Connecting remote IoT devices securely is critical for maintaining data integrity and preventing unauthorized access. As the Internet of Things (IoT) continues to grow, the need for robust security measures becomes increasingly important. A Virtual Private Cloud (VPC) combined with Raspberry Pi offers an affordable and efficient solution for remote device management.
In today's connected world, securing IoT devices has become a top priority for businesses and individuals alike. The rise in cyber threats necessitates a secure infrastructure that protects sensitive data and ensures smooth operations. By leveraging technologies such as VPC and Raspberry Pi, users can create a secure environment for their IoT devices.
This article explores how to securely connect remote IoT devices using a VPC and Raspberry Pi, including essential steps for setup and configuration. Whether you're a beginner or an advanced user, this guide will provide valuable insights and practical advice to enhance your IoT security.
Read also:When Did Emily Compagno Get Married A Comprehensive Guide To Her Personal Life And Career
Table of Contents
- Introduction to VPC
- Raspberry Pi Overview
- Why Secure IoT Devices?
- Setting Up a VPC
- Raspberry Pi Configuration
- Connecting Remote IoT Devices
- Securing Your VPC
- Troubleshooting Common Issues
- Best Practices for IoT Security
- Conclusion
Introduction to VPC
A Virtual Private Cloud (VPC) is a private, isolated network environment within a public cloud infrastructure. It allows users to deploy and manage resources securely, ensuring that data remains protected from unauthorized access. VPCs are commonly used in IoT setups to create a secure network for remote devices.
Key features of a VPC include:
- Private subnets for isolating resources
- Customizable IP address ranges
- Network access control lists (ACLs) for enhanced security
- Support for multiple availability zones
By integrating a VPC into your IoT infrastructure, you can ensure that your devices remain secure and operational, even when accessed remotely.
VPC Benefits for IoT
Using a VPC for IoT offers several advantages:
- Improved security through network isolation
- Scalability to accommodate growing numbers of devices
- Flexibility in configuring network settings
- Cost-effective solution for managing remote devices
These benefits make VPC an ideal choice for securing IoT devices in both personal and enterprise environments.
Raspberry Pi Overview
The Raspberry Pi is a small, affordable computer that has gained popularity among hobbyists and professionals alike. Its versatility and ease of use make it an excellent choice for IoT projects, particularly when combined with a VPC for secure remote access.
Read also:Emily Compagno Divorce The Full Story Behind The Headlines
Key features of the Raspberry Pi include:
- Compact form factor
- Low power consumption
- Support for multiple operating systems
- Extensive community support and resources
With its wide range of capabilities, the Raspberry Pi is well-suited for managing IoT devices and ensuring secure connectivity.
Raspberry Pi Specifications
Here are some of the key specifications of the Raspberry Pi 4 Model B:
- Processor: Broadcom BCM2711, Quad-core Cortex-A72 (ARM v8) 64-bit SoC @ 1.5GHz
- RAM: 2GB, 4GB, or 8GB LPDDR4-3200 SDRAM
- Connectivity: 2.4 GHz and 5.0 GHz IEEE 802.11b/g/n/ac wireless LAN, Bluetooth 5.0, BLE
- Ports: 2 USB 3.0 ports, 2 USB 2.0 ports, Gigabit Ethernet
These specifications make the Raspberry Pi a powerful tool for managing IoT devices and maintaining secure connections.
Why Secure IoT Devices?
Securing IoT devices is essential for protecting sensitive data and preventing unauthorized access. With the increasing number of connected devices, the risk of cyberattacks also rises. A single compromised device can jeopardize the entire network, making security a top priority.
Key reasons for securing IoT devices include:
- Protection of personal and financial data
- Prevention of unauthorized access and control
- Ensuring compliance with regulations and standards
- Maintaining operational integrity and reliability
By implementing robust security measures, such as using a VPC and Raspberry Pi, you can safeguard your IoT devices and maintain peace of mind.
