In the era of the Internet of Things (IoT), securely connecting remote devices to a Virtual Private Cloud (VPC) using Raspberry Pi has become a critical need for businesses and individuals alike. As IoT devices continue to proliferate, ensuring secure connections is paramount to protect sensitive data and maintain privacy. This guide will walk you through the steps to securely connect remote IoT devices to a VPC using Raspberry Pi, ensuring robust security and seamless performance.
The integration of IoT devices into enterprise and home networks has brought convenience and efficiency. However, it has also introduced significant security challenges. The ability to securely connect these devices is not just a technical requirement but a necessity to safeguard against cyber threats. This article will delve into the nuances of setting up a secure connection for remote IoT devices using Raspberry Pi and provide actionable insights.
Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge and tools to establish a secure VPC connection for your IoT devices. By the end of this article, you'll have a clear understanding of the steps involved, potential pitfalls, and best practices to ensure your IoT network remains protected.
Read also:Is Lester Holt Ill Unveiling The Truth Behind The Rumors
Table of Contents
- Introduction to Secure IoT Connections
- Raspberry Pi: An Overview
- What is a Virtual Private Cloud (VPC)?
- IoT Security Challenges
- Steps to Securely Connect Remote IoT Devices
- Using Encryption for Enhanced Security
- Configuring Firewalls for IoT Security
- Network Segmentation for IoT Devices
- Setting Up Raspberry Pi for IoT Connections
- Downloading Necessary Software for Raspberry Pi
- Best Practices for IoT Security
- Future Trends in IoT Security
- Conclusion
Introduction to Secure IoT Connections
IoT devices have transformed the way we interact with technology, enabling smart homes, industrial automation, and wearable devices. However, the exponential growth of IoT devices has also raised concerns about security. The secure connection of remote IoT devices to a VPC using Raspberry Pi is a critical step in addressing these security concerns.
By leveraging Raspberry Pi's capabilities, businesses and individuals can establish a secure VPC environment that protects IoT devices from unauthorized access. This section will explore the importance of secure IoT connections and the role Raspberry Pi plays in achieving this goal.
