In today's interconnected world, leveraging SSH remote IoT devices, especially Raspberry Pi free solutions, has become a cornerstone for building secure and efficient systems. Whether you're a hobbyist or a professional developer, understanding how to set up and manage SSH connections on Raspberry Pi is critical for remote control and automation. This article will delve into the best practices, tools, and strategies to optimize your IoT setup using Raspberry Pi, ensuring seamless remote access without compromising security.
Raspberry Pi has emerged as a go-to platform for IoT enthusiasts and professionals alike. Its affordability, versatility, and robust community support make it an ideal choice for SSH remote IoT projects. By utilizing free tools and open-source software, you can harness the full potential of your Raspberry Pi for remote management, data collection, and automation.
This guide will walk you through the essential steps to configure SSH on your Raspberry Pi, explore the best SSH remote IoT device configurations, and highlight free resources to enhance your project. Whether you're a beginner or an advanced user, this article will provide you with actionable insights to elevate your IoT capabilities.
Read also:Dagen Mcdowell Divorce An Indepth Analysis Of The Highprofile Split
Table of Contents
- Introduction to SSH and Its Importance in IoT
- Raspberry Pi: A Perfect IoT Platform
- Setting Up SSH on Raspberry Pi
- Securing SSH Connections for IoT Devices
- Free Tools and Resources for SSH Remote Access
- Best Practices for SSH Remote IoT Devices
- Troubleshooting Common SSH Issues
- Case Studies: Real-World Applications of Raspberry Pi SSH
- Future Trends in SSH and IoT
- Conclusion and Call to Action
Introduction to SSH and Its Importance in IoT
SSH, or Secure Shell, is a cryptographic protocol designed to provide secure communication over unsecured networks. In the realm of IoT, SSH plays a pivotal role in enabling remote access and management of devices such as Raspberry Pi. By encrypting data transmitted between devices, SSH ensures that sensitive information remains protected from unauthorized access.
Why is SSH crucial for IoT? IoT devices often operate in environments where physical access is limited or impractical. SSH allows users to securely connect to these devices remotely, facilitating tasks like configuration, monitoring, and troubleshooting. This capability is particularly valuable for projects involving Raspberry Pi, where remote management can significantly enhance productivity and efficiency.
In addition to security, SSH offers several advantages, including:
- Reliable data encryption
- Support for multiple authentication methods
- Compatibility with various platforms and operating systems
Raspberry Pi: A Perfect IoT Platform
Raspberry Pi has become synonymous with IoT innovation due to its affordability, flexibility, and ease of use. This credit-card-sized computer is equipped with features that make it an ideal platform for SSH remote IoT projects. From GPIO pins for hardware interfacing to robust support for Linux-based operating systems, Raspberry Pi offers everything needed to build sophisticated IoT solutions.
Key Features of Raspberry Pi
- Low power consumption
- Highly customizable hardware and software configurations
- Extensive library of tutorials and community support
Raspberry Pi's compatibility with SSH makes it a top choice for remote IoT device management. By leveraging free and open-source tools, users can create secure and efficient systems tailored to their specific needs.
Setting Up SSH on Raspberry Pi
Configuring SSH on Raspberry Pi is a straightforward process that requires minimal technical expertise. Whether you're using the latest Raspberry Pi OS or another Linux-based distribution, the steps remain largely consistent.
Read also:Rob Dyrdek Parents Exploring The Life Influence And Legacy
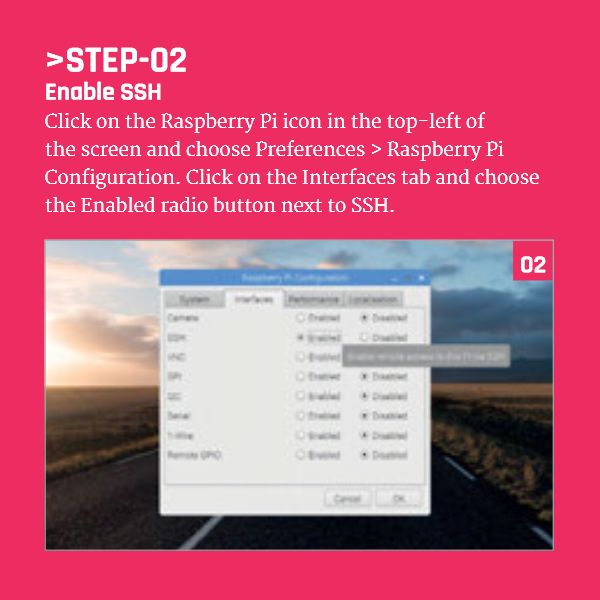
Steps to Enable SSH
- Connect your Raspberry Pi to a monitor, keyboard, and mouse.
