In the era of advanced technology, the integration of IoT (Internet of Things) with remote platforms has become increasingly significant. One of the most reliable ways to secure remote access to IoT devices is by using SSH (Secure Shell) with key-based authentication on a Raspberry Pi. This article will provide a comprehensive guide to setting up and utilizing SSH keys for secure IoT communication on Raspberry Pi.
As the Internet of Things continues to expand, managing and securing devices remotely is more critical than ever. With the help of Raspberry Pi, a versatile and cost-effective platform, you can establish secure communication channels using SSH key pairs.
This guide aims to simplify the complexities involved in setting up SSH keys for Raspberry Pi, ensuring that your IoT devices remain secure and accessible from anywhere in the world.
Read also:When Did Emily Compagno Get Married A Comprehensive Guide To Her Personal Life And Career
Table of Contents
- Introduction to Remote IoT Platform SSH Key on Raspberry Pi
- Understanding Raspberry Pi and Its Role in IoT
- Overview of SSH and Its Importance in IoT
- Generating SSH Keys for Raspberry Pi
- Securing IoT Devices with SSH Keys
- Advantages of Using SSH Keys on Raspberry Pi
- Troubleshooting Common Issues with SSH Keys
- Best Practices for Managing SSH Keys
- Exploring Alternatives to SSH Keys
- Conclusion and Call to Action
Introduction to Remote IoT Platform SSH Key on Raspberry Pi
Remote IoT platforms have transformed the way we interact with devices. The use of SSH keys on Raspberry Pi enhances security and simplifies remote management. This section will introduce the concept and importance of SSH keys in IoT environments.
SSH keys provide a secure method for authentication without the need for passwords. By leveraging SSH keys, users can protect their IoT devices from unauthorized access while maintaining ease of access for legitimate users.
Understanding how SSH keys function and how they integrate with Raspberry Pi is essential for anyone looking to enhance their IoT setup's security.
Understanding Raspberry Pi and Its Role in IoT
Raspberry Pi: A Versatile IoT Platform
Raspberry Pi has emerged as one of the most popular platforms for IoT projects. Its affordability, flexibility, and powerful capabilities make it an ideal choice for developers and hobbyists alike.
- Compact size
- Low power consumption
- Support for multiple operating systems
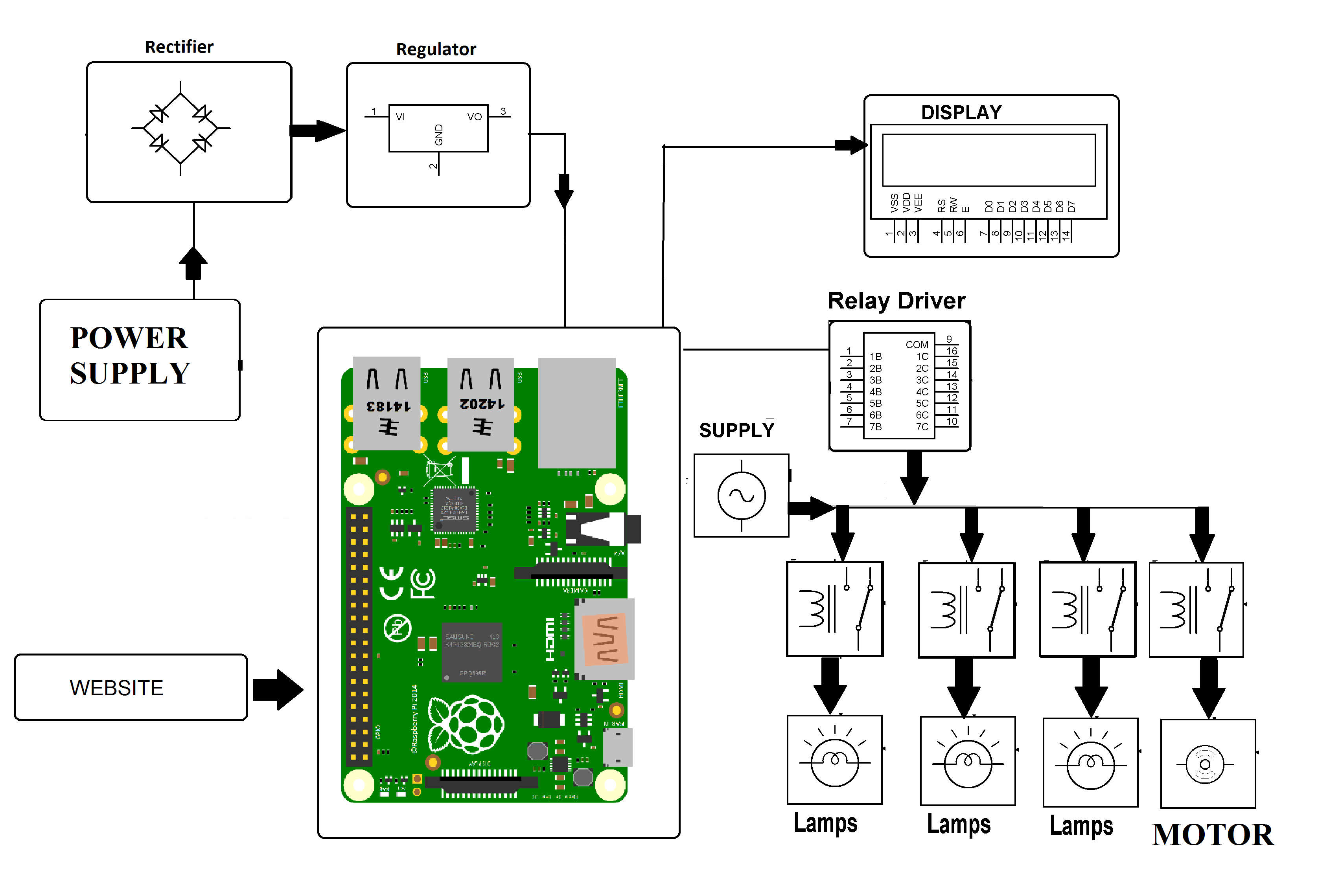
With its GPIO pins and robust processing power, Raspberry Pi serves as a central hub for connecting various IoT devices.
