In the digital era, finding the best SSH RemoteIoT solution has become a top priority for businesses and individuals alike. Secure Shell (SSH) is a powerful protocol designed to provide encrypted communication over unsecured networks, ensuring that data remains confidential and secure. RemoteIoT takes this concept a step further by integrating SSH protocols into Internet of Things (IoT) devices, creating a seamless and secure connection for remote access.
As more devices become interconnected, the demand for secure and reliable remote access solutions continues to grow. Whether you're a tech-savvy professional or someone just beginning to explore the world of IoT, understanding SSH RemoteIoT is crucial. This article will delve into the intricacies of SSH RemoteIoT, providing you with the knowledge needed to make informed decisions about your connectivity needs.
By the end of this guide, you will have a comprehensive understanding of SSH RemoteIoT, its benefits, challenges, and how to choose the best solution tailored to your requirements. Let's dive in and explore the fascinating world of secure remote connectivity.
Read also:Pixie Haircut On Square Face The Ultimate Guide To Flattering Styles
Table of Contents
- Introduction to SSH RemoteIoT
- The Importance of SSH in IoT
- How SSH RemoteIoT Works
- Benefits of Using SSH RemoteIoT
- Security Considerations for SSH RemoteIoT
- Criteria for Selecting the Best SSH RemoteIoT
- Top SSH RemoteIoT Solutions
- Implementing SSH RemoteIoT
- Troubleshooting Common Issues
- The Future of SSH RemoteIoT
- Conclusion
Introduction to SSH RemoteIoT
SSH RemoteIoT combines two powerful technologies: Secure Shell (SSH) and the Internet of Things (IoT). SSH is a cryptographic protocol that ensures secure communication between devices over an unsecured network. IoT, on the other hand, refers to the network of interconnected devices that communicate and exchange data. Together, they create a robust solution for secure remote access to IoT devices.
Why Choose SSH for IoT?
SSH provides several advantages for IoT applications. It encrypts data during transmission, ensuring confidentiality and integrity. Additionally, SSH supports authentication mechanisms that verify the identity of devices and users, reducing the risk of unauthorized access.
Applications of SSH RemoteIoT
SSH RemoteIoT finds applications in various industries, including:
- Smart homes
- Industrial automation
- Healthcare monitoring
- Remote surveillance
The Importance of SSH in IoT
IoT devices are often deployed in remote locations, making secure remote access essential. Without proper security measures, these devices become vulnerable to cyberattacks, data breaches, and unauthorized access. SSH plays a critical role in addressing these security concerns by providing a secure channel for communication.
Key Security Features of SSH
SSH offers several security features that make it an ideal choice for IoT applications:
- Data encryption
- Strong authentication
- Secure file transfer
- Command execution over a secure channel
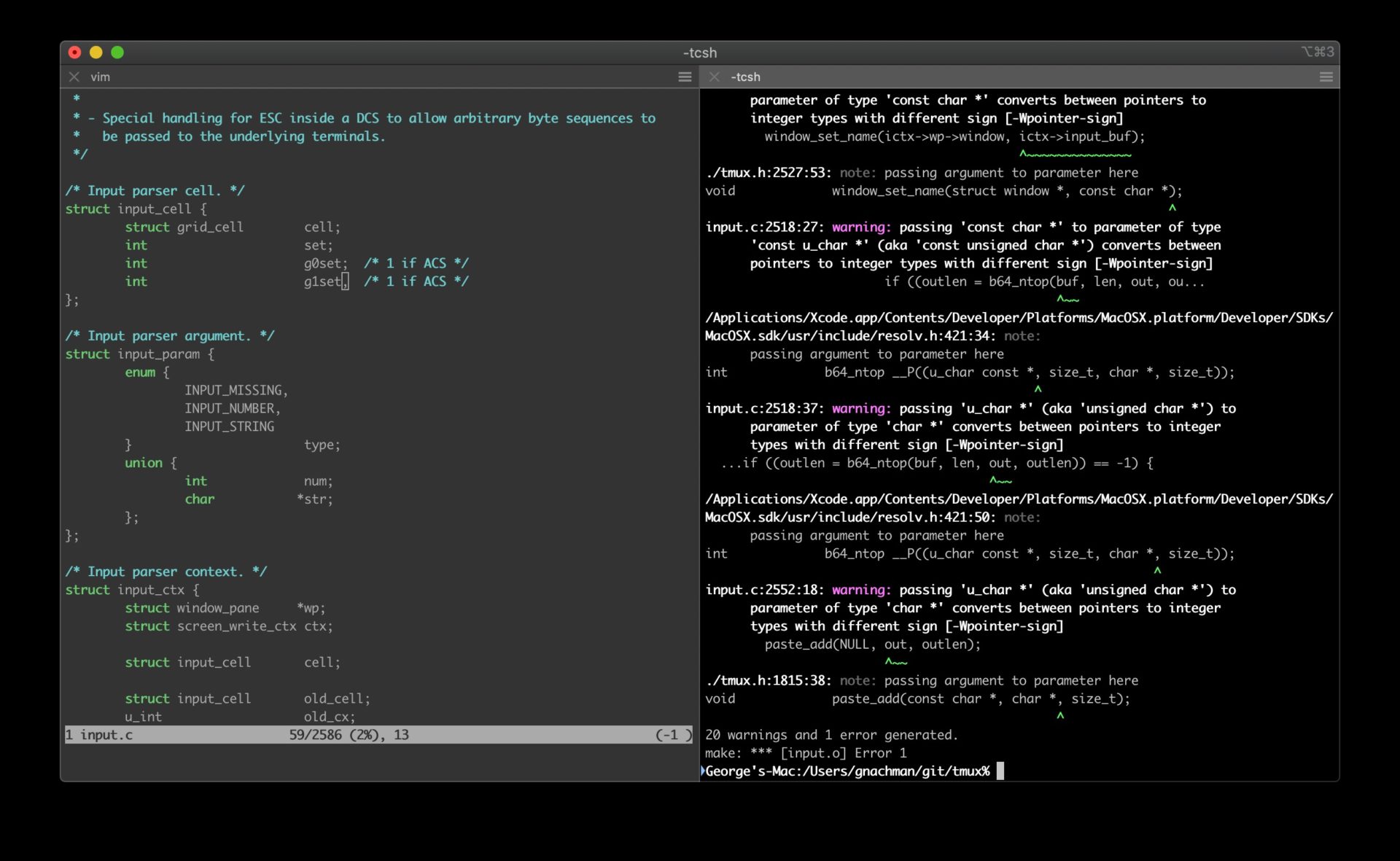
How SSH RemoteIoT Works
SSH RemoteIoT operates by establishing a secure connection between a client device and an IoT device. The process involves several steps:
Read also:Harry Connick Jr Family Pictures A Closer Look Into The Life Of The Beloved Musician
- Initiating the connection request
- Verifying the identity of the devices
- Establishing an encrypted communication channel
- Transferring data securely
Components of SSH RemoteIoT
SSH RemoteIoT consists of the following components:
- SSH client
- SSH server
- Encryption algorithms
- Authentication mechanisms
