Connecting remote IoT devices to your Virtual Private Cloud (VPC) using Raspberry Pi is becoming increasingly popular, especially for those looking to secure their systems without breaking the bank. As technology advances, more individuals and businesses are turning to IoT solutions to streamline operations and enhance efficiency. However, ensuring secure connections is paramount to protect sensitive data and prevent unauthorized access.
In today's digital landscape, leveraging tools like Raspberry Pi offers a cost-effective and flexible solution for managing IoT networks. With the ability to run on free software, Raspberry Pi enables users to create robust systems tailored to their needs. Whether you're a hobbyist or a professional developer, securing your IoT infrastructure is a critical step toward maintaining system integrity.
This comprehensive guide explores how to securely connect remote IoT devices to a VPC using Raspberry Pi, complete with free download options for Windows users. We'll delve into the necessary steps, tools, and best practices to help you build a reliable and secure IoT network. By the end of this article, you'll have the knowledge and resources to implement your own IoT solution.
Read also:Clapperleaks Unveiling The Truth Behind The Whistleblowing Sensation
Table of Contents
- Introduction to IoT and VPC
- Raspberry Pi Basics
- How to Securely Connect IoT Devices
- Setting Up a Virtual Private Cloud
- Free Download Options for Windows
- Designing Network Architecture
- Best Practices for IoT Security
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Conclusion and Next Steps
Introduction to IoT and VPC
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. IoT devices range from simple sensors to complex industrial machinery, all designed to enhance automation and efficiency. A Virtual Private Cloud (VPC) is a private cloud hosted within a larger public cloud infrastructure, offering enhanced security and control over resources.
Connecting IoT devices to a VPC is essential for businesses and individuals who prioritize data security and scalability. By leveraging VPCs, users can isolate their IoT devices from public networks, reducing the risk of cyberattacks. Additionally, VPCs provide the flexibility to manage resources dynamically, ensuring optimal performance and cost efficiency.
Why Secure IoT Connections Matter
IoT devices are often vulnerable to cyber threats due to their limited processing power and lack of built-in security features. Securely connecting these devices to a VPC is crucial for protecting sensitive data and maintaining system integrity. By implementing robust security measures, users can prevent unauthorized access and ensure the reliability of their IoT networks.
Raspberry Pi Basics
Raspberry Pi is a credit-card-sized single-board computer that has gained immense popularity among hobbyists and developers. It offers a low-cost, energy-efficient platform for running various applications, including IoT solutions. Raspberry Pi can be used to connect IoT devices to a VPC, providing a secure and reliable gateway for data transmission.
Key Features of Raspberry Pi
- Compact size and lightweight design
- Support for multiple operating systems, including Linux and Windows
- Low power consumption
- Extensive community support and resources
How to Securely Connect IoT Devices
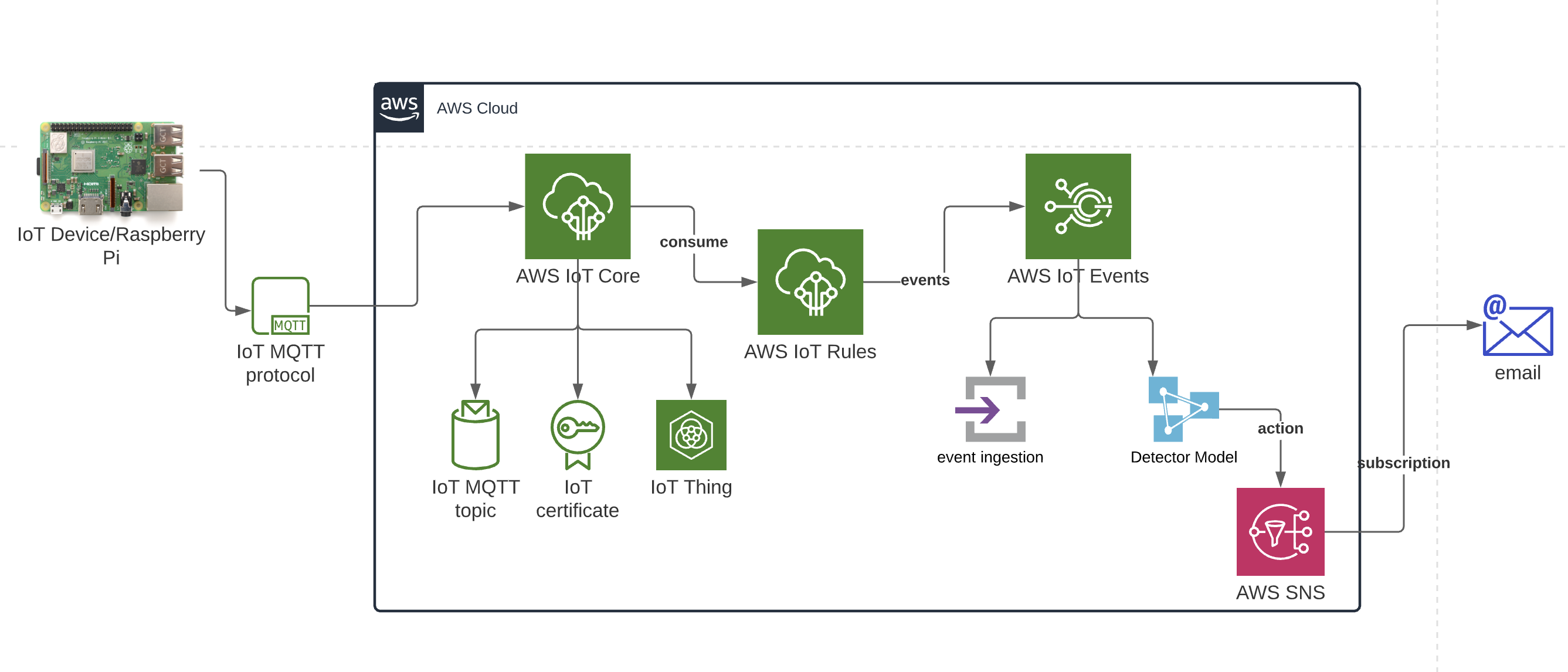
Securing IoT devices involves implementing a combination of hardware, software, and network-level protections. One effective approach is to use a Raspberry Pi as a secure gateway between IoT devices and a VPC. This setup ensures that data is transmitted securely and remains isolated from external threats.
Steps to Secure IoT Connections
- Set up a Raspberry Pi with a secure operating system
