Remote management of IoT devices has become essential as more businesses and individuals adopt connected technologies. Best SSH RemoteIoT free solutions provide secure access to your IoT devices from anywhere, ensuring seamless control and monitoring. With the growing demand for remote connectivity, understanding SSH and its applications in IoT is crucial for tech enthusiasts and professionals alike.
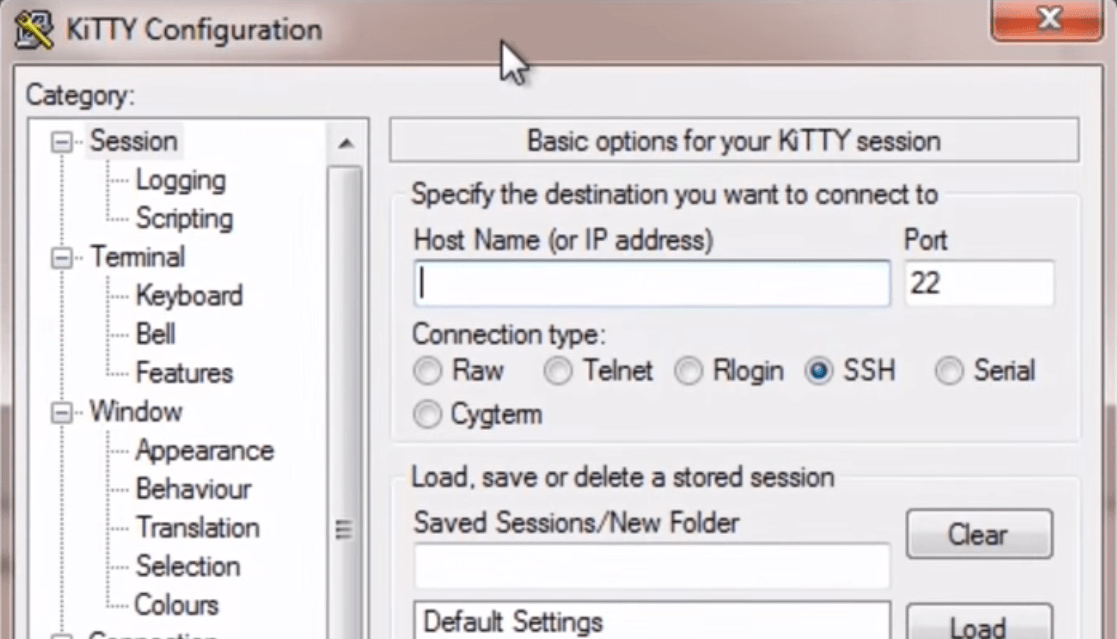
SSH (Secure Shell) has long been the gold standard for secure remote access to servers and devices. Combining SSH with IoT creates powerful opportunities for managing smart devices remotely. This article explores the best free SSH RemoteIoT options available today, helping you make informed decisions about secure connectivity.
Whether you're a developer experimenting with IoT projects or a business looking to enhance operational efficiency, free SSH RemoteIoT tools can transform how you interact with your devices. This guide will delve into the top solutions, their features, and how they can benefit your IoT setup.
Read also:Are Dr Phil And Robin Divorced Exploring The Truth Behind Their Relationship
Understanding SSH and Its Role in IoT
What is SSH?
SSH, or Secure Shell, is a network protocol designed to provide secure communication between devices over an unsecured network. Originally developed in 1995, SSH has become the go-to method for secure remote access to servers and devices. Its encryption capabilities ensure that data transmitted between devices remains private and tamper-proof.
SSH offers several key features that make it ideal for IoT applications:
- Encryption: SSH uses strong encryption algorithms to protect data in transit.
- Authentication: It supports various authentication methods, including passwords and public key infrastructure (PKI).
- Port Forwarding: SSH allows secure tunneling of other protocols through its encrypted connection.
- File Transfer: Secure Copy Protocol (SCP) and Secure File Transfer Protocol (SFTP) are built on top of SSH for secure file transfers.
Why SSH is Essential for IoT
As IoT devices become more prevalent, securing their communication becomes increasingly important. SSH provides a robust solution for managing IoT devices remotely while maintaining data integrity and confidentiality. According to a report by Gartner, the number of IoT devices is expected to reach 25 billion by 2030, making secure remote management a critical priority.
SSH addresses common IoT security challenges by:
- Providing end-to-end encryption for device communication.
- Ensuring secure authentication for device access.
- Facilitating secure firmware updates and configuration changes.
- Offering audit trails for device access and modifications.
Top Free SSH RemoteIoT Solutions
1. OpenSSH
OpenSSH is the most widely used SSH implementation, available for multiple platforms including Linux, macOS, and Windows. It provides a comprehensive suite of tools for secure remote access and management. OpenSSH's open-source nature makes it highly customizable and suitable for IoT applications.
Key features:
Read also:Simon Cowell Car Accident 2025 A Comprehensive Overview
- Supports multiple encryption algorithms.
- Includes tools for secure file transfer (scp, sftp).
- Provides extensive configuration options.
- Offers strong community support and frequent updates.
2. Dropbear SSH
Dropbear is a lightweight SSH server and client designed for embedded systems and resource-constrained environments. Its small footprint makes it ideal for IoT devices with limited processing power and memory.
Benefits of Dropbear:
- Minimal resource requirements.
- Supports both SSHv1 and SSHv2 protocols.
- Includes public key authentication.
- Compatible with various embedded platforms.
