- AWS IoT Device Management for device provisioning and monitoring
- AWS IoT Analytics for data processing and visualization
By leveraging AWS IoT Platform, businesses can build scalable and secure IoT solutions that meet their specific requirements. This section will provide an overview of the platform's capabilities and how it can be used to implement IoT remote access via SSH.
Setup Process for IoT Remote Access via SSH on AWS
Setting up IoT remote access via SSH on AWS involves several steps, from configuring devices to establishing secure connections. This section will guide you through the process, ensuring that you have a clear understanding of each step.
Steps to set up IoT remote access:
- Provision IoT devices using AWS IoT Device Management
- Configure SSH settings on devices
- Set up an EC2 instance on AWS to act as a SSH server
- Establish secure connections between devices and the EC2 instance
Each step is crucial for ensuring that your IoT devices can be accessed securely and efficiently. This section will provide detailed instructions and best practices for each step, helping you avoid common pitfalls.
Security Best Practices for IoT Remote Access
Security is paramount when it comes to IoT remote access. With the increasing number of cyber threats targeting IoT devices, it's essential to implement robust security measures. This section will outline best practices for securing IoT remote access via SSH on AWS.
Best practices include:
- Using strong passwords and multi-factor authentication
- Regularly updating device firmware and software
- Monitoring network activity for suspicious behavior
By following these best practices, you can significantly reduce the risk of security breaches and ensure the integrity of your IoT ecosystem. This section will also discuss advanced security measures, such as network segmentation and encryption, to further enhance security.
Scaling Solutions for IoT Deployments
As IoT deployments grow, the need for scalable solutions becomes increasingly important. AWS offers a range of services that can help you scale your IoT infrastructure efficiently. This section will explore strategies for scaling IoT deployments while maintaining performance and security.
Key strategies for scaling IoT deployments include:
- Using AWS Auto Scaling to handle increased workloads
- Implementing load balancing to distribute traffic
- Optimizing resource allocation to reduce costs
By leveraging these strategies, you can ensure that your IoT infrastructure can handle growth without compromising performance or security. This section will provide practical advice on scaling IoT deployments effectively.
Real-World Use Cases of IoT Remote Access via SSH on AWS
IoT remote access via SSH on AWS has numerous real-world applications across various industries. From manufacturing to healthcare, businesses are leveraging this technology to improve efficiency and reduce costs. This section will explore some of the most common use cases and how they benefit from IoT remote access.
Examples of use cases include:
- Remote monitoring of industrial equipment
- Telemedicine applications in healthcare
- Smart home automation systems
Each use case demonstrates the versatility and effectiveness of IoT remote access via SSH on AWS. This section will provide detailed examples and case studies to illustrate the benefits of this technology in real-world scenarios.
Troubleshooting Common Issues
Despite its many benefits, IoT remote access via SSH on AWS can present challenges. This section will address common issues that may arise during implementation and provide solutions to help you overcome them.
Common issues include:
- Connection timeouts
- Authentication failures
- Performance bottlenecks
By understanding these issues and their solutions, you can ensure that your IoT remote access solution remains reliable and efficient. This section will also provide troubleshooting tips and resources to help you resolve issues quickly.
Optimizing Performance for IoT Remote Access
Optimizing performance is crucial for ensuring that IoT remote access solutions meet the demands of modern applications. This section will explore strategies for improving the performance of IoT remote access via SSH on AWS.
Performance optimization strategies include:
- Using caching to reduce latency
- Optimizing network configurations for faster data transfer
- Implementing compression to reduce bandwidth usage
By implementing these strategies, you can enhance the performance of your IoT remote access solution, ensuring that it meets the needs of your applications. This section will provide practical advice on optimizing performance effectively.
Future Trends in IoT Remote Access
The future of IoT remote access is promising, with advancements in technology driving innovation and growth. This section will explore emerging trends and technologies that are shaping the future of IoT remote access via SSH on AWS.
Key trends include:
- Increased adoption of edge computing
- Integration of AI and machine learning for predictive maintenance
- Enhanced security measures to protect against cyber threats
By staying informed about these trends, you can ensure that your IoT remote access solution remains cutting-edge and effective. This section will provide insights into the future of IoT remote access and how you can prepare for it.
Kesimpulan
In conclusion, IoT remote access via SSH on AWS offers a powerful solution for managing and monitoring IoT devices securely and efficiently. By leveraging the capabilities of AWS IoT Platform and implementing best practices for security and performance, businesses can build scalable and reliable IoT solutions that meet their specific needs.
We encourage you to take action by experimenting with the techniques and strategies discussed in this article. Whether you're a developer, IT professional, or business leader, understanding IoT remote access via SSH on AWS can help you unlock new opportunities and drive innovation in your organization. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into IoT and related technologies.