In today's interconnected world, securely connecting remote IoT devices through a Virtual Private Cloud (VPC) using a Raspberry Pi has become a critical need for individuals and businesses alike. With the growing reliance on IoT technology, ensuring secure communication between devices is no longer optional—it's essential.
The concept of securely connect remote IoT VPC Raspberry Pi free download revolves around creating a robust and encrypted network infrastructure that allows IoT devices to communicate safely over the internet. This setup not only protects sensitive data but also enhances the overall performance of your IoT ecosystem.
Whether you're a tech enthusiast, a small business owner, or an enterprise IT manager, understanding how to implement this solution can significantly improve your network's security and efficiency. In this comprehensive guide, we'll explore everything you need to know about securely connecting IoT devices via VPC using a Raspberry Pi, including step-by-step instructions, best practices, and free resources for downloading necessary tools.
Read also:Who Is Adam Schiffs Wife Exploring The Life And Legacy Of Eve Schiff
Table of Contents:
- Introduction to IoT and VPC
- Raspberry Pi Basics
- Understanding VPC Architecture
- Securing IoT Devices
- Establishing Remote Connections
- Free Download Options
- Best Practices for Secure Connections
- Troubleshooting Common Issues
- Case Studies
- Conclusion and Call to Action
Introduction to IoT and VPC
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart home devices to industrial automation systems, IoT devices are everywhere. However, as these devices become more prevalent, so do the security risks associated with them.
Why Security Matters in IoT
IoT devices often transmit sensitive data, such as personal information, health metrics, or financial transactions. Without proper security measures, this data can be intercepted by malicious actors, leading to privacy breaches and financial losses. This is where Virtual Private Cloud (VPC) comes into play.
A VPC provides a secure and isolated environment for your IoT devices, ensuring that all communications are encrypted and protected from unauthorized access. By integrating a Raspberry Pi into this setup, you can create a cost-effective and scalable solution for managing your IoT network.
Raspberry Pi Basics
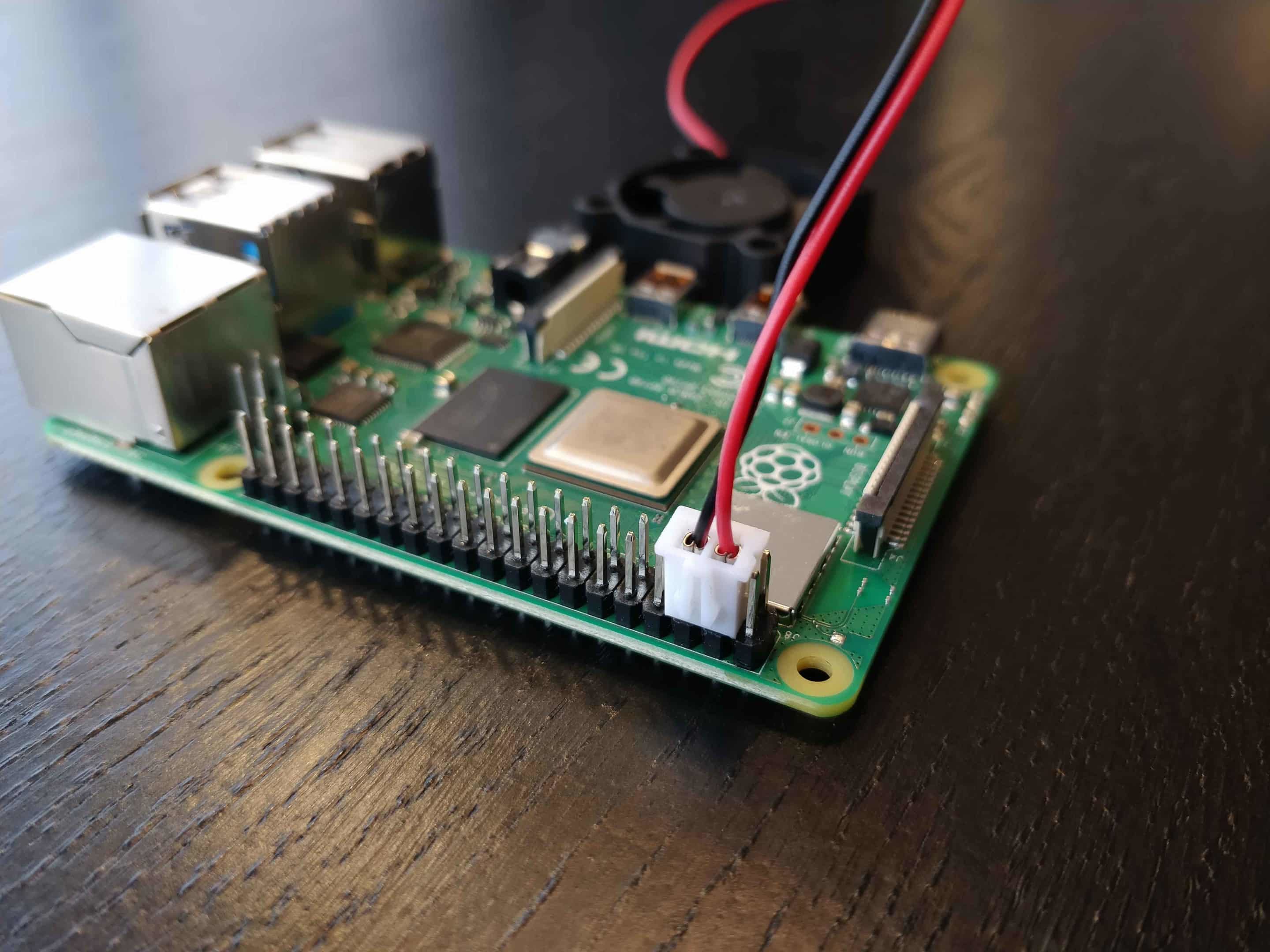
The Raspberry Pi is a powerful yet affordable single-board computer that has gained immense popularity among hobbyists, developers, and businesses. Its versatility makes it an ideal choice for implementing IoT solutions.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems, including Linux
- GPIO pins for interfacing with external devices
- Extensive community support and documentation
When used in conjunction with a VPC, the Raspberry Pi can act as a gateway for securely connecting IoT devices, enabling seamless communication between them.