3. BearSSL
BearSSL is another lightweight SSH implementation designed specifically for embedded systems. It focuses on providing secure communication while maintaining minimal resource usage, making it perfect for IoT applications.
Features:
- Optimized for embedded environments.
- Supports modern encryption algorithms.
- Provides secure key exchange mechanisms.
- Includes comprehensive documentation.
Selecting the Right SSH RemoteIoT Solution
Factors to Consider
Choosing the best SSH RemoteIoT free solution requires evaluating several key factors:
- Device Compatibility: Ensure the solution supports your specific IoT hardware and operating system.
- Resource Requirements: Consider the processing power and memory available on your IoT devices.
- Security Features: Evaluate the encryption algorithms and authentication methods supported.
- Community Support: Look for solutions with active user communities and frequent updates.
Use Cases
Different SSH RemoteIoT solutions are better suited for specific use cases:
- Industrial IoT: OpenSSH provides robust security and scalability for large-scale deployments.
- Smart Home Devices: Dropbear offers lightweight capabilities ideal for home automation systems.
- Embedded Systems: BearSSL excels in resource-constrained environments requiring minimal footprint.
Implementing SSH for IoT Security
Best Practices
Implementing SSH for IoT security involves following best practices to ensure maximum protection:
- Use strong, unique passwords or public key authentication.
- Disable password authentication if using public key infrastructure.
- Regularly update SSH software to patch security vulnerabilities.
- Monitor access logs for unauthorized login attempts.
Common Pitfalls to Avoid
When implementing SSH for IoT, avoid common mistakes that can compromise security:
- Using default passwords or weak credentials.
- Leaving unnecessary services running on IoT devices.
- Failing to update SSH software regularly.
- Ignoring access logs and audit trails.
Performance Optimization for SSH RemoteIoT
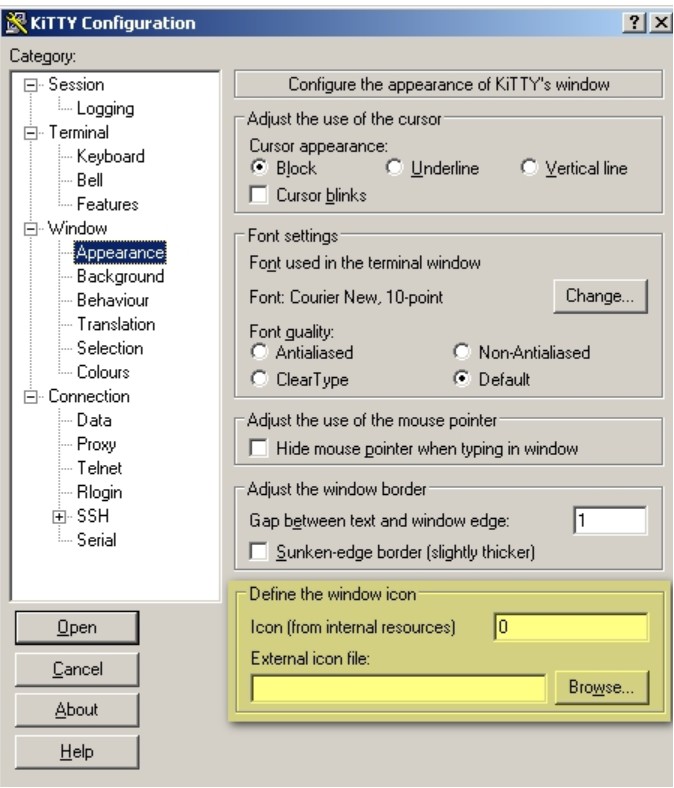
Tuning SSH Configuration
Optimizing SSH performance for IoT involves tweaking configuration settings:
- Adjust cipher preferences for faster encryption.
- Limit maximum session duration to prevent prolonged connections.
- Enable compression for slower network connections.
- Set idle timeout intervals to automatically disconnect inactive sessions.
Resource Management
Managing resources effectively is crucial for IoT devices with limited capabilities:
- Monitor CPU and memory usage during SSH sessions.
- Limit concurrent connections to prevent resource exhaustion.
- Implement connection limits based on device capabilities.
- Use lightweight SSH implementations when necessary.
Future Trends in SSH RemoteIoT
Emerging Technologies
Several emerging technologies are shaping the future of SSH RemoteIoT:
- Quantum-resistant encryption algorithms.
- Artificial intelligence-driven threat detection.
- Blockchain-based authentication mechanisms.
- Edge computing for localized processing.
Industry Developments
The IoT industry continues to evolve, driving innovation in SSH RemoteIoT solutions:
- Increased focus on zero-trust architecture.
- Development of IoT-specific security standards.
- Integration with cloud-based management platforms.
- Adoption of machine learning for anomaly detection.
Conclusion
The best SSH RemoteIoT free solutions provide secure, reliable access to IoT devices while maintaining performance and resource efficiency. By understanding the capabilities of OpenSSH, Dropbear, and BearSSL, you can select the ideal solution for your specific needs. Implementing SSH best practices and following optimization techniques will ensure maximum security and performance for your IoT setup.
We invite you to share your experiences with SSH RemoteIoT solutions in the comments section below. Your feedback helps us improve our content and provides valuable insights for other readers. For more information on IoT security and management, explore our other articles covering related topics.
Table of Contents
- Understanding SSH and Its Role in IoT
- Top Free SSH RemoteIoT Solutions
- Selecting the Right SSH RemoteIoT Solution
- Implementing SSH for IoT Security
- Performance Optimization for SSH RemoteIoT