In today's interconnected world, remotely accessing IoT devices has become a crucial aspect of modern technology. Whether you're a developer, a system administrator, or an entrepreneur, understanding how to securely and efficiently manage IoT devices is essential. This article delves into the best practices for remotely accessing IoT devices via SSH on web platforms and AWS, ensuring your operations are both secure and scalable.
As more devices connect to the internet, the need for remote management grows exponentially. However, with this convenience comes the responsibility to implement robust security measures. This article will guide you through the process of setting up secure remote access to IoT devices, leveraging SSH and AWS infrastructure.
By the end of this article, you will have a comprehensive understanding of the tools, techniques, and best practices to manage your IoT devices remotely while maintaining the highest standards of security and reliability.
Read also:Inigo Montoya Portrayed By The Iconic Character And His Legacy In Film
Table of Contents
- Introduction to Remote IoT Access
- What Are IoT Devices?
- Understanding SSH for IoT Devices
- Implementing Web-Based SSH Access
- AWS Solutions for IoT Remote Access
- Security Best Practices for IoT Remote Access
- Ensuring Scalability in IoT Management
- Recommended Tools for IoT Remote Access
- Common Issues and Troubleshooting
- Future Trends in IoT Remote Access
Introduction to Remote IoT Access
Remote access to IoT devices has transformed the way businesses and individuals manage their connected devices. The ability to monitor, configure, and troubleshoot devices from anywhere in the world is a game-changer. However, the best remotely access IoT devices require careful planning and execution to ensure security and reliability.
Why Is Remote Access Important?
Remote access allows administrators to perform maintenance, update firmware, and resolve issues without being physically present. This not only saves time but also reduces operational costs. Additionally, with the rise of cloud platforms like AWS, remote access has become more scalable and efficient.
What Are IoT Devices?
IoT devices refer to any physical objects embedded with sensors, software, and connectivity features that allow them to exchange data with other devices and systems over the internet. These devices range from simple sensors to complex industrial equipment.
Types of IoT Devices
- Consumer Devices: Smart home devices, wearables, and smart appliances.
- Industrial Devices: Machinery, robotics, and manufacturing equipment.
- Enterprise Devices: Networked printers, security systems, and office automation tools.
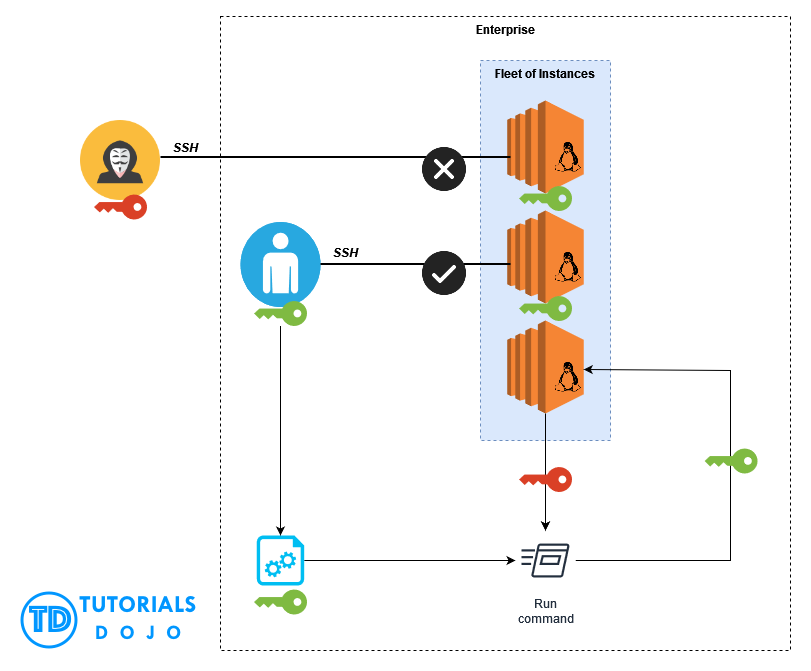
Understanding SSH for IoT Devices
Secure Shell (SSH) is a cryptographic network protocol that provides secure communication over an unsecured network. It is widely used for remote login and other secure network services.
Key Features of SSH
- Encryption: Protects data in transit from unauthorized access.
- Authentication: Ensures only authorized users can access the system.
- Integrity: Verifies that the data has not been tampered with during transmission.
Implementing Web-Based SSH Access
Web-based SSH access allows users to connect to IoT devices through a web browser, eliminating the need for specialized software. This approach is particularly useful for mobile users who may not have access to traditional SSH clients.
Steps to Set Up Web-Based SSH
- Install an SSH server on your IoT device.
- Configure a reverse proxy to forward traffic to the SSH server.
- Use a web-based SSH client like Gate One or WebSSH.
AWS Solutions for IoT Remote Access
Amazon Web Services (AWS) offers a range of tools and services to facilitate remote access to IoT devices. These solutions are designed to be secure, scalable, and easy to integrate with existing infrastructure.
