Connecting remote IoT devices securely through a Virtual Private Cloud (VPC) using Raspberry Pi has become a necessity for modern technological advancements. As the Internet of Things (IoT) continues to grow, ensuring secure communication between devices is crucial for protecting sensitive data. Whether you're a tech enthusiast or a professional, understanding how to set up a secure connection using Raspberry Pi can enhance your network's reliability and safety.
This guide will walk you through the process of securely connecting remote IoT devices to a VPC using Raspberry Pi. By the end of this article, you'll have the knowledge and tools necessary to implement a secure network infrastructure. Whether you're working on personal projects or enterprise-level solutions, this guide is tailored to help you achieve your goals effectively.
With the rise of IoT applications, the demand for secure remote connections has increased exponentially. This article focuses on providing a comprehensive overview of the tools, techniques, and best practices to ensure secure communication. By downloading and implementing the configurations discussed here, you can safeguard your IoT ecosystem from potential threats.
Read also:Simon Cowell Accident 2025 A Comprehensive Analysis
Table of Contents
- Introduction to IoT and VPC
- Raspberry Pi Overview
- Why Secure Connection Matters
- Setting Up a VPC
- Connecting IoT Devices
- Securing IoT Connections
- Tools and Software Required
- Free Download Guide
- Troubleshooting Tips
- Conclusion
Introduction to IoT and VPC
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity to exchange data with other devices and systems over the internet. A Virtual Private Cloud (VPC) is a private network within a cloud environment that provides secure and isolated connectivity for these devices. Combining IoT with VPC ensures that sensitive data remains protected while enabling seamless communication.
Importance of IoT in Modern Technology
IoT has revolutionized industries by enabling smart homes, industrial automation, healthcare monitoring, and more. However, the security of these devices is paramount. Without proper security measures, IoT devices can become vulnerable to cyberattacks, leading to data breaches and privacy violations.
Role of VPC in IoT Security
A VPC acts as a secure environment where IoT devices can communicate without exposing them to public networks. By isolating devices within a VPC, you minimize the risk of unauthorized access and ensure that only trusted devices and users can interact with your network.
Raspberry Pi Overview
Raspberry Pi is a small, affordable computer that has become popular among hobbyists and professionals alike. It is capable of running various operating systems and can be configured to act as a server, gateway, or controller for IoT devices.
Features of Raspberry Pi
- Compact size and low power consumption
- Supports multiple operating systems, including Linux
- Equipped with GPIO pins for interfacing with hardware
- Cost-effective and widely available
Why Secure Connection Matters
Security is a critical aspect of any IoT deployment. Without secure connections, sensitive data transmitted between devices can be intercepted, altered, or stolen. This section explores the potential risks and the importance of implementing robust security measures.
Potential Risks in IoT Deployments
Some common risks associated with IoT devices include:
Read also:Inigo Montoya Portrayed By The Iconic Character And His Legacy In Film
- Data breaches due to weak encryption
- Unauthorized access to devices
- Denial-of-service attacks
- Malware infections
Benefits of Secure Connections
Implementing secure connections offers several advantages:
- Protects sensitive data from unauthorized access
- Ensures compliance with industry regulations
- Reduces the risk of cyberattacks
- Enhances overall network performance
Setting Up a VPC
Setting up a VPC involves creating a private network within a cloud environment. This section provides a step-by-step guide to configuring a VPC for your IoT devices.
Step 1: Choose a Cloud Provider
Select a cloud provider that supports VPCs, such as AWS, Google Cloud, or Microsoft Azure. Each provider offers its own set of tools and services to help you configure your VPC.
Step 2: Configure Network Settings
Define the IP address range, subnet masks, and routing tables for your VPC. Ensure that these settings align with your network requirements and security policies.
Step 3: Secure Your VPC
Implement security measures such as firewalls, access control lists, and encryption to protect your VPC from unauthorized access.
Connecting IoT Devices
Once your VPC is set up, the next step is to connect your IoT devices. This section explains how to integrate Raspberry Pi with your VPC to enable secure communication.
