Connecting IoT devices securely in a remote environment has become a critical need in today's technology-driven world. As businesses and individuals rely more on cloud computing and IoT, ensuring secure communication between devices and networks is paramount. AWS offers robust solutions, such as VPC and Raspberry Pi integrations, to help users create a secure IoT infrastructure while keeping costs low with free-tier options.
With the rise of remote work and distributed systems, setting up a secure connection between IoT devices and the cloud has never been more important. AWS provides tools like Virtual Private Cloud (VPC) to isolate and protect IoT devices, ensuring data remains private and secure. This article will explore how to securely connect remote IoT devices using Raspberry Pi and AWS, including free resources available for download.
This guide aims to provide actionable insights, technical details, and practical steps to help you establish a secure IoT environment. Whether you're a developer, hobbyist, or business owner, this article will equip you with the knowledge to leverage AWS and Raspberry Pi for secure IoT connections.
Read also:Who Did Emily Compagno Marry A Comprehensive Look Into Her Personal Life And Career
Table of Contents
- Introduction to IoT and Secure Connections
- Overview of Raspberry Pi in IoT
- What is AWS VPC?
- Benefits of Securely Connecting IoT Devices
- Step-by-Step Guide to Secure IoT Connections
- Free Downloads and Resources for AWS IoT
- Best Practices for Secure IoT Connections
- Troubleshooting Common Issues
- Future Trends in Secure IoT Connections
- Conclusion
Introduction to IoT and Secure Connections
Internet of Things (IoT) refers to the interconnected network of devices that communicate with each other over the internet. From smart home appliances to industrial sensors, IoT devices are revolutionizing the way we interact with technology. However, with the increasing number of connected devices, security concerns have grown exponentially.
Securing IoT devices is crucial to prevent unauthorized access and data breaches. AWS provides a range of tools, including Virtual Private Cloud (VPC), to help users establish secure connections. By leveraging AWS VPC, users can isolate their IoT devices from the public internet, ensuring data privacy and security.
Why Security Matters in IoT
IoT devices often collect sensitive data, such as personal information or industrial secrets. If not secured properly, this data can be vulnerable to cyberattacks. Implementing robust security measures, such as encryption and secure authentication, is essential to protect IoT devices and the data they transmit.
Overview of Raspberry Pi in IoT
Raspberry Pi is a popular single-board computer widely used in IoT projects. Its affordability, versatility, and ease of use make it an ideal choice for developers and hobbyists alike. Raspberry Pi can act as a gateway for IoT devices, enabling secure communication with cloud platforms like AWS.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for various operating systems, including Raspbian and Ubuntu
- Compatibility with numerous sensors and peripherals
- Easy integration with cloud platforms like AWS
What is AWS VPC?
AWS Virtual Private Cloud (VPC) is a service that allows users to create an isolated network environment in the AWS cloud. With VPC, users can define their own IP address range, create subnets, and configure route tables and network gateways. This ensures that IoT devices connected to the VPC are protected from unauthorized access.
How AWS VPC Enhances Security
By using AWS VPC, users can:
Read also:Is Ron Jeremy Still In Prison Unveiling The Truth Behind The Controversial Porn Icon
- Isolate IoT devices from the public internet
- Control inbound and outbound traffic using security groups and network access control lists (ACLs)
- Encrypt data in transit and at rest
- Monitor network activity for potential security threats
Benefits of Securely Connecting IoT Devices
Establishing secure connections for IoT devices offers several advantages, including:
- Enhanced data privacy and security
- Reduced risk of cyberattacks and data breaches
- Improved device performance and reliability
- Compliance with industry regulations and standards
Real-World Applications of Secure IoT Connections
Secure IoT connections are essential in various industries, such as healthcare, manufacturing, and transportation. For example, in healthcare, secure IoT devices can transmit patient data to cloud platforms for analysis and monitoring. In manufacturing, IoT sensors can provide real-time insights into production processes, enabling businesses to optimize operations.
Step-by-Step Guide to Secure IoT Connections
Setting up a secure IoT connection using Raspberry Pi and AWS involves several steps. Below is a detailed guide to help you get started:
Step 1: Set Up Your Raspberry Pi
Begin by installing an operating system on your Raspberry Pi. Raspbian is a popular choice, but you can also use Ubuntu or other Linux-based distributions. Once the operating system is installed, configure the network settings and enable SSH for remote access.
Step 2: Create an AWS Account
Sign up for an AWS account and activate the free tier, which provides access to several AWS services, including VPC and IoT Core, for one year. This will help you save costs while experimenting with IoT projects.
Step 3: Configure AWS VPC
Log in to the AWS Management Console and navigate to the VPC dashboard. Create a new VPC and define the IP address range, subnets, and route tables. Configure security groups and network ACLs to control traffic flow.