Raspberry Pi: An Overview
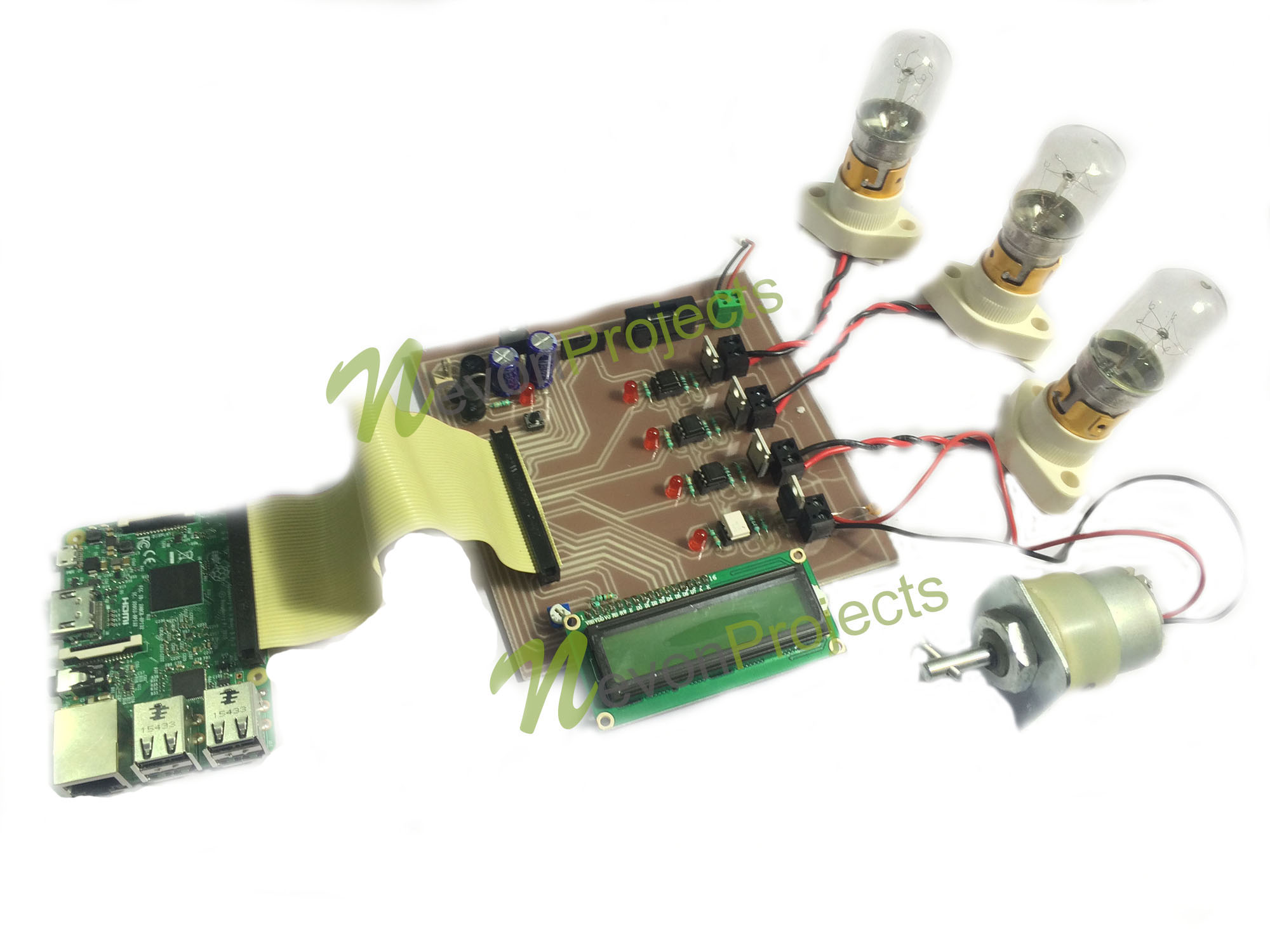
Raspberry Pi is a credit-card-sized single-board computer that has gained immense popularity among developers, hobbyists, and educators. Its versatility and affordability make it an ideal platform for IoT projects. Raspberry Pi can act as a gateway for IoT devices, enabling secure communication between devices and the cloud.
Key Features of Raspberry Pi
- Compact and cost-effective hardware
- Supports multiple operating systems, including Linux-based distributions
- Equipped with GPIO pins for interfacing with sensors and actuators
- Highly customizable and programmable
Raspberry Pi's ability to run lightweight server software makes it an excellent choice for setting up secure IoT connections.
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a logically isolated section of a cloud environment that provides secure and private connectivity for IoT devices. By using a VPC, organizations can control access to their IoT devices and manage network traffic more effectively.
VPCs offer several advantages, including:
Read also:Is Bill Oreilly Married Today A Comprehensive Look At His Personal Life And Career
- Enhanced security through network isolation
- Flexible configuration options
- Scalability to accommodate growing IoT networks
Connecting IoT devices to a VPC ensures that sensitive data remains protected from external threats.
IoT Security Challenges
Despite the numerous benefits of IoT devices, they come with significant security challenges. These challenges include:
Common IoT Security Issues
- Weak authentication mechanisms
- Lack of encryption for data transmission
- Vulnerabilities in firmware and software
- Insufficient network segmentation
Addressing these challenges requires a comprehensive security strategy that includes secure connections, regular updates, and robust authentication protocols.
Steps to Securely Connect Remote IoT Devices
Establishing a secure connection for remote IoT devices involves several key steps. Below is a detailed breakdown of the process:
Step 1: Configure Raspberry Pi
Begin by setting up Raspberry Pi with the necessary operating system and software. Ensure that all security updates are installed and that the device is configured for optimal performance.