- Configure network settings to enable secure communication
- Implement encryption protocols such as SSL/TLS
- Regularly update software and firmware to address vulnerabilities
Setting Up a Virtual Private Cloud
Setting up a VPC involves configuring network settings to create a private, isolated environment for your IoT devices. This process typically includes defining subnets, access control lists, and security groups to ensure secure communication within the VPC.
Read also:Is Kamala Harris An Alcoholic Debunking Myths And Understanding The Truth
Steps to Configure a VPC
- Create a VPC with a defined IP range
- Set up subnets for different device groups
- Configure security groups to control inbound and outbound traffic
- Monitor network activity using logging and analytics tools
Free Download Options for Windows
Windows users can take advantage of free software and tools to set up their IoT VPC environment. Popular options include open-source operating systems like Raspbian and Ubuntu, which can be installed on a Raspberry Pi. Additionally, tools such as PuTTY and WinSCP enable users to remotely manage their Raspberry Pi devices from a Windows computer.
Recommended Downloads
- Raspbian OS for Raspberry Pi
- PuTTY for remote SSH connections
- WinSCP for secure file transfers
Designing Network Architecture
Designing a robust network architecture is essential for ensuring secure and efficient IoT communication. This involves planning the layout of devices, determining data flow, and implementing security measures at each layer of the network.
Key Considerations for Network Design
- Device placement and connectivity
- Data encryption and authentication
- Redundancy and failover mechanisms
- Monitoring and logging for anomaly detection
Best Practices for IoT Security
Implementing best practices for IoT security can significantly reduce the risk of cyberattacks and data breaches. Some key strategies include regular software updates, strong authentication mechanisms, and network segmentation.
Top IoT Security Practices
- Use strong, unique passwords for all devices
- Enable multi-factor authentication wherever possible
- Segment networks to isolate critical devices
- Regularly audit and update security policies
Troubleshooting Common Issues
Even with the best planning, issues may arise when setting up an IoT VPC environment. Common problems include connectivity issues, software conflicts, and misconfigured settings. Troubleshooting these issues requires a systematic approach and access to relevant documentation and support resources.
Solutions for Common Problems
- Check network settings and restart devices
- Consult official documentation for troubleshooting guides
- Reach out to community forums for additional support
Future Trends in IoT Security
The field of IoT security is rapidly evolving, with new technologies and strategies emerging to address emerging threats. Some promising trends include the use of artificial intelligence for threat detection, blockchain for secure data sharing, and quantum encryption for advanced security.
Innovations in IoT Security
- AI-driven threat detection systems
- Blockchain-based data integrity solutions
- Quantum encryption for ultra-secure communications
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices to a VPC using Raspberry Pi is a powerful solution for enhancing data security and network efficiency. By following the steps outlined in this guide, you can create a reliable and secure IoT infrastructure tailored to your needs. Remember to implement best practices for IoT security and stay informed about emerging trends in the field.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore our other articles for more tips and resources on IoT and cybersecurity. Together, we can build a safer and more connected digital world.
Data sources and references: