In the era of Internet of Things (IoT), remote access to devices has become an essential skill for developers and hobbyists alike. The Raspberry Pi, with its affordability and versatility, plays a crucial role in enabling seamless SSH remote IoT device management. Whether you're managing a home automation system or deploying industrial IoT solutions, understanding how to set up SSH on a Raspberry Pi is invaluable.
SSH, or Secure Shell, is a cryptographic protocol designed to provide secure communication over unsecured networks. With SSH, users can remotely control and manage IoT devices from anywhere in the world, ensuring both convenience and security. This article will guide you through the process of setting up SSH remote access on a Raspberry Pi, providing step-by-step instructions and valuable insights.
By the end of this guide, you'll have the knowledge and tools necessary to download and configure SSH for your IoT projects. Whether you're a beginner or an experienced developer, this comprehensive guide will help you master the art of remote IoT device management using Raspberry Pi.
Read also:Who Is Adam Schiffs Wife Exploring The Life And Legacy Of Eve Schiff
Table of Contents
- Introduction to SSH
- Raspberry Pi Overview
- Why SSH for IoT Devices?
- Setup SSH on Raspberry Pi
- Remote Access to IoT Devices
- Security Best Practices
- Troubleshooting SSH Issues
- Free SSH Tools and Software
- Case Studies: Real-World Applications
- Conclusion and Next Steps
Introduction to SSH
SSH, or Secure Shell, is a network protocol that provides secure communication between two devices over an unsecured network. It is widely used for remote command-line login and file transfer, ensuring data integrity and confidentiality. By encrypting all data exchanged between the client and server, SSH eliminates the risks associated with unencrypted protocols like Telnet.
For IoT devices, SSH offers a reliable method of remote management, allowing users to access and control their devices from anywhere in the world. This is particularly important for devices deployed in remote locations or those requiring frequent updates and maintenance.
Key Features of SSH
- Encryption: Ensures secure data transmission.
- Authentication: Verifies the identity of both client and server.
- Command Execution: Allows users to execute commands remotely.
- File Transfer: Facilitates secure file transfer using SFTP.
Raspberry Pi Overview
The Raspberry Pi is a small, affordable single-board computer that has gained immense popularity among hobbyists, educators, and professionals. With its powerful hardware and versatile operating systems, the Raspberry Pi is an ideal platform for IoT projects. It supports a wide range of applications, from home automation to industrial automation, making it a go-to choice for developers.
One of the key advantages of the Raspberry Pi is its compatibility with Linux-based operating systems, which makes it easy to install and configure SSH. This compatibility ensures that users can leverage the full power of SSH for remote access and management of IoT devices.
Why Raspberry Pi for IoT?
- Affordability: Low cost with high performance.
- Community Support: Large community of developers and resources.
- Versatility: Supports a wide range of applications and projects.
- Open Source: Fully customizable and modifiable.
Why SSH for IoT Devices?
IoT devices are often deployed in remote locations, making physical access impractical or impossible. SSH provides a secure and efficient solution for remote management, enabling users to monitor, update, and troubleshoot their devices without needing to be physically present.
With SSH, users can:
Read also:Is Blake Shelton A Democrat Or A Republican In 2024
- Access device configurations and settings.
- Execute commands and scripts remotely.
- Transfer files securely using SFTP.
- Monitor device performance and logs.
Security Benefits of SSH
SSH offers several security advantages over other remote access protocols:
- Data Encryption: Protects sensitive information from eavesdropping.
- Authentication: Ensures only authorized users can access the device.
- Integrity: Prevents data tampering during transmission.
Setup SSH on Raspberry Pi
Setting up SSH on a Raspberry Pi is a straightforward process that can be completed in just a few steps. This section will guide you through the process, ensuring that your IoT device is ready for secure remote access.
Step 1: Enable SSH
To enable SSH on your Raspberry Pi, follow these steps:
- Connect your Raspberry Pi to a monitor, keyboard, and mouse.
- Boot the Raspberry Pi and log in to the operating system.
- Open the Raspberry Pi Configuration tool by typing "sudo raspi-config" in the terminal.
- Select "Interfacing Options" and enable SSH.
Step 2: Find Your Pi's IP Address
To connect to your Raspberry Pi remotely, you need to know its IP address. You can find this information by typing "hostname -I" in the terminal. This command will display the IP address assigned to your Raspberry Pi.