Risks of Insecure IoT Devices
Insecure IoT devices pose several risks, including:
- Data breaches leading to loss of sensitive information
- Malware infections compromising device functionality
- Unauthorized access enabling malicious activities
- Compliance violations resulting in legal and financial consequences
Avoiding these risks requires a proactive approach to IoT security, starting with secure connectivity solutions like VPC and Raspberry Pi.
Setting Up a VPC
Setting up a VPC involves several steps to ensure proper configuration and security. Below is a step-by-step guide to help you create a secure VPC for your IoT devices:
- Create a VPC: Use a cloud provider's management console to create a new VPC, specifying the desired IP address range and other settings.
- Define subnets: Divide your VPC into private and public subnets to isolate resources and enhance security.
- Set up security groups: Configure security groups to control inbound and outbound traffic for your VPC resources.
- Configure network ACLs: Use network ACLs to add an additional layer of security by defining rules for traffic entering and leaving your subnets.
Following these steps will help you create a secure VPC environment for your IoT devices.
VPC Security Best Practices
To further enhance the security of your VPC, consider the following best practices:
- Regularly update security group rules to reflect changes in your network
- Monitor network traffic for suspicious activity using tools like AWS CloudWatch
- Implement multi-factor authentication (MFA) for added protection
- Limit access to sensitive resources using role-based access control (RBAC)
By adhering to these best practices, you can maintain a secure VPC environment for your IoT devices.
Raspberry Pi Configuration
Configuring a Raspberry Pi for secure IoT connectivity involves several steps, including setting up the operating system, enabling SSH, and configuring network settings. Below is a step-by-step guide to help you get started:
- Install an operating system: Download and install a suitable operating system, such as Raspberry Pi OS, onto your Raspberry Pi.
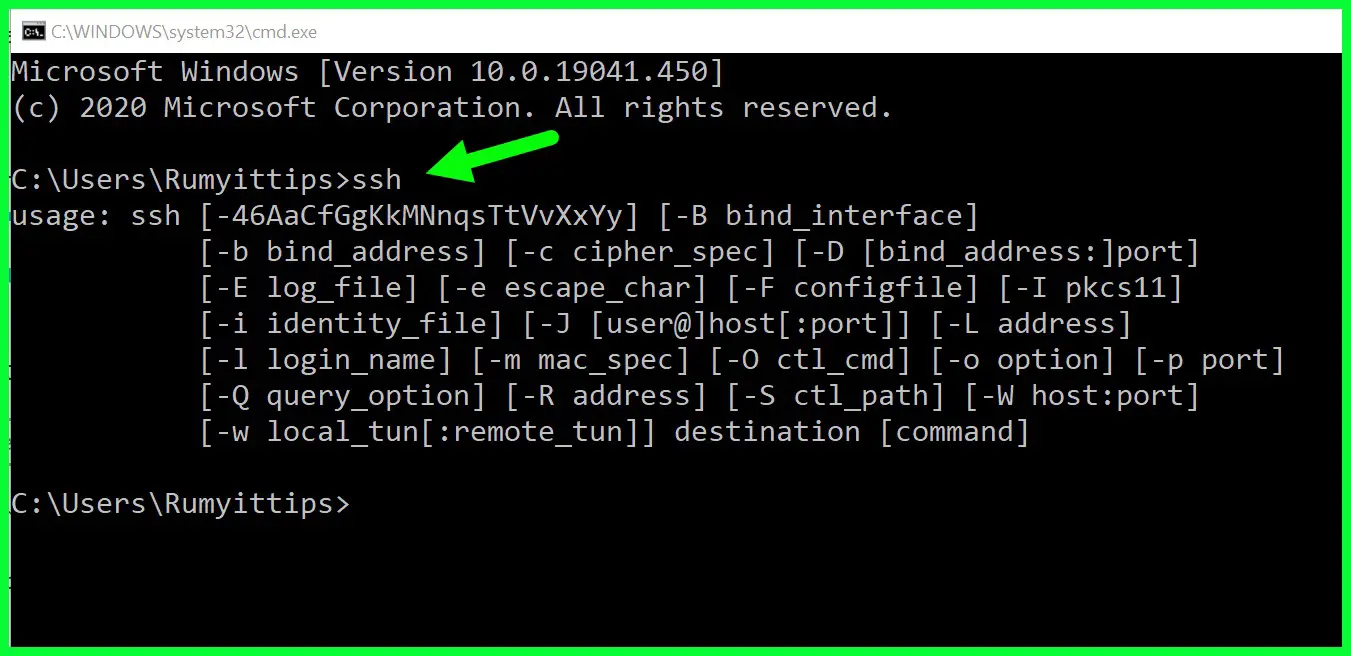
- Enable SSH: Enable Secure Shell (SSH) to allow remote access to your Raspberry Pi.
