SSH (Secure Shell) is a powerful tool for securely managing and accessing remote IoT devices. It provides a secure channel to connect to devices over the internet or a local network, ensuring data integrity and confidentiality. Whether you're a beginner or an experienced user, understanding how to use SSH for IoT can significantly enhance your ability to manage remote devices effectively.
In today's connected world, IoT devices play a crucial role in various industries, from smart homes to industrial automation. However, managing these devices remotely can be challenging without the right tools. SSH offers a secure and reliable solution for remote access, allowing users to control and monitor their IoT devices from anywhere.
This article will guide you step-by-step through the process of using SSH for remote IoT devices. We'll cover everything from setting up SSH to troubleshooting common issues, ensuring you have all the information you need to manage your IoT devices securely and efficiently.
Read also:Harry Connick Jr Family Pictures A Closer Look Into The Life Of The Beloved Musician
Table of Contents
- Introduction to SSH
- Why Use SSH for Remote IoT?
- Prerequisites for Using SSH
- Setting Up an SSH Server
- Connecting to Remote IoT Devices
- Securing Your SSH Connection
- Advanced SSH Features for IoT
- Troubleshooting Common SSH Issues
- Best Practices for SSH in IoT
- The Future of SSH in IoT
Introduction to SSH
SSH, or Secure Shell, is a cryptographic protocol designed to provide secure communication over an unsecured network. It is widely used for remote command execution and secure data transfer. In the context of IoT, SSH plays a vital role in enabling secure access to devices that may not have physical interfaces.
SSH operates on port 22 by default and uses encryption algorithms to protect data during transmission. This ensures that sensitive information, such as login credentials and configuration files, remains confidential. Understanding the basics of SSH is essential for anyone looking to manage IoT devices remotely.
Some key features of SSH include:
- Encryption for secure data transmission
- Authentication methods, including password and public key
- Support for tunneling and port forwarding
- Platform independence, allowing it to run on various operating systems
Why Use SSH for Remote IoT?
Using SSH for remote IoT devices offers several advantages over other protocols. First and foremost, SSH ensures the security and integrity of data transmitted between devices. This is particularly important in IoT applications where sensitive information is often involved.
Additionally, SSH provides a robust framework for managing and maintaining IoT devices. With SSH, users can perform tasks such as:
- Updating firmware and software
- Monitoring device performance
- Configuring network settings
- Running diagnostic tests
These capabilities make SSH an indispensable tool for IoT administrators and developers, enabling them to manage their devices efficiently and securely.
Read also:Marguerite Whitley The Fascinating Life And Legacy Of A Hollywood Icon
Prerequisites for Using SSH
Hardware and Software Requirements
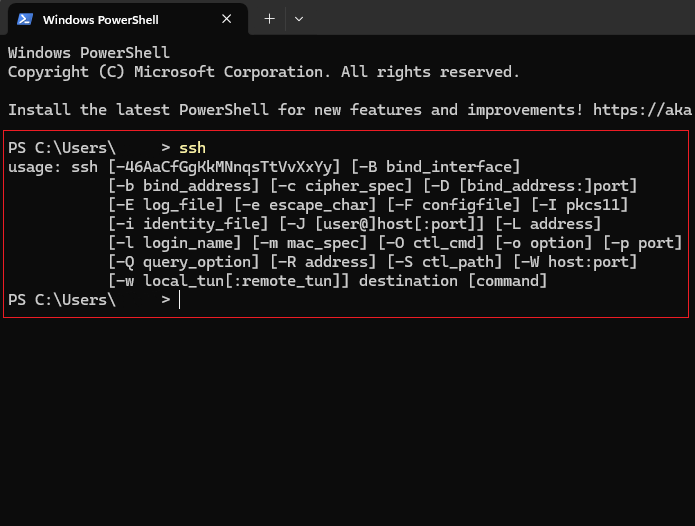
Before you can start using SSH for remote IoT devices, you'll need to ensure that both your local machine and the IoT device meet the necessary requirements. On the hardware side, you'll need:
- A computer or laptop with SSH client software installed
- An IoT device capable of running an SSH server
- A stable internet or local network connection
Software Setup
On the software side, you'll need to install and configure the following:
- An SSH client, such as OpenSSH or PuTTY
- An SSH server on the IoT device, typically provided by the device's operating system
- Any additional software or libraries required by your specific IoT application
Once these prerequisites are in place, you'll be ready to proceed with setting up and using SSH for your IoT devices.
Setting Up an SSH Server
Setting up an SSH server on your IoT device is a critical step in enabling remote access. The process varies depending on the operating system and hardware platform of your device. Below is a general guide to setting up an SSH server:
Step 1: Enable SSH on the Device
Most modern IoT devices come with SSH pre-installed, but it may be disabled by default. To enable SSH, follow these steps:
- Log in to your device's administrative interface
- Navigate to the network settings or security options
- Enable the SSH service and save your changes
Step 2: Configure Firewall Settings
Ensure that your device's firewall allows incoming connections on port 22 (or the custom port you've configured). This step is crucial for allowing remote access to your device.