Why Raspberry Pi for IoT?
Raspberry Pi offers several advantages that make it perfect for IoT applications:
Read also:Is John Travolta Gay Unveiling The Truth Behind The Rumors
- Cost-effective hardware
- Extensive community support
- Compatibility with multiple programming languages
These features make Raspberry Pi an excellent choice for building secure and scalable IoT systems.
Overview of SSH and Its Importance in IoT
SSH, or Secure Shell, is a protocol used for secure communication between devices over an unsecured network. In the context of IoT, SSH provides a secure channel for managing devices remotely.
Key-based authentication, a feature of SSH, eliminates the need for passwords, reducing the risk of brute-force attacks and unauthorized access.
By implementing SSH with key-based authentication, IoT devices can be managed securely, ensuring data integrity and confidentiality.
Generating SSH Keys for Raspberry Pi
Step-by-Step Guide to Creating SSH Keys
Generating SSH keys for Raspberry Pi involves a straightforward process. Follow these steps to create your SSH key pair:
- Open a terminal window on your computer.
- Run the command:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com". - Choose a location to save the key (default is usually fine).
- Set a passphrase for added security.
This process will generate a public and private key pair, which will be used for authentication.
Transferring SSH Keys to Raspberry Pi
Once the keys are generated, they need to be transferred to the Raspberry Pi. Use the following steps:
- Copy the public key to Raspberry Pi using the command:
ssh-copy-id pi@raspberrypi.local. - Enter the Raspberry Pi's password when prompted.
- Test the connection by running:
ssh pi@raspberrypi.local.
With the keys successfully transferred, you can now log in to your Raspberry Pi without needing a password.
Securing IoT Devices with SSH Keys
Why Security Matters in IoT
IoT devices are often vulnerable to cyberattacks due to their connectivity and lack of robust security measures. Using SSH keys helps mitigate these risks by providing a secure authentication method.
By eliminating the use of passwords, SSH keys reduce the likelihood of brute-force attacks and unauthorized access to your IoT devices.
Best Security Practices for IoT Devices
- Regularly update firmware and software.
- Use strong, unique SSH keys for each device.
- Monitor network activity for suspicious behavior.
Implementing these practices ensures that your IoT devices remain secure and reliable.
Advantages of Using SSH Keys on Raspberry Pi
Using SSH keys on Raspberry Pi offers numerous benefits that enhance both security and convenience:
- Increased security through key-based authentication.
- Elimination of password-related vulnerabilities.
- Seamless remote access without the need for manual password entry.
These advantages make SSH keys an essential tool for anyone managing IoT devices on Raspberry Pi.
Troubleshooting Common Issues with SSH Keys
Common Problems and Solutions
While SSH keys are generally reliable, issues can arise. Below are some common problems and their solutions:
- Key not recognized: Ensure the public key is correctly copied to the Raspberry Pi.
- Connection refused: Check firewall settings and ensure SSH is enabled on the Raspberry Pi.
- Passphrase forgotten: Regenerate the SSH key pair with a new passphrase.
Addressing these issues promptly ensures uninterrupted access to your IoT devices.
Best Practices for Managing SSH Keys
Managing SSH Keys Effectively
To maximize the benefits of SSH keys, follow these best practices:
- Store private keys in a secure location.
- Regularly audit and rotate SSH keys.
- Limit access to SSH keys to authorized personnel only.
By adhering to these practices, you can maintain the security and integrity of your IoT setup.
Exploring Alternatives to SSH Keys
While SSH keys are a popular choice for securing IoT devices, other methods exist. Below are some alternatives:
- SSL/TLS certificates: Provide robust encryption for secure communication.
- Two-factor authentication: Adds an extra layer of security to device access.
- VPN tunnels: Create a secure network for managing IoT devices.
Each method has its advantages and disadvantages, so it's essential to choose the one that best fits your needs.
Conclusion and Call to Action
In conclusion, using SSH keys on Raspberry Pi is a powerful way to secure your IoT devices and simplify remote management. By following the steps outlined in this guide, you can enhance the security of your IoT setup and protect it from potential threats.
We encourage you to share your experiences and insights in the comments below. Additionally, explore our other articles for more tips and tricks on managing IoT devices effectively.
Thank you for reading, and happy tinkering!