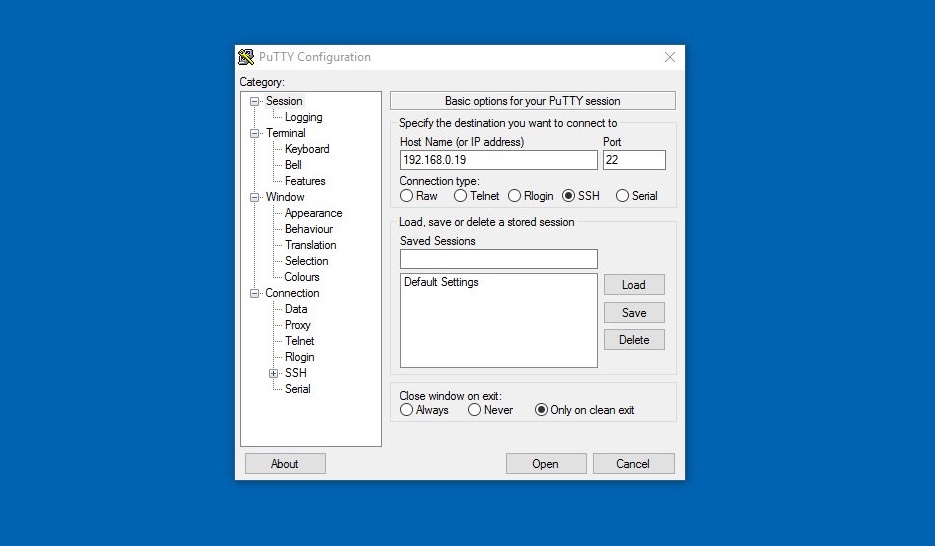
Step 3: Connect Using an SSH Client
Once SSH is enabled and you have the IP address, you can connect to your Raspberry Pi using an SSH client. Popular SSH clients include PuTTY (for Windows) and Terminal (for macOS and Linux).
Remote Access to IoT Devices
With SSH configured on your Raspberry Pi, you can now access your IoT devices from anywhere in the world. This section will explore the various ways you can leverage SSH for remote IoT device management.
Remote Command Execution
Using SSH, you can execute commands on your IoT device remotely. This is particularly useful for automating tasks, monitoring device performance, and troubleshooting issues. For example, you can use SSH to check CPU usage, disk space, and network connectivity.
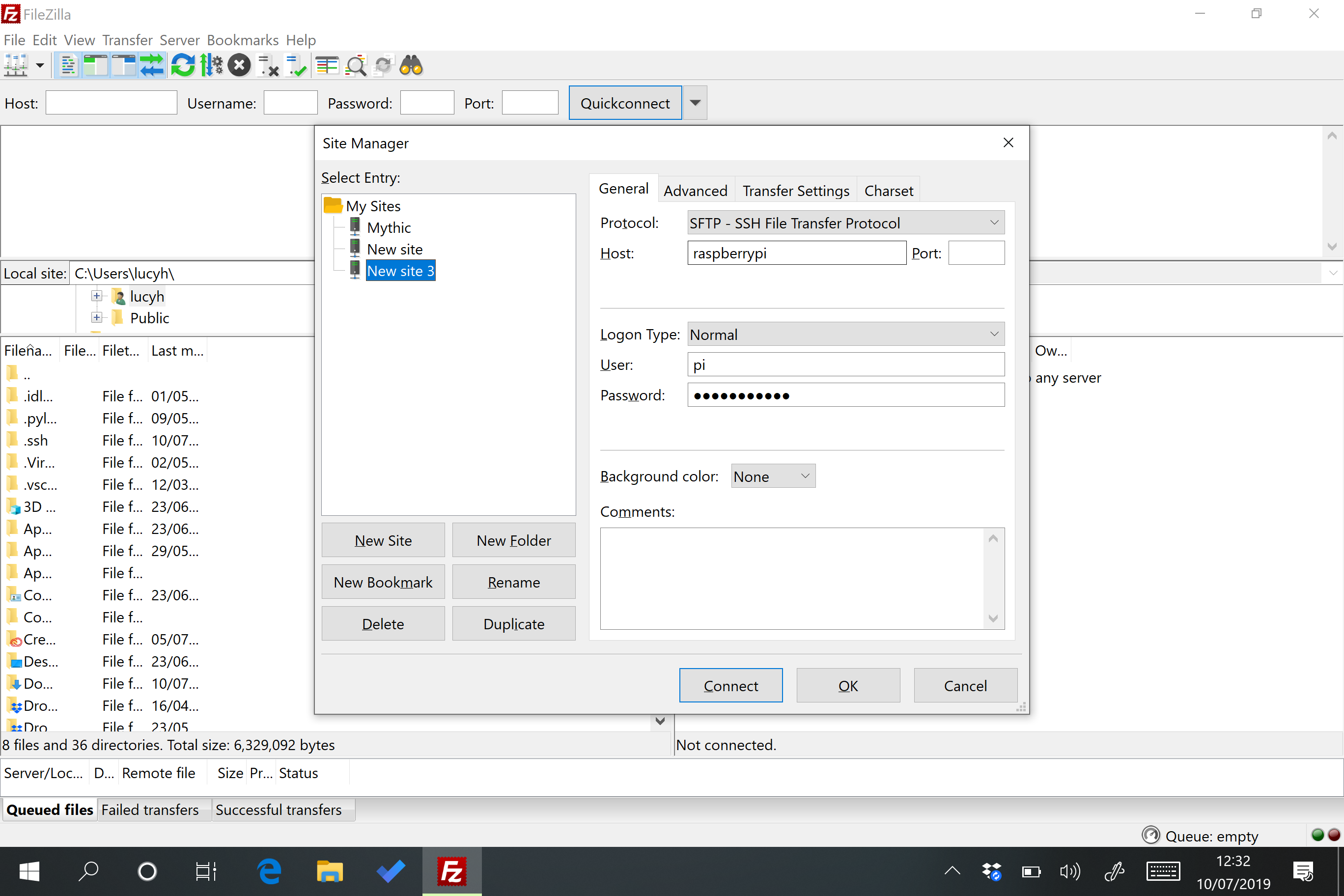
File Transfer with SFTP
SFTP (Secure File Transfer Protocol) is an extension of SSH that allows you to transfer files securely between your local machine and your Raspberry Pi. This is ideal for uploading scripts, configuration files, and other resources to your IoT device.
Security Best Practices
While SSH provides a secure method of remote access, it is important to follow best practices to ensure the security of your IoT devices. This section will outline key security measures you can implement to protect your Raspberry Pi and its connected devices.
Use Strong Passwords
Strong passwords are essential for securing your SSH connection. Avoid using common passwords and consider using a password manager to generate and store complex passwords.
Enable Key-Based Authentication
Key-based authentication provides an additional layer of security by requiring a private key to access your device. This eliminates the need for passwords and reduces the risk of brute-force attacks.
Update Your System Regularly
Keeping your Raspberry Pi and its software up to date is crucial for maintaining security. Regular updates ensure that any vulnerabilities are patched and that your device is protected against potential threats.
Troubleshooting SSH Issues
Despite its reliability, SSH can sometimes encounter issues that prevent successful connections. This section will address common problems and provide solutions to help you troubleshoot and resolve them.
Connection Refused
If you receive a "connection refused" error, it may indicate that SSH is not enabled on your Raspberry Pi. Double-check that SSH is enabled in the Raspberry Pi Configuration tool and ensure that the IP address is correct.
