Accessing IoT devices remotely has become increasingly essential in today's interconnected world. With the rise of smart technology, businesses and individuals need secure and efficient ways to manage their IoT devices from anywhere. One of the most reliable methods for remote access is through SSH (Secure Shell) on a free AWS (Amazon Web Services) platform. This article will guide you through setting up and managing IoT devices using SSH, ensuring seamless and secure connectivity.
As more devices connect to the internet, the demand for remote access solutions grows. Whether you're a tech enthusiast, a small business owner, or a professional developer, understanding how to remotely access IoT devices via SSH on AWS can save time, reduce costs, and enhance productivity. AWS offers a free tier that makes this process accessible to everyone, regardless of budget.
In this comprehensive guide, we'll explore the tools, methods, and best practices for setting up remote access to IoT devices. By the end of this article, you'll have the knowledge and skills to configure your own secure SSH connection on AWS, ensuring your IoT devices remain accessible and protected at all times.
Read also:Zendaya Height And Weight A Comprehensive Guide To The Iconic Star
Table of Contents
- Introduction to IoT and Remote Access
- Why Use SSH for IoT Devices?
- Understanding AWS Free Tier
- Setting Up AWS for IoT Devices
- Configuring SSH Access
- Securing Your SSH Connection
- Troubleshooting Common Issues
- Best Practices for Remote Access
- Use Cases for Remotely Accessing IoT Devices
- Conclusion and Call to Action
Introduction to IoT and Remote Access
The Internet of Things (IoT) refers to the network of physical devices, vehicles, appliances, and other items embedded with sensors, software, and connectivity. These devices collect and exchange data, enabling automation and enhanced functionality. Remote access to IoT devices is crucial for monitoring, troubleshooting, and maintaining these systems without physical presence.
Key Benefits of IoT Remote Access
- Increased efficiency and productivity
- Reduced operational costs
- Enhanced security and control
- Improved data collection and analysis
By leveraging SSH for remote access, you ensure a secure and encrypted connection, protecting sensitive data and preventing unauthorized access.
Why Use SSH for IoT Devices?
SSH (Secure Shell) is a cryptographic network protocol that provides secure communication over an unsecured network. It is widely used for remote login and command execution, making it ideal for managing IoT devices.
Advantages of Using SSH
- Encryption of data during transmission
- Authentication through public and private keys
- Support for various authentication methods
- Compatibility with multiple operating systems
SSH ensures that your IoT devices remain secure while allowing you to access them from anywhere in the world.
Understanding AWS Free Tier
Amazon Web Services (AWS) offers a free tier that provides access to a variety of services, including EC2 instances, which are perfect for hosting IoT devices. The free tier is available to new AWS customers for the first 12 months and includes:
- 750 hours per month of t2.micro or t3.micro instances
- 30 GB of data transfer out per month
- Unlimited data transfer in
By utilizing the AWS free tier, you can set up a secure SSH connection without incurring any costs, making it an attractive option for individuals and small businesses.
Read also:Harry Enten Education A Comprehensive Guide To His Expertise And Achievements
Setting Up AWS for IoT Devices
Setting up AWS for IoT devices involves several steps, including creating an AWS account, launching an EC2 instance, and configuring security settings.
Steps to Set Up AWS
- Sign up for an AWS account at https://aws.amazon.com/
- Go to the EC2 dashboard and click "Launch Instance"
- Select an Amazon Machine Image (AMI) compatible with your IoT device
- Choose an instance type, such as t2.micro, which is eligible for the free tier
- Configure instance details, including network settings and storage
- Create or select a key pair for SSH access
Once your instance is launched, you can proceed to configure SSH access for your IoT devices.
