Connecting remote IoT devices securely is crucial in today's interconnected world. With the rise of smart devices and edge computing, ensuring the safety of your network and data has never been more important. This article delves into the best practices for securely connecting remote IoT devices using a Virtual Private Cloud (VPC) on Raspberry Pi, including a free download guide to help you get started.
The Internet of Things (IoT) has revolutionized the way we interact with technology. However, the security risks associated with these devices cannot be overlooked. As organizations and individuals adopt IoT solutions, they must prioritize security measures to protect sensitive data and maintain privacy. This article explores how to securely connect remote IoT devices using Raspberry Pi and VPC configurations.
Whether you're a hobbyist, developer, or IT professional, this comprehensive guide will equip you with the knowledge and tools to create a secure IoT environment. From understanding the basics of VPCs to implementing advanced security protocols, this article provides actionable insights and practical tips.
Read also:Rudy From The Cosby Show A Comprehensive Look At The Beloved Character
Understanding IoT Security Challenges
Why IoT Security Matters
The Internet of Things (IoT) involves connecting multiple devices over the internet, enabling them to communicate and share data. While this connectivity offers numerous benefits, it also introduces significant security challenges. IoT devices are often targeted by cybercriminals due to their vulnerabilities, which can lead to data breaches, unauthorized access, and network compromises.
Some common IoT security challenges include:
- Lack of encryption in device communications
- Poor authentication mechanisms
- Outdated firmware and software
- Inadequate network segmentation
Addressing these challenges is critical to ensuring the safety and reliability of IoT ecosystems.
Key Components of IoT Security
To secure IoT devices effectively, it's essential to focus on several key components:
- Data encryption: Protecting data in transit and at rest
- Authentication: Verifying the identity of devices and users
- Network segmentation: Isolating IoT devices from other network segments
- Regular updates: Keeping firmware and software up to date
By addressing these components, organizations can significantly enhance the security of their IoT deployments.
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a logically isolated section of a cloud environment where resources can be securely deployed and managed. VPCs provide a secure and scalable infrastructure for hosting applications and services, making them ideal for IoT deployments.
Read also:Crazyjamjam Fanfix Free The Ultimate Guide For Enthusiasts
Key features of a VPC include:
- Private subnets for secure communication
- Customizable IP address ranges
- Network access control lists (ACLs) for fine-grained security
- Integration with other cloud services
VPCs enable organizations to create a secure and controlled environment for their IoT devices, reducing the risk of unauthorized access and data breaches.
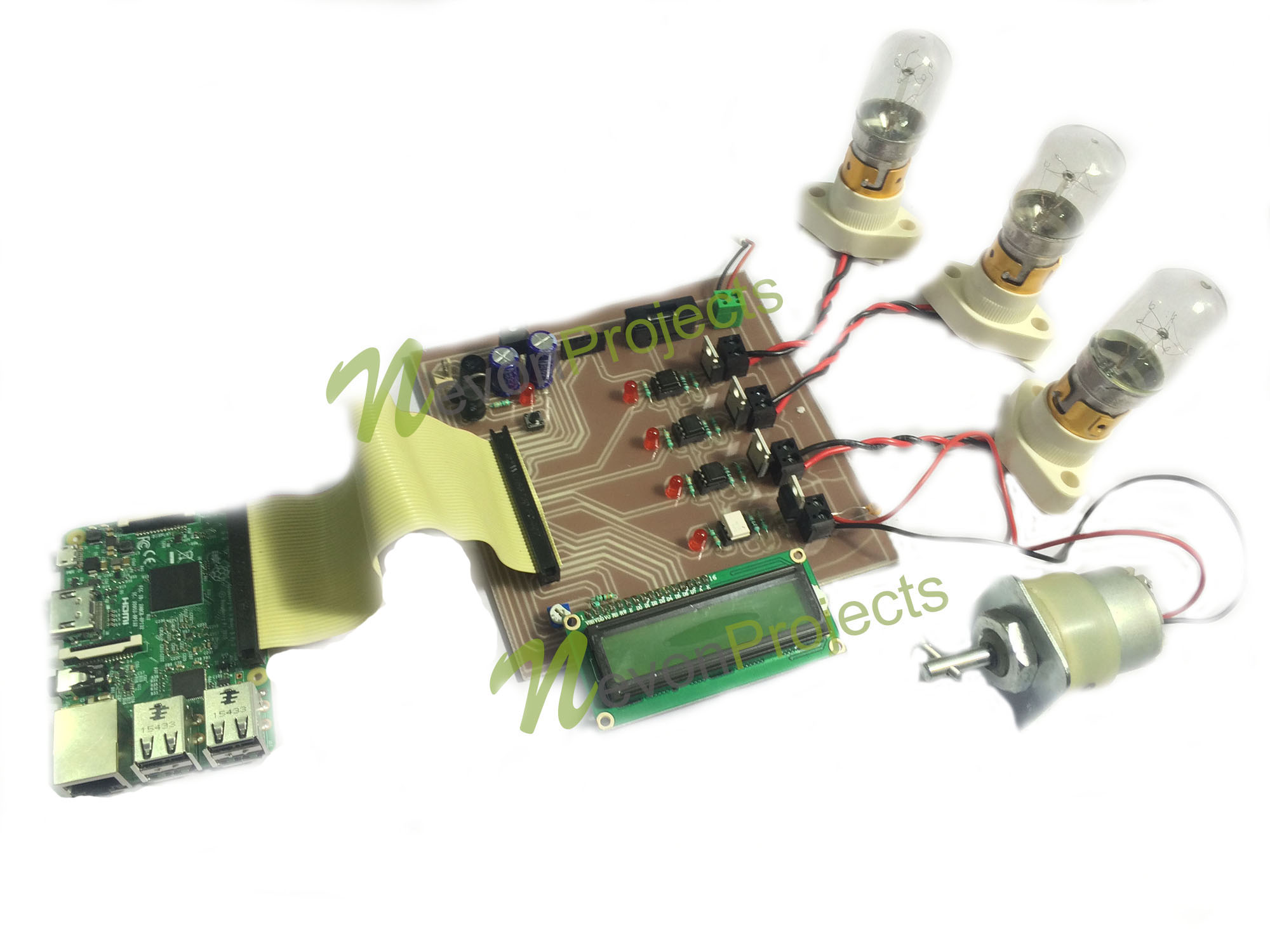
Securing IoT Devices with Raspberry Pi
Why Raspberry Pi?