- Configure network settings: Set up your Raspberry Pi's network settings to connect to your VPC.
- Secure your Raspberry Pi: Implement security measures such as strong passwords, firewalls, and regular updates.
Completing these steps will ensure that your Raspberry Pi is properly configured for secure IoT connectivity.
Securing Your Raspberry Pi
To enhance the security of your Raspberry Pi, consider the following measures:
- Use strong, unique passwords for all accounts
- Enable automatic updates to keep your system up-to-date
- Install and configure a firewall to control incoming and outgoing traffic
- Regularly back up important data to prevent loss in case of a security breach
These security measures will help protect your Raspberry Pi and ensure secure IoT connectivity.
Connecting Remote IoT Devices
Connecting remote IoT devices to a VPC involves several steps to ensure proper configuration and secure communication. Below is a step-by-step guide to help you connect your IoT devices:
- Identify device requirements: Determine the specific requirements for each IoT device, such as communication protocols and authentication methods.
- Configure device settings: Set up each device to communicate with your VPC, ensuring proper authentication and encryption.
- Test connectivity: Verify that each device can successfully connect to your VPC and communicate securely.
- Monitor device performance: Use monitoring tools to track device performance and address any issues that arise.
Following these steps will help you establish secure connections between your IoT devices and VPC.
Best Practices for IoT Device Connectivity
To optimize IoT device connectivity, consider the following best practices:
- Use secure communication protocols such as HTTPS or MQTT with TLS
- Implement strong authentication mechanisms, such as certificates or tokens
- Regularly update device firmware to address security vulnerabilities
- Limit device access to only necessary resources within the VPC
By adhering to these best practices, you can ensure reliable and secure connectivity for your IoT devices.
Securing Your VPC
Securing your VPC requires a combination of technical measures and best practices to protect against potential threats. Below are some strategies to enhance the security of your VPC:
- Regularly review and update security group rules
- Implement network ACLs to control traffic at the subnet level
- Use encryption for data in transit and at rest
- Monitor VPC activity for suspicious behavior using tools like AWS CloudTrail
Implementing these strategies will help you maintain a secure VPC environment for your IoT devices.
Advanced Security Measures
For added security, consider implementing the following advanced measures:
- Use intrusion detection and prevention systems (IDPS) to detect and block malicious activity
- Implement data loss prevention (DLP) solutions to safeguard sensitive information
- Regularly perform security audits and vulnerability assessments
- Train employees and users on security best practices to reduce human error
These advanced measures will further enhance the security of your VPC and IoT devices.
Troubleshooting Common Issues
When working with VPCs and IoT devices, you may encounter various issues that require troubleshooting. Below are some common issues and their solutions:
- Device connectivity issues: Verify network settings and ensure proper authentication.
- Security group configuration problems: Review and update security group rules as needed.
- Performance bottlenecks: Monitor resource usage and optimize settings for better performance.
- Data transfer delays: Check network latency and optimize communication protocols.
Addressing these issues promptly will help ensure smooth operation of your IoT devices and VPC.
Best Practices for IoT Security
Implementing best practices for IoT security is essential for protecting your devices and maintaining operational integrity. Below are some key best practices:
- Use strong, unique passwords for all devices and accounts
- Regularly update firmware and software to address security vulnerabilities
- Implement encryption for data in transit and at rest
- Limit device access to only necessary resources within the VPC
By following these best practices, you can enhance