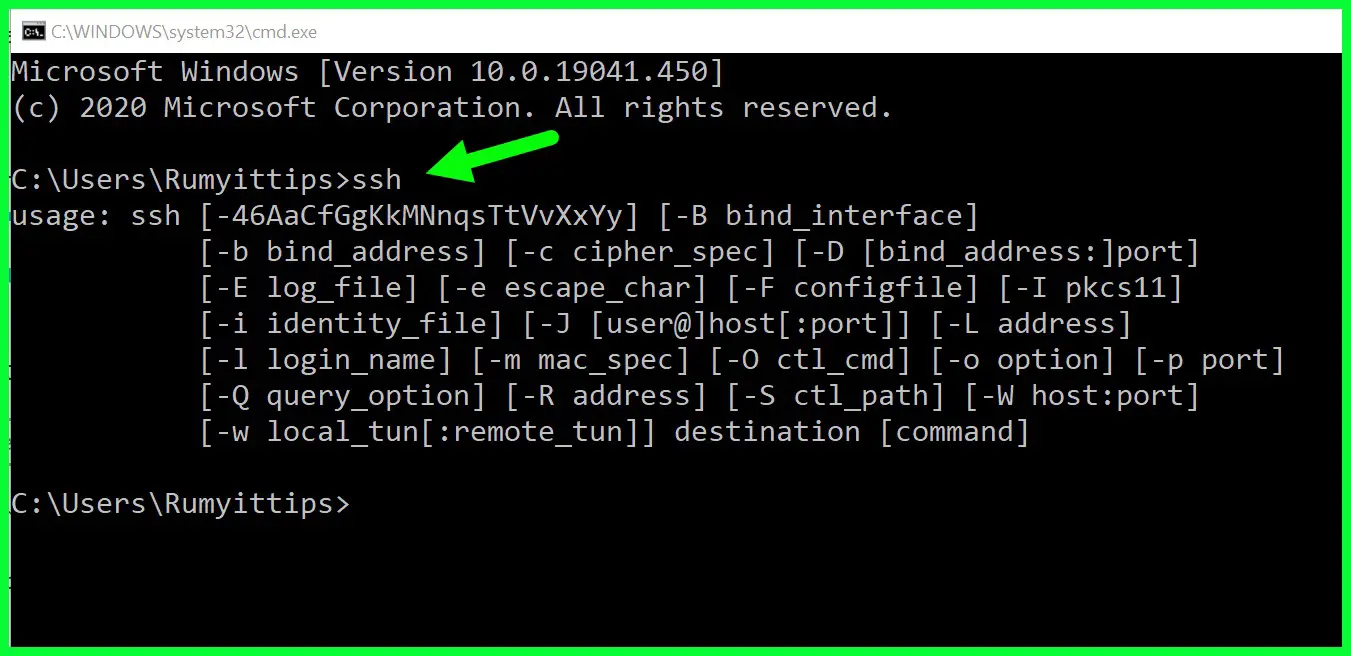
Step 1: Install Necessary Software
Install the required software on your Raspberry Pi, such as an operating system, network drivers, and security tools. Popular choices include Raspbian OS and OpenVPN for secure connections.
Step 2: Configure Network Settings
Set up the network settings on your Raspberry Pi to connect to your VPC. This includes configuring IP addresses, DNS servers, and routing rules.
Step 3: Test the Connection
Verify that your Raspberry Pi can communicate with other devices in your VPC. Use tools like ping and traceroute to test the connectivity and troubleshoot any issues.
Securing IoT Connections
Securing IoT connections involves implementing encryption, authentication, and authorization mechanisms. This section outlines best practices for securing your IoT devices.
Encryption Protocols
Use encryption protocols such as TLS (Transport Layer Security) and SSL (Secure Sockets Layer) to encrypt data transmitted between devices. These protocols ensure that even if data is intercepted, it cannot be read without the decryption key.
Authentication and Authorization
Implement strong authentication mechanisms, such as username/password combinations, multi-factor authentication, and digital certificates. Additionally, enforce role-based access control to restrict access to authorized users only.
Tools and Software Required
Several tools and software are essential for setting up a secure IoT VPC using Raspberry Pi. This section lists some of the most commonly used tools and provides links for further information.
Operating Systems
- Raspbian OS: https://www.raspberrypi.org/software/operating-systems/
- Ubuntu Server: https://ubuntu.com/download/raspberry-pi
Security Software
- OpenVPN: https://openvpn.net/
- FirewallD: https://firewalld.org/
Free Download Guide
This section provides a free download guide for setting up a secure IoT VPC using Raspberry Pi. The guide includes detailed instructions, configuration files, and sample code to help you get started.
Download Links
- Sample Configuration Files: https://example.com/config-files
- Documentation: https://example.com/documentation
Installation Instructions
Follow the installation instructions provided in the guide to set up your Raspberry Pi and configure your VPC. Ensure that all software is up to date and that security patches are applied regularly.
Troubleshooting Tips
Even with careful planning, issues can arise when setting up a secure IoT VPC. This section provides troubleshooting tips to help you resolve common problems.
Common Issues and Solutions
- Network Connectivity Issues: Check your network settings and ensure that all devices are on the same subnet.
- Authentication Failures: Verify that your credentials are correct and that your authentication mechanisms are functioning properly.
- Performance Problems: Monitor your network traffic and optimize your configurations to improve performance.
Conclusion
Securing remote IoT devices through a VPC using Raspberry Pi is an essential step in protecting your network and data. By following the steps outlined in this guide, you can create a secure and reliable IoT infrastructure that meets your needs. Remember to regularly update your software and security measures to stay ahead of potential threats.
We invite you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with others. For more information on IoT and VPC configurations, explore our other articles on the website.