Raspberry Pi is a versatile and cost-effective single-board computer that has gained popularity among developers and hobbyists. Its small size, low power consumption, and open-source nature make it an ideal platform for IoT projects.
Key advantages of using Raspberry Pi for IoT security include:
- Support for multiple operating systems and programming languages
- Compatibility with a wide range of sensors and peripherals
- Easy integration with cloud services and VPCs
By leveraging Raspberry Pi, users can create custom IoT solutions tailored to their specific needs.
Setting Up Raspberry Pi for IoT Security
Configuring Raspberry Pi for IoT security involves several steps:
- Install a secure operating system, such as Raspbian with full disk encryption
- Enable a firewall and configure network settings
- Install and configure security software, such as fail2ban and ufw
- Regularly update the system and install security patches
These steps ensure that Raspberry Pi is configured securely for IoT applications.
Connecting IoT Devices to a VPC
Steps to Connect IoT Devices Securely
Connecting IoT devices to a VPC involves the following steps:
- Create a VPC in your cloud provider's console
- Set up subnets and security groups for your IoT devices
- Configure network access rules and encryption protocols
- Deploy IoT devices within the VPC and test connectivity
By following these steps, you can ensure that your IoT devices are securely connected to the VPC.
Best Practices for VPC Configuration
When configuring a VPC for IoT devices, consider the following best practices:
- Use private subnets for sensitive devices
- Enable encryption for all data in transit and at rest
- Regularly audit and update security settings
- Monitor network traffic for suspicious activity
Implementing these best practices will help you maintain a secure and reliable VPC environment.
Download Free Guide: Securely Connect Remote IoT VPC Raspberry Pi
To assist you in securing your IoT devices, we have created a free downloadable guide that provides step-by-step instructions for connecting remote IoT devices to a VPC using Raspberry Pi. This guide covers:
- Setting up Raspberry Pi for IoT security
- Configuring a VPC in your cloud provider's console
- Connecting IoT devices securely to the VPC
- Troubleshooting common issues
Click here to download the free guide.
Advanced Security Measures for IoT Devices
Implementing Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) adds an extra layer of security to IoT devices by requiring users to provide multiple forms of identification before gaining access. This can include something the user knows (password), something the user has (smartphone), or something the user is (biometric data).
Implementing MFA for IoT devices can significantly reduce the risk of unauthorized access and data breaches.
Using Blockchain for Secure IoT Communication
Blockchain technology offers a decentralized and tamper-proof method for securing IoT communications. By using blockchain, IoT devices can securely exchange data without relying on a central authority, reducing the risk of man-in-the-middle attacks and data tampering.
Organizations exploring advanced IoT security solutions should consider integrating blockchain into their architectures.
Monitoring and Maintaining IoT Security
Importance of Continuous Monitoring
Securing IoT devices is an ongoing process that requires continuous monitoring and maintenance. Regularly monitoring network traffic, device activity, and system logs can help identify potential security threats and vulnerabilities.
Tools such as intrusion detection systems (IDS) and security information and event management (SIEM) solutions can assist in monitoring and analyzing IoT security data.
Regular Updates and Patch Management
Keeping IoT devices and associated software up to date is critical to maintaining security. Regular updates and patch management ensure that known vulnerabilities are addressed promptly, reducing the risk of exploitation by cybercriminals.
Automating the update process can help streamline this task and ensure that devices remain secure.
Conclusion
In conclusion, securely connecting remote IoT devices using a Virtual Private Cloud (VPC) on Raspberry Pi is essential for maintaining the safety and reliability of IoT ecosystems. By following the best practices outlined in this article and utilizing the free downloadable guide, you can create a secure and scalable IoT environment.
We encourage you to:
- Download the free guide for step-by-step instructions
- Share this article with others who may benefit from the information
- Leave a comment below with your thoughts and questions
Stay informed and proactive in securing your IoT devices to protect sensitive data and maintain privacy.
Table of Contents
- Understanding IoT Security Challenges
- What is a Virtual Private Cloud (VPC)?
- Securing IoT Devices with Raspberry Pi
- Connecting IoT Devices to a VPC
- Download Free Guide: Securely Connect Remote IoT VPC Raspberry Pi
- Advanced Security Measures for IoT Devices
- Monitoring and Maintaining IoT Security
- Conclusion