Benefits of Using SSH RemoteIoT
Adopting SSH RemoteIoT offers numerous benefits, including:
- Enhanced security
- Improved reliability
- Scalability
- Cost-effectiveness
These advantages make SSH RemoteIoT an attractive solution for organizations seeking to secure their IoT infrastructure.
Security Considerations for SSH RemoteIoT
While SSH provides robust security, it is essential to implement best practices to maximize its effectiveness. Some key considerations include:
- Using strong passwords and key-based authentication
- Regularly updating SSH software
- Monitoring for suspicious activity
- Implementing firewalls and intrusion detection systems
Common Security Threats
SSH RemoteIoT systems may face threats such as:
- Brute-force attacks
- Man-in-the-middle attacks
- Malware infections
Criteria for Selecting the Best SSH RemoteIoT
When choosing an SSH RemoteIoT solution, consider the following criteria:
- Security features
- Performance and reliability
- Compatibility with existing systems
- Cost and scalability
- Customer support and documentation
Evaluating Vendors
Research potential vendors thoroughly, reading reviews and case studies to ensure they meet your requirements. Look for vendors with a proven track record in delivering secure and reliable SSH RemoteIoT solutions.
Top SSH RemoteIoT Solutions
Several leading solutions are available in the market, each offering unique features and benefits:
- OpenSSH
- TunnelBear
- Cisco Secure Shell
- SSH.COM
Each solution caters to different needs, so it's important to evaluate them based on your specific requirements.
Comparing Features
When comparing SSH RemoteIoT solutions, consider the following features:
- Encryption algorithms
- Authentication methods
- Support for multiple platforms
- User interface and ease of use
Implementing SSH RemoteIoT
Successfully implementing SSH RemoteIoT requires careful planning and execution. Follow these steps to ensure a smooth deployment:
- Assess your requirements
- Select the appropriate solution
- Configure the SSH server and client
- Test the connection
- Monitor and maintain the system
Best Practices
To optimize your SSH RemoteIoT implementation, adhere to these best practices:
- Use strong encryption algorithms
- Implement multi-factor authentication
- Regularly back up configuration files
- Train users on security best practices
Troubleshooting Common Issues
Despite careful planning, issues may arise during the implementation and operation of SSH RemoteIoT. Common problems include:
- Connection failures
- Authentication errors
- Performance issues
Refer to the vendor's documentation and support resources to resolve these issues effectively.
The Future of SSH RemoteIoT
As technology continues to evolve, SSH RemoteIoT is expected to play an increasingly important role in securing IoT ecosystems. Advances in encryption algorithms, quantum computing, and artificial intelligence will further enhance the capabilities of SSH RemoteIoT, making it even more secure and efficient.
Trends to Watch
Keep an eye on emerging trends such as:
- Zero-trust architecture
- Quantum-resistant encryption
- AI-driven threat detection
Conclusion
SSH RemoteIoT represents a powerful solution for securing IoT ecosystems. By understanding its benefits, challenges, and implementation strategies, you can make informed decisions about adopting this technology. Remember to follow best practices and stay updated on the latest trends to ensure the security and reliability of your SSH RemoteIoT system.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into the world of technology and security. Together, let's build a safer and more connected future!