Step 3: Test the SSH Server
Once the SSH server is enabled, test it by connecting from another device on the same network. Use the following command in your terminal:
ssh username@device_ip_address
Connecting to Remote IoT Devices
Connecting to remote IoT devices using SSH is a straightforward process. Here's how you can do it:
Using an SSH Client
On your local machine, open your SSH client and enter the following command:
ssh username@remote_device_ip
Replace "username" with your IoT device's login name and "remote_device_ip" with the device's IP address.
Authentication Methods
SSH supports multiple authentication methods, including:
- Password-based authentication
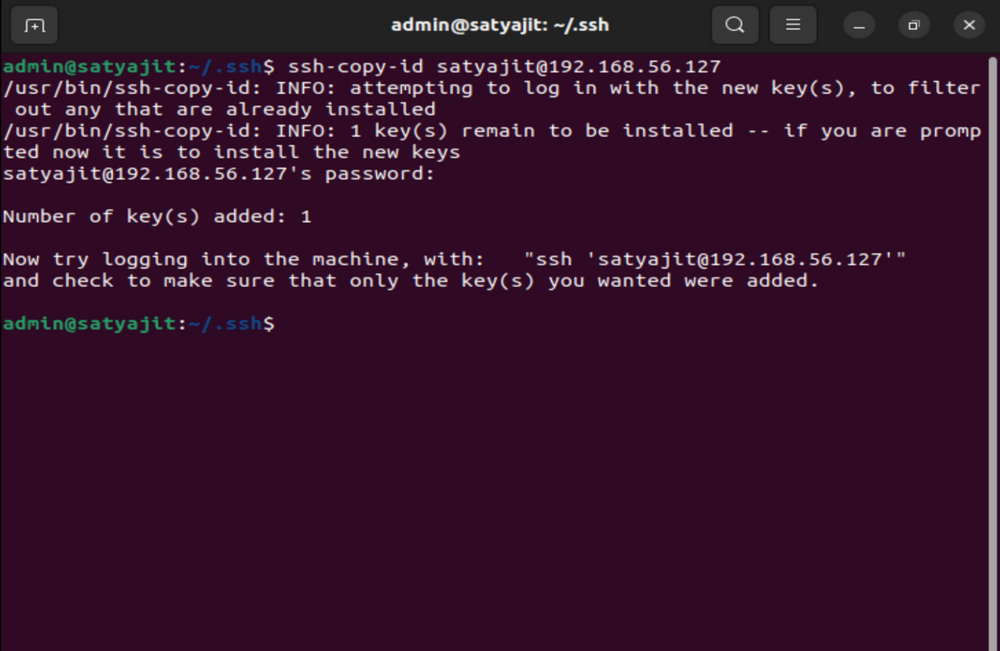
- Public key authentication
For added security, it's recommended to use public key authentication whenever possible.
Securing Your SSH Connection
While SSH is inherently secure, there are additional steps you can take to further protect your connections. These include:
- Changing the default SSH port
- Disabling password authentication in favor of public key authentication
- Implementing firewall rules to restrict access
- Using strong, unique passwords for user accounts
By implementing these security measures, you can significantly reduce the risk of unauthorized access to your IoT devices.
Advanced SSH Features for IoT
SSH offers several advanced features that can enhance its functionality for IoT applications. These include:
SSH Tunneling
SSH tunneling allows you to securely forward traffic between devices, making it ideal for accessing services behind firewalls or NAT.
Port Forwarding
Port forwarding enables you to redirect traffic from one port to another, facilitating remote access to specific services on your IoT device.
SSH Keys
Using SSH keys for authentication provides a secure and convenient way to access your devices without entering passwords each time.
Troubleshooting Common SSH Issues
Even with proper setup, you may encounter issues when using SSH for IoT devices. Common problems include:
- Connection timeouts
- Authentication failures
- Firewall or network configuration issues
To troubleshoot these issues, start by checking the following:
- Verify that the SSH server is running on the IoT device
- Ensure that the correct IP address and port number are being used
- Check firewall settings to confirm that incoming connections are allowed
Best Practices for SSH in IoT
To ensure the secure and efficient use of SSH for IoT devices, follow these best practices:
- Regularly update your device's firmware and SSH software
- Monitor SSH logs for suspicious activity
- Limit access to trusted users and devices
- Use strong, unique passwords and SSH keys
The Future of SSH in IoT
As the IoT ecosystem continues to grow, the role of SSH in securing remote connections will become increasingly important. Advances in encryption technology and the development of new protocols will further enhance the security and functionality of SSH for IoT applications.
Looking ahead, we can expect to see:
- Improved support for lightweight protocols on resource-constrained devices
- Integration with emerging technologies such as blockchain for enhanced security
- Greater adoption of automated security measures to protect against threats
Kesimpulan
In conclusion, SSH is an invaluable tool for managing and securing remote IoT devices. By following the steps outlined in this guide, you can ensure that your devices are accessible and protected from unauthorized access. Remember to implement best practices and stay informed about the latest developments in SSH and IoT security.
We invite you to share your thoughts and experiences with SSH in the comments below. If you found this article helpful, please consider sharing it with others who may benefit from the information. For more resources on IoT and cybersecurity, explore our other articles and guides.