Step 2: Set Up a VPC
Create a VPC in your cloud provider's environment, ensuring that it is properly configured to support IoT devices. Define subnets, security groups, and access control lists to enhance security.
Step 3: Connect IoT Devices
Link your IoT devices to Raspberry Pi, ensuring that all communication is encrypted. Use secure protocols such as MQTT or HTTPS to transmit data.
By following these steps, you can establish a secure connection for your IoT devices, minimizing the risk of cyberattacks.
Using Encryption for Enhanced Security
Encryption is a fundamental component of IoT security. By encrypting data transmitted between IoT devices and the VPC, you can protect sensitive information from unauthorized access.
Types of Encryption Protocols
- TLS/SSL for secure communication
- AES for data encryption
- SSH for secure remote access
Implementing these protocols on Raspberry Pi ensures that all data transmitted through the VPC remains encrypted and secure.
Configuring Firewalls for IoT Security
Firewalls play a crucial role in securing IoT devices by controlling incoming and outgoing network traffic. Configuring firewalls on Raspberry Pi can help protect against unauthorized access and potential threats.
Best Practices for Firewall Configuration
- Use iptables for advanced firewall management
- Restrict access to specific IP addresses
- Monitor network traffic for suspicious activity
By implementing these practices, you can enhance the security of your IoT network.
Network Segmentation for IoT Devices
Network segmentation involves dividing a network into smaller, isolated segments to improve security and performance. By segmenting IoT devices, you can limit the spread of potential threats and ensure that sensitive data remains protected.
Benefits of Network Segmentation
- Reduces attack surface
- Improves network performance
- Facilitates easier management
Implementing network segmentation on Raspberry Pi can significantly enhance the security of your IoT network.
Setting Up Raspberry Pi for IoT Connections
Setting up Raspberry Pi for IoT connections involves several steps, including installing the operating system, configuring network settings, and securing the device. Below is a detailed guide:
Step 1: Install the Operating System
Download and install a lightweight operating system such as Raspbian or Ubuntu Server on your Raspberry Pi. Ensure that all security updates are applied.
Step 2: Configure Network Settings
Set up Wi-Fi or Ethernet connections for your Raspberry Pi, ensuring that it can communicate with your IoT devices and the VPC.
Step 3: Secure the Device
Implement security measures such as strong passwords, firewalls, and encryption to protect your Raspberry Pi from unauthorized access.
By following these steps, you can ensure that your Raspberry Pi is properly configured for IoT connections.
Downloading Necessary Software for Raspberry Pi
To securely connect remote IoT devices to a VPC, you need to download and install specific software on your Raspberry Pi. Below are some essential tools:
Key Software Tools
- MQTT broker for secure communication
- OpenSSL for encryption
- SSH for secure remote access
Downloading and installing these tools will enable you to establish a secure connection for your IoT devices.
Best Practices for IoT Security
Adopting best practices for IoT security is essential to protect your devices and data. Below are some key practices to consider:
Security Best Practices
- Regularly update firmware and software
- Use strong authentication mechanisms
- Monitor network activity for anomalies
- Implement network segmentation
By following these practices, you can ensure that your IoT network remains secure and resilient against cyber threats.
Future Trends in IoT Security
The field of IoT security is rapidly evolving, with new technologies and trends emerging to address existing challenges. Below are some future trends to watch:
Emerging Trends
- AI-driven security solutions
- Blockchain for secure data management
- Zero-trust architecture
These trends will shape the future of IoT security, providing new tools and techniques to protect devices and data.
Conclusion
Securing remote IoT devices through a VPC using Raspberry Pi is a critical step in protecting sensitive data and maintaining privacy. This guide has provided a comprehensive overview of the steps involved, potential challenges, and best practices for achieving secure connections.
We encourage you to implement the strategies outlined in this article to enhance the security of your IoT network. Please feel free to leave comments or questions below, and don't hesitate to share this article with others who may find it useful. For more information on IoT security, explore our other articles on the latest trends and technologies.
References: