With the increasing reliance on IoT (Internet of Things) devices, remotely accessing and managing them has become more critical than ever. Whether you're a network administrator, hobbyist, or tech enthusiast, understanding how to SSH (Secure Shell) into IoT devices remotely from your Android device can significantly enhance your control over smart systems. This guide will walk you through the process step-by-step, ensuring security, efficiency, and ease of use.
Remote access to IoT devices via SSH allows you to manage configurations, troubleshoot issues, and monitor performance without being physically present. This method is especially beneficial for individuals or businesses managing multiple IoT devices spread across different locations.
However, it's essential to approach remote SSH connections with caution, as IoT devices are often vulnerable to cyber threats. This article aims to equip you with the knowledge and tools to securely access IoT devices remotely using your Android device, ensuring your network remains protected.
Read also:Discover The Enigma Of Abandoned Houses In Puerto Rico
Table of Contents
- Introduction to SSH
- IoT Devices Overview
- Why SSH is Important for IoT Devices
- Tools You Need
- Step-by-Step Guide to SSH into IoT Devices
- Securing Your SSH Connection
- Common Issues and Troubleshooting
- Advanced Techniques for Remote Access
- Best Practices for SSH IoT Device Remotely
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol used to securely operate network services over an unsecured network. It provides strong authentication and encrypted data communications between two computers, ensuring that sensitive information remains protected during transmission.
SSH is widely used in remote server management, file transfers, and network operations. When it comes to IoT devices, SSH offers a secure way to interact with these devices remotely, allowing users to execute commands, transfer files, and monitor device performance.
History and Development of SSH
Developed in 1995 by Tatu Ylönen, SSH was designed as a replacement for less secure protocols like Telnet and rlogin. Over the years, SSH has evolved into a robust tool for secure communication, with its latest version, SSH-2, being widely adopted across various platforms.
Understanding the history and development of SSH helps users appreciate its importance in modern networking, especially in the context of IoT devices.
IoT Devices Overview
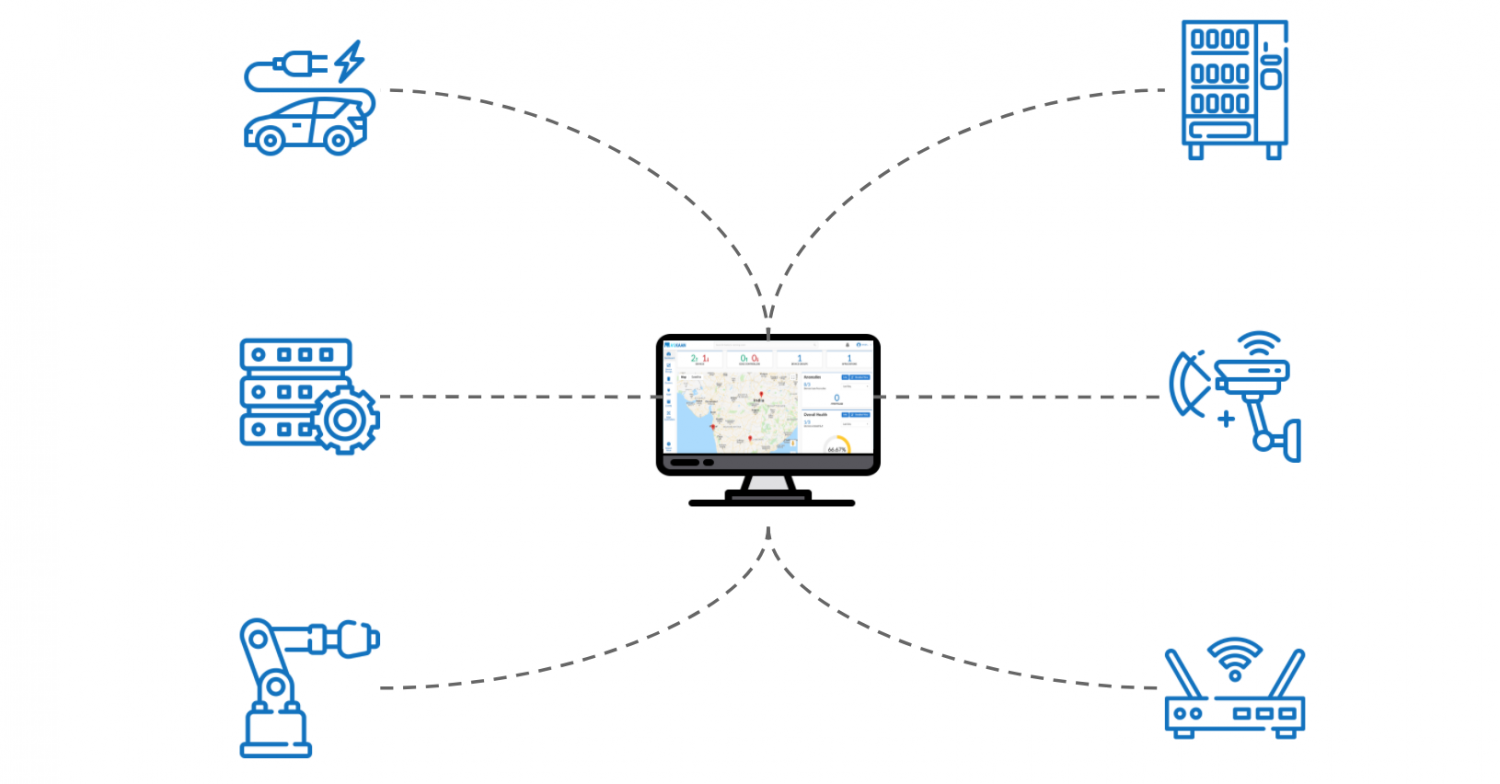
IoT devices encompass a wide range of smart gadgets, from home automation systems to industrial sensors. These devices are interconnected through the internet, allowing them to communicate and exchange data seamlessly.