Read also:Otto Kilcher Death A Comprehensive Look Into The Life And Tragic End Of An Iconic Figure
Understanding VPC Architecture
A Virtual Private Cloud (VPC) is a virtual network dedicated to your AWS account. It enables you to launch AWS resources into a virtual network that you define, providing complete control over your network configuration.
Components of a VPC
- Subnets: Logical subdivisions of your VPC that allow you to group resources based on security and operational needs.
- Security Groups: Act as virtual firewalls for your instances, controlling inbound and outbound traffic.
- Route Tables: Determine how traffic is directed within and outside your VPC.
By configuring these components correctly, you can ensure that your IoT devices are securely connected within the VPC.
Securing IoT Devices
Securing IoT devices involves implementing a combination of hardware, software, and network-level measures. Here are some best practices to consider:
Encryption and Authentication
Encrypting data in transit and at rest is crucial for protecting sensitive information. Additionally, implementing strong authentication mechanisms, such as multi-factor authentication (MFA), can prevent unauthorized access to your devices.
Regular Updates and Patching
Keeping your devices and software up to date with the latest security patches is essential for mitigating vulnerabilities. Automating this process can help ensure that your devices remain secure over time.
Establishing Remote Connections
Establishing secure remote connections is a critical aspect of managing IoT devices. Using a Raspberry Pi as a gateway, you can create a secure tunnel between your local network and the VPC.
SSH Tunneling
Secure Shell (SSH) tunneling allows you to securely connect to your Raspberry Pi from a remote location. By configuring SSH with key-based authentication, you can ensure that only authorized users can access your device.
VPN Configuration
Setting up a Virtual Private Network (VPN) on your Raspberry Pi provides an additional layer of security for remote connections. This ensures that all traffic between your device and the VPC is encrypted and protected from eavesdropping.
Free Download Options
There are several free resources available for downloading the necessary software and tools to securely connect IoT devices via VPC using a Raspberry Pi. Some popular options include:
Official Raspberry Pi OS
The official Raspberry Pi operating system is available for free download from the Raspberry Pi Foundation website. It includes all the necessary tools and utilities for setting up your device.
OpenVPN
OpenVPN is a widely used open-source VPN solution that can be easily installed on your Raspberry Pi. It provides robust encryption and authentication features, making it an ideal choice for securing remote connections.
Best Practices for Secure Connections
Implementing best practices is essential for ensuring the security and reliability of your IoT network. Here are some tips to consider:
Network Segmentation
Segmenting your network into smaller, isolated subnets can help limit the impact of a potential security breach. By separating IoT devices from other network resources, you can reduce the risk of lateral movement by attackers.
Monitoring and Logging
Implementing comprehensive monitoring and logging solutions can help you detect and respond to security incidents in real time. Regularly reviewing logs can also provide valuable insights into potential vulnerabilities.
Troubleshooting Common Issues
Even with the best-laid plans, issues can arise when setting up a secure IoT network. Here are some common problems and their solutions:
Connection Failures
If you're experiencing connection failures, check your network configuration and ensure that all security groups and route tables are correctly set up. Additionally, verify that your SSH or VPN settings are configured properly.
Performance Issues
Performance issues can often be attributed to insufficient resources or misconfigured settings. Consider upgrading your Raspberry Pi or optimizing your network configuration to improve performance.
Case Studies
Real-world examples can provide valuable insights into the practical applications of securely connecting IoT devices via VPC using a Raspberry Pi. Here are a few case studies to consider:
Smart Home Automation
A homeowner successfully implemented a secure IoT network using a Raspberry Pi and VPC, enabling them to remotely control and monitor their smart home devices. This setup not only improved convenience but also enhanced the security of their home network.
Industrial IoT
An industrial manufacturer leveraged this solution to securely connect their IoT sensors and devices, enabling real-time monitoring and analysis of production processes. This resulted in increased efficiency and reduced downtime.
Conclusion and Call to Action
Securing IoT devices through a Virtual Private Cloud (VPC) using a Raspberry Pi is a powerful solution for protecting sensitive data and enhancing network performance. By following the best practices outlined in this guide and utilizing the free resources available, you can create a robust and secure IoT ecosystem.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore our other articles for more information on IoT security and related topics. Together, let's build a safer and more connected future!