- Boot the device and log in to the operating system.
- Open the terminal and enter the following command:
sudo raspi-config. - Navigate to "Interfacing Options" and select "SSH".
- Choose "Enable" and reboot the device.
Alternatively, you can enable SSH by placing an empty file named "ssh" in the boot partition of your Raspberry Pi's SD card. This method is particularly useful when setting up a headless Raspberry Pi.
Securing SSH Connections for IoT Devices
While SSH provides robust security out of the box, additional measures can further enhance the protection of your IoT devices. Implementing best practices for SSH security ensures that your Raspberry Pi remains safe from potential threats.
Best Security Practices
- Use strong, unique passwords or public key authentication.
- Disable root login to prevent unauthorized access.
- Change the default SSH port (22) to a non-standard port.
- Enable two-factor authentication (2FA) for added security.
By adhering to these guidelines, you can significantly reduce the risk of unauthorized access to your SSH remote IoT devices.
Free Tools and Resources for SSH Remote Access
Several free tools and resources are available to enhance your SSH experience on Raspberry Pi. These tools simplify remote management and improve overall system performance.
Popular Free Tools
- PuTTY: A popular SSH client for Windows users.
- OpenSSH: A widely used open-source SSH implementation.
- SSHFS: Allows you to mount remote file systems over SSH.
These tools, combined with Raspberry Pi's capabilities, provide a powerful platform for SSH remote IoT projects.
Best Practices for SSH Remote IoT Devices
Adopting best practices for SSH remote IoT devices ensures optimal performance and security. Below are some key recommendations:
Key Recommendations
- Regularly update your Raspberry Pi's operating system and software.
- Monitor SSH logs for suspicious activity.
- Limit SSH access to trusted IP addresses.
- Use firewall rules to restrict unnecessary traffic.
Implementing these practices will help safeguard your IoT devices and maintain a secure environment.
Troubleshooting Common SSH Issues
Encountering issues with SSH is not uncommon, especially when working with IoT devices. Below are some common problems and their solutions:
Common Issues and Solutions
- Connection Refused: Ensure that SSH is enabled and the service is running.
- Authentication Failure: Verify that your credentials or keys are correct.
- Timeout Errors: Check your network connectivity and firewall settings.
By addressing these issues promptly, you can maintain uninterrupted SSH connectivity for your IoT devices.
Case Studies: Real-World Applications of Raspberry Pi SSH
Raspberry Pi SSH remote IoT setups have been successfully implemented in various industries. Below are two case studies highlighting their practical applications:
Case Study 1: Smart Home Automation
A homeowner utilized Raspberry Pi with SSH to automate lighting, climate control, and security systems. By configuring SSH, they were able to remotely monitor and manage their smart home devices, enhancing convenience and energy efficiency.
Case Study 2: Environmental Monitoring
A research team deployed Raspberry Pi SSH-enabled devices to collect environmental data in remote locations. The ability to securely access these devices remotely allowed them to gather critical information without physically visiting the sites.
Future Trends in SSH and IoT
The future of SSH in IoT looks promising, with advancements in encryption, authentication, and automation driving innovation. As more devices become interconnected, the demand for secure and efficient remote management solutions will continue to grow.
Emerging technologies such as quantum cryptography and blockchain may further enhance SSH security, offering new possibilities for IoT applications. Staying informed about these developments will enable users to leverage the full potential of SSH remote IoT devices.
Conclusion and Call to Action
In conclusion, SSH remote IoT devices, particularly those based on Raspberry Pi, offer unparalleled opportunities for secure and efficient remote management. By following the guidelines and best practices outlined in this article, you can unlock the full potential of your IoT projects.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into IoT and related technologies. Together, let's build a smarter, more connected future!