Some common examples of IoT devices include smart thermostats, security cameras, smart locks, and industrial sensors. Each of these devices requires remote management and monitoring to ensure optimal performance and security.
Read also:Ron Jeremy Jail The Untold Story And Legal Journey
Types of IoT Devices
- Consumer IoT: Devices used in homes, such as smart speakers, smart lights, and wearables.
- Enterprise IoT: Devices used in businesses, including inventory trackers and smart office equipment.
- Industrial IoT: Devices used in manufacturing and industrial settings, such as sensors and automated machinery.
Understanding the types of IoT devices you are working with is crucial for determining the best approach to SSH remote access.
Why SSH is Important for IoT Devices
SSH plays a vital role in securing IoT devices, especially when accessed remotely. Unlike other protocols, SSH encrypts all data transmitted between the client and server, making it nearly impossible for unauthorized parties to intercept sensitive information.
Moreover, SSH provides strong authentication mechanisms, ensuring that only authorized users can access the IoT devices. This is particularly important in environments where security breaches can have severe consequences.
Security Benefits of SSH
- Data encryption during transmission.
- Strong user authentication.
- Protection against man-in-the-middle attacks.
These security benefits make SSH an ideal choice for managing IoT devices remotely, ensuring both data integrity and confidentiality.
Tools You Need
To SSH into IoT devices remotely from your Android device, you will need a few essential tools. These tools will help you establish a secure connection and manage your IoT devices efficiently.
SSH Clients for Android
- Termius: A popular SSH client for Android, offering a user-friendly interface and robust features.
- JuiceSSH: Another reliable SSH client with support for multiple sessions and customizable themes.
- ConnectBot: An open-source SSH client that provides advanced features like port forwarding and public key authentication.
Choosing the right SSH client depends on your specific needs and preferences. It's recommended to try out a few options to find the one that suits you best.
Step-by-Step Guide to SSH into IoT Devices
Now that you have the necessary tools, let's dive into the step-by-step process of SSHing into IoT devices remotely from your Android device.
Step 1: Install an SSH Client
Download and install an SSH client from the Google Play Store. Popular options include Termius, JuiceSSH, and ConnectBot.
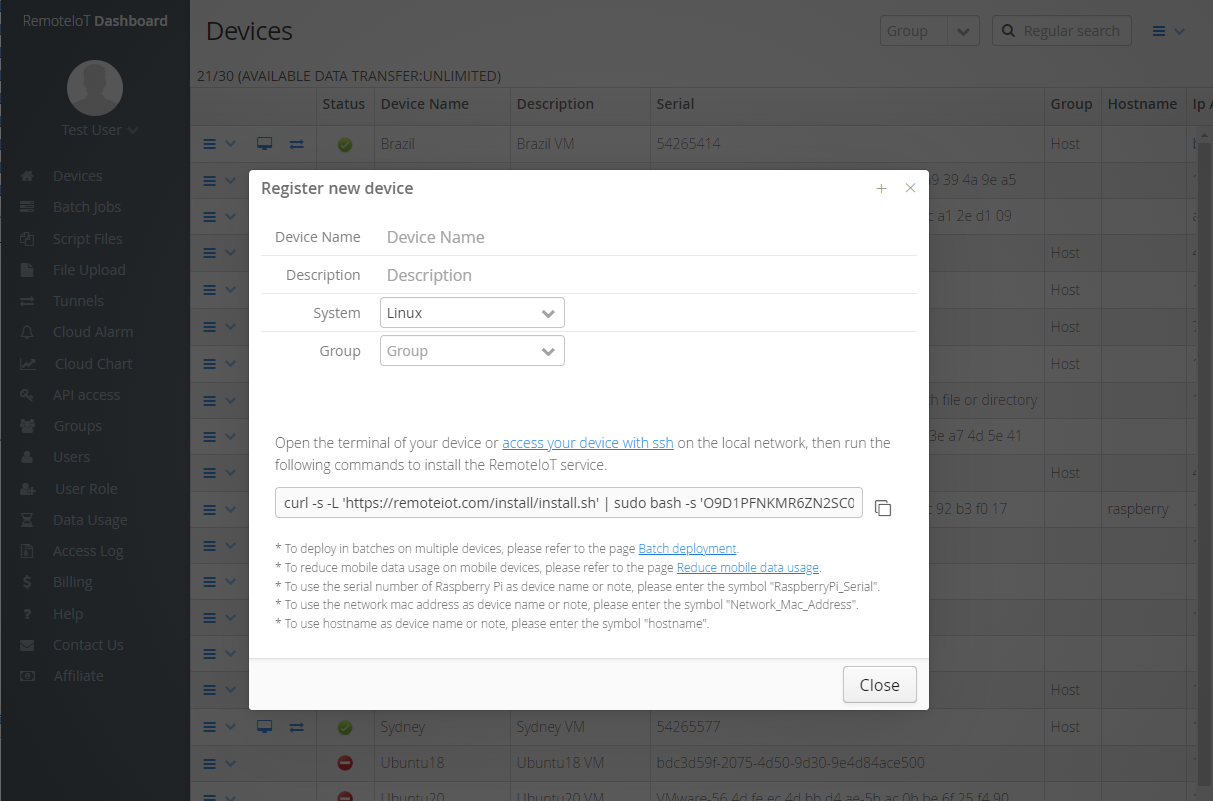
Step 2: Configure the IoT Device
Ensure that the IoT device is set up to accept SSH connections. This typically involves enabling the SSH service and configuring the necessary settings.
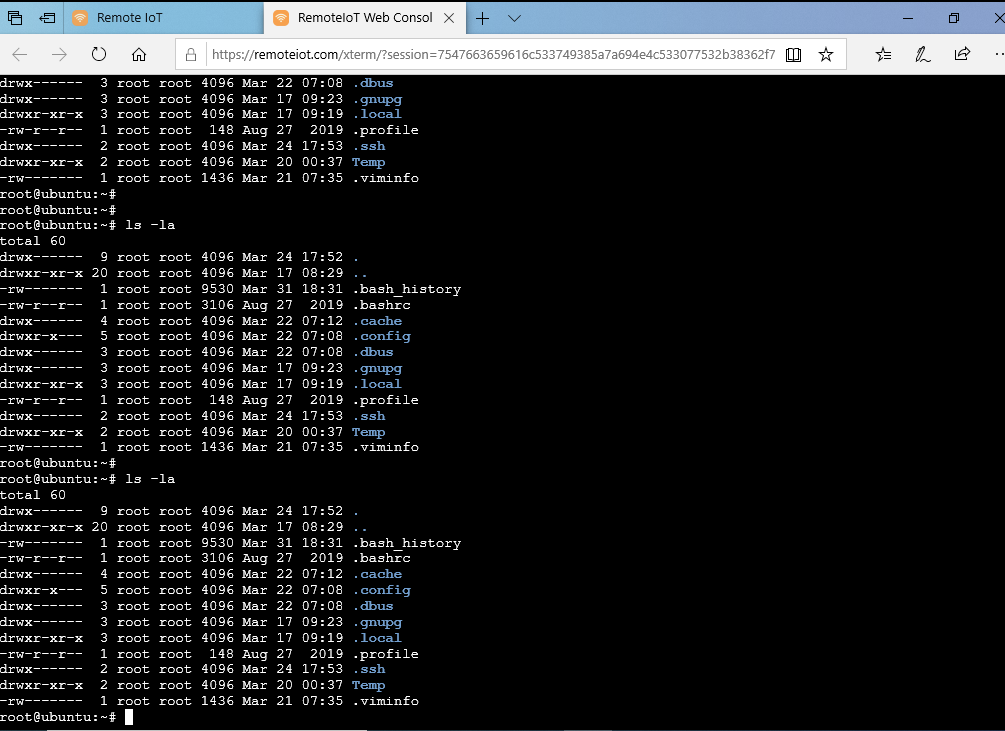
Step 3: Connect to the IoT Device
Using your SSH client, enter the IP address or hostname of the IoT device, along with the appropriate username and password. Once connected, you can start managing the device remotely.
Securing Your SSH Connection
While SSH provides a secure method for remote access, it's essential to take additional steps to enhance the security of your connections. This includes using strong passwords, enabling two-factor authentication, and regularly updating your SSH client and IoT device firmware.
Best Security Practices
- Use strong, unique passwords for each device.
- Enable two-factor authentication whenever possible.
- Keep your SSH client and IoT device firmware up to date.
Implementing these practices will significantly reduce the risk of unauthorized access and ensure the security of your IoT devices.
Common Issues and Troubleshooting
Even with the best tools and practices, issues can arise when SSHing into IoT devices. Common problems include connection timeouts, authentication failures, and configuration errors.
Troubleshooting Tips
- Check the IP address and port number to ensure they are correct.
- Verify that the SSH service is running on the IoT device.
- Ensure that firewalls or network settings are not blocking the connection.
By following these troubleshooting tips, you can quickly resolve most issues and maintain a stable SSH connection to your IoT devices.
Advanced Techniques for Remote Access
For users looking to enhance their SSH experience, there are several advanced techniques to consider. These include setting up port forwarding, using SSH tunnels, and automating tasks with scripts.
Port Forwarding
Port forwarding allows you to securely access services running on your IoT device from a remote location. This is particularly useful for accessing web interfaces or other services that are not directly exposed to the internet.
SSH Tunnels
SSH tunnels provide an encrypted connection between your Android device and the IoT device, ensuring that all data transmitted remains secure. This technique is especially beneficial when accessing sensitive information or managing critical systems.
Best Practices for SSH IoT Device Remotely
To ensure a smooth and secure SSH experience, it's essential to follow best practices. These include regularly monitoring your IoT devices, keeping software up to date, and documenting your configurations.
Regular Monitoring
Regularly monitoring your IoT devices can help you identify potential issues before they become serious problems. This includes checking logs, monitoring performance metrics, and ensuring that all devices are functioning as expected.
Documentation
Keeping detailed documentation of your configurations and procedures can save time and effort when troubleshooting or onboarding new team members. This documentation should include IP addresses, usernames, passwords, and any specific settings or configurations used.
Conclusion
In conclusion, SSHing into IoT devices remotely from your Android device is a powerful tool for managing and monitoring smart systems. By following the steps outlined in this guide, you can establish secure connections, troubleshoot common issues, and implement advanced techniques to enhance your experience.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and networking technologies.
Remember, securing your IoT devices is crucial in today's interconnected world. Stay informed, stay secure, and enjoy the convenience of remote management with SSH.