Configuring SSH Access
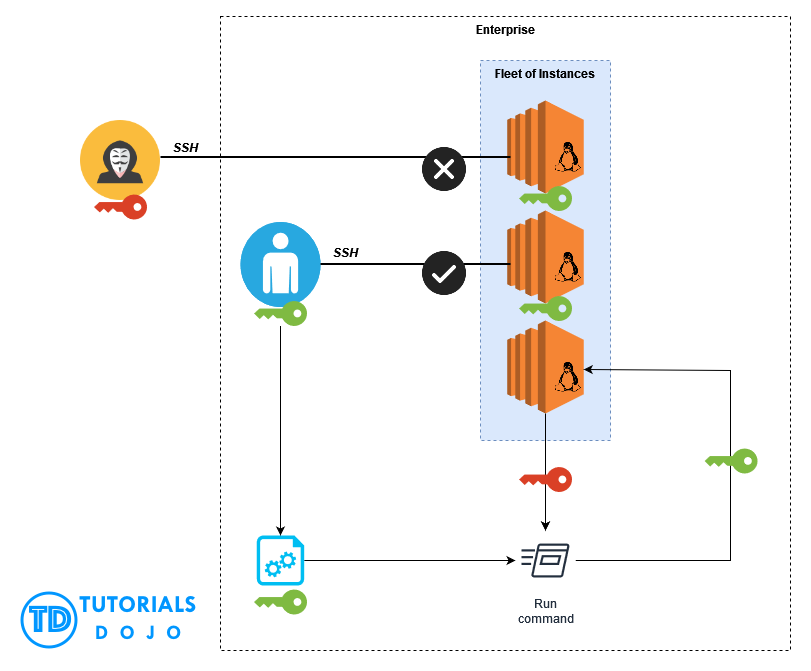
Configuring SSH access involves setting up the necessary security groups, firewall rules, and key-based authentication.
Setting Up Security Groups
Security groups act as virtual firewalls for your EC2 instances. To allow SSH access, you need to add a rule that permits incoming traffic on port 22.
- Go to the EC2 dashboard and select "Security Groups"
- Create a new security group or edit an existing one
- Add a rule allowing inbound traffic on port 22 from your IP address or a specific range
Configuring Key-Based Authentication
Key-based authentication enhances security by requiring a private key for SSH access. This method eliminates the need for passwords, reducing the risk of brute-force attacks.
- Generate a key pair using a tool like PuTTYgen or ssh-keygen
- Upload the public key to your EC2 instance during setup
- Store the private key securely on your local machine
With key-based authentication configured, you can now establish a secure SSH connection to your IoT devices.
Securing Your SSH Connection
Securing your SSH connection is critical to protecting your IoT devices from unauthorized access. Here are some best practices to enhance security:
- Disable password authentication and use key-based authentication only
- Change the default SSH port (22) to a non-standard port
- Implement rate limiting to prevent brute-force attacks
- Regularly update your EC2 instance and IoT devices to patch vulnerabilities
- Monitor logs for suspicious activity
By following these practices, you can ensure that your SSH connection remains secure and your IoT devices are protected.
Troubleshooting Common Issues
Despite careful setup, issues may arise when configuring SSH access for IoT devices. Here are some common problems and their solutions:
Connection Timeout
- Verify that the security group allows inbound traffic on the correct port
- Check the instance's network settings and ensure it has internet access
Permission Denied (Public Key)
- Ensure the correct private key is being used
- Check file permissions for the private key (chmod 400)
If you encounter any issues, refer to the AWS documentation or seek assistance from the AWS community forums.
Best Practices for Remote Access
Adopting best practices for remote access ensures optimal performance and security. Consider the following tips:
- Limit access to authorized users only
- Regularly back up your IoT devices and EC2 instances
- Use strong, unique passwords for all accounts
- Implement multi-factor authentication (MFA) where possible
- Keep software and firmware up to date
By adhering to these practices, you can maintain a secure and efficient remote access system for your IoT devices.
Use Cases for Remotely Accessing IoT Devices
Remote access to IoT devices has numerous applications across various industries. Here are some examples:
Smart Home Automation
Homeowners can remotely monitor and control smart devices such as thermostats, lighting systems, and security cameras, enhancing convenience and energy efficiency.
Industrial IoT
Manufacturers can access industrial sensors and machines to perform predictive maintenance, reducing downtime and improving productivity.
Agriculture
Farmers can remotely monitor soil moisture levels, weather conditions, and irrigation systems, optimizing crop yields and resource usage.
These use cases demonstrate the versatility and value of remote access in the IoT ecosystem.
Conclusion and Call to Action
Remotely accessing IoT devices via SSH on a free AWS platform is a powerful solution for managing and maintaining connected devices. By following the steps outlined in this article, you can set up a secure and efficient remote access system that enhances productivity and reduces costs.
We encourage you to experiment with AWS and SSH to explore the full potential of remote IoT management. Don't forget to leave a comment or share this article with others who may benefit from this information. For more in-depth guides and resources, explore our other articles on IoT and cloud computing.
Remember, staying informed and proactive is key to securing your IoT devices and ensuring seamless remote access. Happy configuring!