RemoteIoT platform SSH key management for Raspberry Pi has become a critical skill for developers and enthusiasts alike. Whether you're setting up a home automation system, working on IoT projects, or managing remote servers, understanding SSH keys is essential. This guide will walk you through everything you need to know about configuring SSH keys for Raspberry Pi using the RemoteIoT platform, ensuring secure and seamless access.
As technology evolves, the demand for secure and efficient remote access solutions increases. For Raspberry Pi users, SSH (Secure Shell) is the go-to protocol for managing devices remotely. However, managing SSH keys effectively can be challenging for beginners. This article aims to simplify the process by providing step-by-step instructions and expert tips.
This guide is tailored for both beginners and advanced users who want to harness the full potential of their Raspberry Pi devices while ensuring robust security. By the end of this article, you'll have a comprehensive understanding of how to set up and manage SSH keys using the RemoteIoT platform.
Read also:Emily Compagno Divorce The Full Story Behind The Headlines
Table of Contents
- Introduction to RemoteIoT Platform
- What is SSH and Why Use It?
- Benefits of Using SSH Keys for Raspberry Pi
- Setting Up RemoteIoT Platform
- How to Generate SSH Keys
- Configuring Raspberry Pi for SSH Access
- Connecting Raspberry Pi to RemoteIoT Platform
- Security Best Practices for SSH
- Common Issues and Troubleshooting Tips
- Conclusion and Next Steps
Introduction to RemoteIoT Platform
The RemoteIoT platform is a powerful tool designed to simplify remote management of IoT devices, including Raspberry Pi. It provides an intuitive interface and robust features that make managing SSH keys and device connections effortless. Whether you're a hobbyist or a professional developer, RemoteIoT offers the flexibility and security you need to manage your projects effectively.
This platform supports various operating systems and devices, making it a versatile solution for IoT enthusiasts. By integrating SSH key management into its core functionality, RemoteIoT ensures secure and encrypted communication between devices and users.
In this section, we will explore the key features of RemoteIoT and how it enhances the SSH experience for Raspberry Pi users. Additionally, we will discuss why choosing a reliable platform like RemoteIoT is crucial for maintaining secure connections.
What is SSH and Why Use It?
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote access to servers, file transfers, and command execution. For Raspberry Pi users, SSH is indispensable for managing devices remotely without physical access.
Key Features of SSH
- Encryption: SSH ensures that all data transmitted between devices is encrypted, preventing unauthorized access.
- Authentication: SSH provides robust authentication mechanisms, including password-based and key-based authentication.
- Security: By using SSH, users can protect their devices from common cyber threats such as man-in-the-middle attacks.
Using SSH with Raspberry Pi not only enhances security but also improves efficiency by allowing users to automate tasks and manage multiple devices simultaneously.
Benefits of Using SSH Keys for Raspberry Pi
While password-based authentication is common, using SSH keys offers several advantages that make it the preferred choice for securing Raspberry Pi devices. Below are some of the key benefits:
Read also:The Real Blippi Exploring The World Of Education Through Fun And Entertainment
- Increased Security: SSH keys provide stronger authentication compared to passwords, reducing the risk of brute-force attacks.
- Convenience: Once set up, SSH keys eliminate the need to enter passwords repeatedly, streamlining the login process.
- Automation: SSH keys enable seamless automation of tasks, such as deploying scripts or transferring files between devices.
By leveraging SSH keys, Raspberry Pi users can significantly enhance the security and usability of their devices. In the next section, we will delve into setting up the RemoteIoT platform to manage these keys effectively.
Setting Up RemoteIoT Platform
Before configuring SSH keys for Raspberry Pi, it's essential to set up the RemoteIoT platform. Follow these steps to get started:
- Visit the official RemoteIoT website and create an account if you haven't already.
- Download and install the RemoteIoT client software on your computer or mobile device.
- Log in to your account and navigate to the device management section.
Once the platform is set up, you can begin configuring SSH keys for your Raspberry Pi devices. The RemoteIoT platform provides an intuitive interface that simplifies the process, ensuring a smooth setup experience.
How to Generate SSH Keys
Generating SSH keys is a straightforward process that involves using the OpenSSH utility. Follow these steps to generate a key pair:
- Open a terminal or command prompt on your computer.
- Run the command:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com". - Follow the prompts to specify a file location and passphrase (optional).