Step 4: Connect Raspberry Pi to AWS
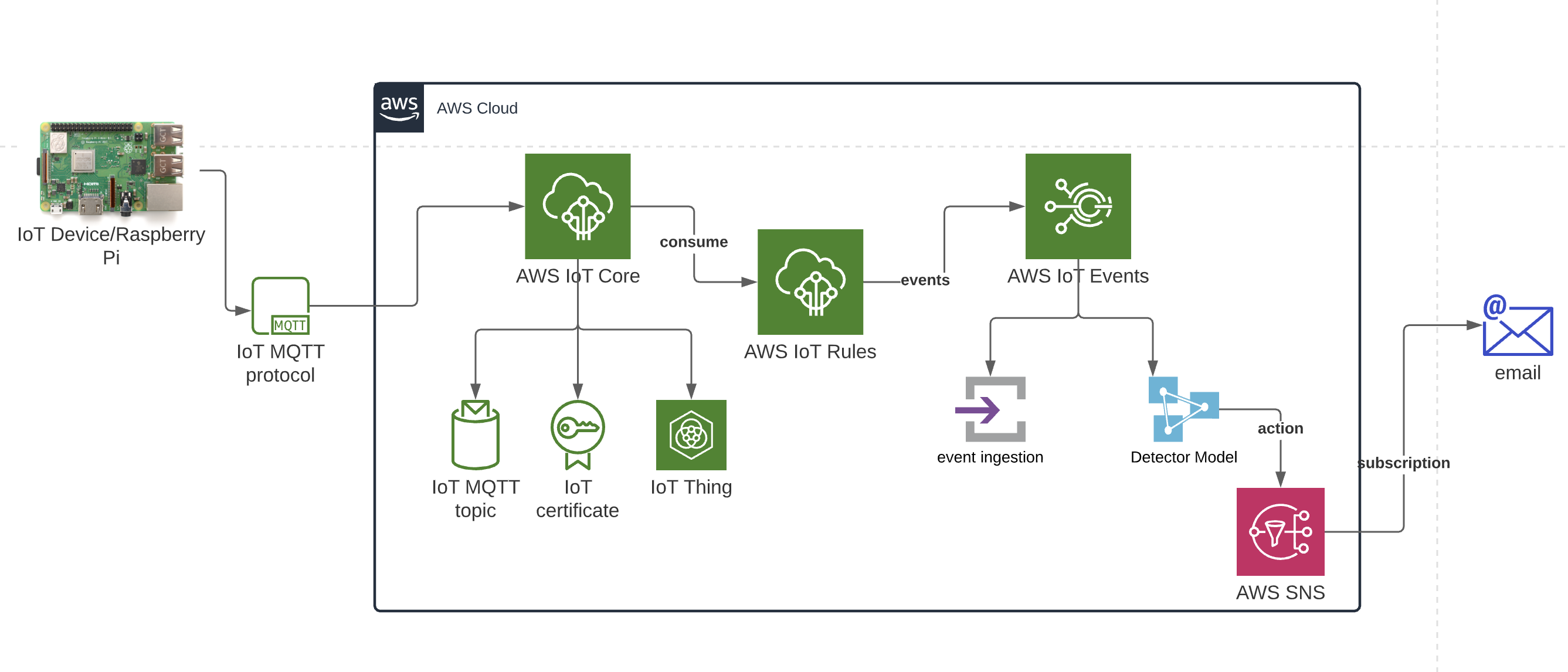
Install the AWS IoT Core SDK on your Raspberry Pi and configure it to connect to your VPC. Use secure protocols like MQTT or HTTPS to transmit data between your IoT devices and the cloud.
Free Downloads and Resources for AWS IoT
AWS offers several free resources to help users get started with IoT projects. These include:
- AWS IoT Core free tier
- Free AWS VPC setup guides
- Sample code and tutorials for Raspberry Pi
- Documentation and support forums
Where to Find Free Downloads
You can access these resources by visiting the AWS website and navigating to the IoT section. Additionally, the AWS Marketplace offers free and paid software solutions for IoT projects.
Best Practices for Secure IoT Connections
To ensure the security of your IoT devices, follow these best practices:
- Use strong passwords and two-factor authentication
- Regularly update firmware and software
- Encrypt data in transit and at rest
- Monitor network activity for suspicious behavior
Common Security Threats in IoT
IoT devices are vulnerable to various security threats, including:
- Malware and ransomware attacks
- Denial-of-service (DoS) attacks
- Man-in-the-middle (MitM) attacks
- Data breaches
Troubleshooting Common Issues
When setting up secure IoT connections, you may encounter various issues. Below are some common problems and their solutions:
Issue 1: Unable to Connect to AWS VPC
Solution: Check your network configuration and ensure that security groups and network ACLs are properly set up. Verify that your Raspberry Pi is connected to the correct subnet and that the route tables are configured correctly.
Issue 2: Data Transmission Errors
Solution: Ensure that the AWS IoT Core SDK is correctly installed and configured on your Raspberry Pi. Check the protocol settings and verify that the data format is compatible with the cloud platform.
Future Trends in Secure IoT Connections
The future of IoT security is evolving rapidly, with new technologies and standards emerging to address emerging threats. Some key trends include:
- Blockchain-based security solutions
- Artificial intelligence and machine learning for threat detection
- Edge computing for enhanced performance and security
- Quantum cryptography for unbreakable encryption
How These Trends Will Impact IoT Security
As IoT continues to grow, implementing advanced security measures will become increasingly important. By adopting emerging technologies and staying informed about the latest trends, users can ensure the safety and reliability of their IoT devices.
Conclusion
Securing IoT devices is essential to protect sensitive data and prevent cyberattacks. By leveraging AWS VPC and Raspberry Pi, users can establish secure connections for their IoT projects while keeping costs low with free-tier options. This guide has provided actionable insights, technical details, and practical steps to help you achieve secure IoT connections.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more information on IoT, cloud computing, and cybersecurity. Together, we can build a safer and more connected future.