Authentication Failed
Authentication failures can occur due to incorrect passwords or mismatched keys. Verify that you are using the correct credentials and ensure that your public key is correctly configured on the server.
Free SSH Tools and Software
There are several free SSH tools and software available that can enhance your remote access experience. This section will introduce you to some of the most popular options and explain how they can benefit your IoT projects.
PuTTY
PuTTY is a widely used SSH client for Windows users. It provides a simple interface for connecting to remote servers and supports various protocols, including SSH, Telnet, and Rlogin.
OpenSSH
OpenSSH is a free and open-source SSH client and server software that is included in most Linux distributions. It offers a robust set of features and is highly customizable, making it an ideal choice for Raspberry Pi users.
Case Studies: Real-World Applications
To demonstrate the practical applications of SSH in IoT projects, this section will present several case studies that showcase its versatility and effectiveness.
Home Automation System
A homeowner uses SSH to remotely manage their home automation system, controlling lighting, temperature, and security systems from their smartphone. This setup not only improves convenience but also enhances security by allowing real-time monitoring and updates.
Industrial IoT Deployment
An industrial facility uses SSH to monitor and control IoT sensors deployed across its production line. By enabling remote access, engineers can quickly identify and resolve issues, minimizing downtime and improving efficiency.
Conclusion and Next Steps
In conclusion, SSH provides a secure and efficient method for remote access to IoT devices, making it an essential tool for developers and hobbyists alike. By following the steps outlined in this guide, you can successfully configure SSH on your Raspberry Pi and take full advantage of its capabilities.
We encourage you to explore further by experimenting with different SSH tools and configurations. Don't forget to share your experiences and insights with the community, and consider contributing to open-source projects to help advance the field of IoT development.
Thank you for reading, and we hope this guide has been helpful in your journey to mastering SSH remote IoT device management using Raspberry Pi. If you have any questions or feedback, please leave a comment below or explore our other articles for more information.