After generating the keys, you will have a private key (id_rsa) and a public key (id_rsa.pub). The public key will be uploaded to your Raspberry Pi, while the private key remains securely stored on your computer.
Best Practices for Key Management
- Always use strong passphrases to protect your private key.
- Store your private key in a secure location and avoid sharing it with others.
- Regularly update and rotate your SSH keys to maintain security.
Configuring Raspberry Pi for SSH Access
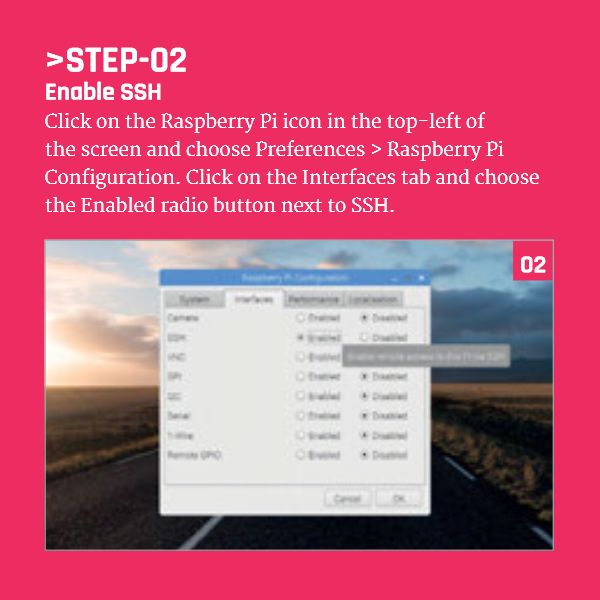
Once you have generated your SSH keys, the next step is to configure your Raspberry Pi for SSH access. Follow these instructions to enable SSH and upload your public key:
- Connect to your Raspberry Pi via a monitor or SSH client.
- Enable SSH by running the command:
sudo raspi-configand navigating to the SSH option. - Create a .ssh directory in your home folder:
mkdir ~/.ssh. - Copy your public key to the authorized_keys file:
echo "your_public_key">> ~/.ssh/authorized_keys.
With SSH configured, you can now connect to your Raspberry Pi securely using the RemoteIoT platform. This setup ensures encrypted communication and eliminates the need for password-based authentication.
Connecting Raspberry Pi to RemoteIoT Platform
Connecting your Raspberry Pi to the RemoteIoT platform is the final step in setting up secure SSH access. Follow these instructions to complete the process:
- Log in to your RemoteIoT account and navigate to the device management section.
- Add your Raspberry Pi by providing its IP address or hostname.
- Upload your public SSH key to the platform for authentication.
Once connected, you can manage your Raspberry Pi remotely through the RemoteIoT interface. This platform provides real-time monitoring, automated backups, and secure access from anywhere in the world.
Security Best Practices for SSH
While SSH keys significantly enhance security, it's important to follow best practices to ensure your devices remain protected. Below are some key recommendations:
- Disable password-based authentication to prevent brute-force attacks.
- Limit SSH access to specific IP addresses or networks using firewall rules.
- Regularly update your Raspberry Pi's operating system and software to patch vulnerabilities.
- Monitor SSH logs for suspicious activity and take immediate action if necessary.
By adhering to these practices, you can maintain a secure and reliable SSH setup for your Raspberry Pi devices.
Common Issues and Troubleshooting Tips
Even with careful setup, issues can arise when configuring SSH keys for Raspberry Pi. Below are some common problems and solutions:
- Connection Refused: Ensure SSH is enabled on your Raspberry Pi and check the IP address or hostname for accuracy.
- Permission Denied: Verify that your public key is correctly added to the authorized_keys file and that file permissions are set appropriately.
- Key Authentication Failed: Double-check that your private key is stored securely and matches the public key uploaded to the platform.
If you encounter persistent issues, consult the official RemoteIoT documentation or seek assistance from their support team.
Conclusion and Next Steps
In conclusion, mastering SSH key management for Raspberry Pi using the RemoteIoT platform is a valuable skill for anyone working with IoT devices. This guide has provided a comprehensive overview of the process, from generating SSH keys to configuring secure connections. By following the steps outlined, you can ensure your devices remain secure and accessible from anywhere in the world.
We encourage you to take the next step by experimenting with advanced features of the RemoteIoT platform and exploring additional security measures. Share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our website for more valuable insights.
Stay secure and keep innovating!