Read also:Martha Scott Lawyer The Definitive Guide To Her Legal Expertise And Impact
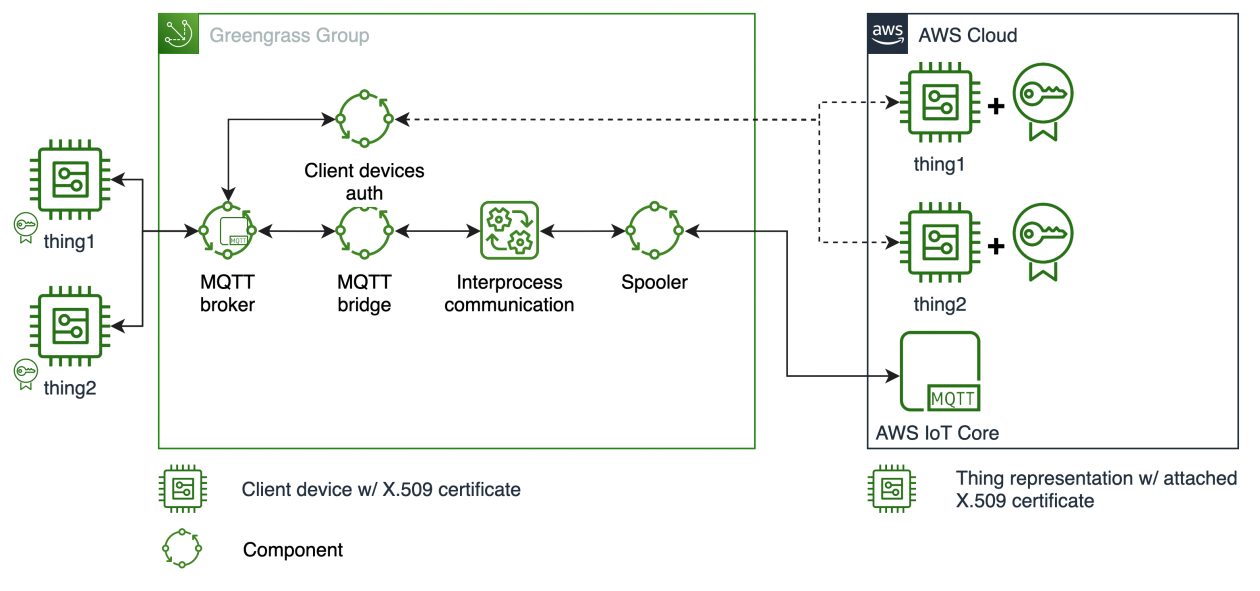
AWS IoT Core
AWS IoT Core is a managed cloud service that allows connected devices to securely interact with cloud applications and other devices. It supports MQTT, HTTP, and WebSocket protocols, making it a versatile choice for IoT projects.
Security Best Practices for IoT Remote Access
Security should always be a top priority when managing IoT devices remotely. Below are some best practices to ensure your devices remain protected:
1. Use Strong Authentication
Implement multi-factor authentication (MFA) to add an extra layer of security to your SSH connections.
2. Regularly Update Firmware
Keep your IoT devices' firmware up to date to protect against known vulnerabilities.
3. Monitor Access Logs
Regularly review access logs to detect and respond to suspicious activity.
Ensuring Scalability in IoT Management
As the number of IoT devices grows, so does the need for scalable solutions. AWS provides the infrastructure needed to manage large-scale IoT deployments effectively.
Scalability Tips
- Use auto-scaling groups to handle increased loads.
- Implement load balancers to distribute traffic evenly.
- Utilize cloud storage solutions for data management.
Recommended Tools for IoT Remote Access
Several tools can enhance your ability to manage IoT devices remotely. Below are some popular options:
1. PuTTY
PuTTY is a free and open-source SSH client that supports various protocols, including SSH, Telnet, and Rlogin.
2. Mosh
Mosh (Mobile Shell) is a replacement for SSH that supports intermittent connectivity, making it ideal for mobile users.
3. AWS IoT Device Management
This service provides tools for provisioning, monitoring, and remotely managing IoT devices at scale.
Common Issues and Troubleshooting
Even with the best planning, issues can arise when remotely accessing IoT devices. Below are some common problems and their solutions:
Connection Errors
If you encounter connection errors, check the following:
- Ensure the device is online and reachable.
- Verify that the SSH server is running on the device.
- Check firewall settings to ensure they are not blocking the connection.
Future Trends in IoT Remote Access
The field of IoT remote access is constantly evolving, with new technologies and trends emerging regularly. Some key trends to watch include:
1. Edge Computing
Edge computing brings processing power closer to the source of data, reducing latency and improving performance.
2. Artificial Intelligence
AI is being integrated into IoT systems to enable predictive maintenance and enhance operational efficiency.
3. Quantum Computing
While still in its infancy, quantum computing has the potential to revolutionize IoT security and data processing.
Conclusion
In conclusion, the best remotely access IoT devices via SSH on web and AWS requires a combination of technical expertise, security awareness, and scalable infrastructure. By following the best practices outlined in this article, you can ensure your IoT devices are managed securely and efficiently.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies.
References: